https://www.amazon.com/Voice-Desert-Valerio-Stefano-ebook/dp/B0CJLZ2QY5/
SITEMAP
Make a donation: IBAN: IT36M0708677020000000008016 - BIC/SWIFT: ICRAITRRU60 - VALERIO DI STEFANO or
Privacy Policy Cookie Policy Terms and Conditions
Deployment Guide
Deployment, Configuration and Administration of Red Hat Enterprise Linux 6
Edition 1
Legal Notice
1801 Varsity Drive
Raleigh, NC 27606-2072 USA
Phone: +1 919 754 3700
Phone: 888 733 4281
Fax: +1 919 754 3701
Abstract
- Preface
- Introduction
- I. Package Management
- 1. Yum
- 2. PackageKit
- 3. RPM
- II. Network-Related Configuration
- 4. Network Interfaces
- 5. Network Configuration
- 6. Dynamic Host Configuration Protocol (DHCP)
- 7. Controlling Access to Services
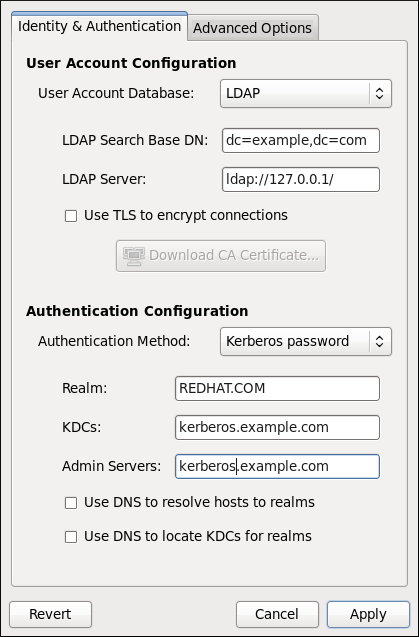
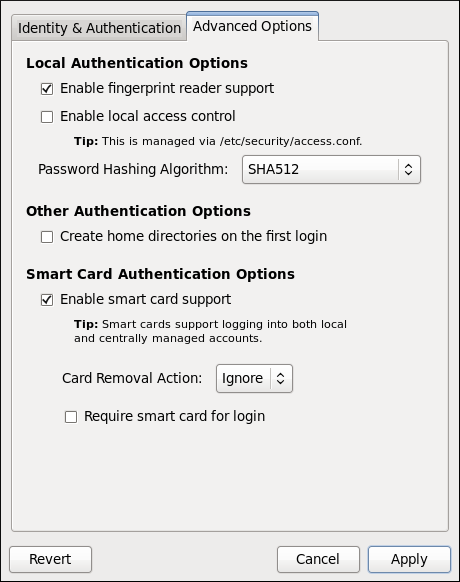
- 8. Authentication Configuration
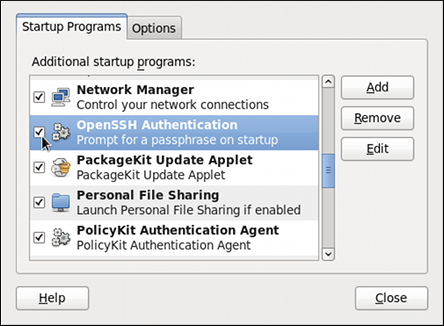
- 9. OpenSSH
- 10. The BIND DNS Server
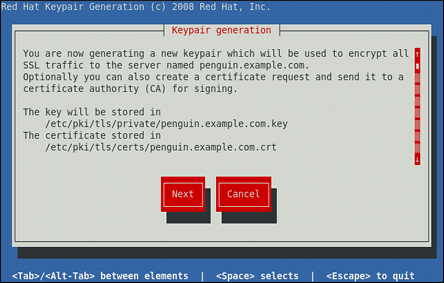
- 11. The Apache HTTP Server
- 12. Email
- III. System Configuration
- 13. Date and Time Configuration
- 14. Keyboard Configuration
- 15. Users and Groups
- 16. Automated Tasks
- 17. Log Files
- 18. The sysconfig Directory
- 18.1. Files in the
/etc/sysconfig/Directory - 18.1.1.
/etc/sysconfig/arpwatch - 18.1.2.
/etc/sysconfig/authconfig - 18.1.3.
/etc/sysconfig/autofs - 18.1.4.
/etc/sysconfig/clock - 18.1.5.
/etc/sysconfig/dhcpd - 18.1.6.
/etc/sysconfig/firstboot - 18.1.7.
/etc/sysconfig/i18n - 18.1.8.
/etc/sysconfig/init - 18.1.9.
/etc/sysconfig/ip6tables-config - 18.1.10.
/etc/sysconfig/keyboard - 18.1.11.
/etc/sysconfig/ldap - 18.1.12.
/etc/sysconfig/named - 18.1.13.
/etc/sysconfig/network - 18.1.14.
/etc/sysconfig/ntpd - 18.1.15.
/etc/sysconfig/quagga - 18.1.16.
/etc/sysconfig/radvd - 18.1.17.
/etc/sysconfig/samba - 18.1.18.
/etc/sysconfig/selinux - 18.1.19.
/etc/sysconfig/sendmail - 18.1.20.
/etc/sysconfig/spamassassin - 18.1.21.
/etc/sysconfig/squid - 18.1.22.
/etc/sysconfig/system-config-users - 18.1.23.
/etc/sysconfig/vncservers - 18.1.24.
/etc/sysconfig/xinetd
- 18.1.1.
- 18.2. Directories in the
/etc/sysconfig/Directory - 18.3. Additional Resources
- 18.1. Files in the
- 19. The
procFile System - 19.1. A Virtual File System
- 19.2. Top-level Files within the
procFile System - 19.2.1.
/proc/buddyinfo - 19.2.2.
/proc/cmdline - 19.2.3.
/proc/cpuinfo - 19.2.4.
/proc/crypto - 19.2.5.
/proc/devices - 19.2.6.
/proc/dma - 19.2.7.
/proc/execdomains - 19.2.8.
/proc/fb - 19.2.9.
/proc/filesystems - 19.2.10.
/proc/interrupts - 19.2.11.
/proc/iomem - 19.2.12.
/proc/ioports - 19.2.13.
/proc/kcore - 19.2.14.
/proc/kmsg - 19.2.15.
/proc/loadavg - 19.2.16.
/proc/locks - 19.2.17.
/proc/mdstat - 19.2.18.
/proc/meminfo - 19.2.19.
/proc/misc - 19.2.20.
/proc/modules - 19.2.21.
/proc/mounts - 19.2.22.
/proc/mtrr - 19.2.23.
/proc/partitions - 19.2.24.
/proc/slabinfo - 19.2.25.
/proc/stat - 19.2.26.
/proc/swaps - 19.2.27.
/proc/sysrq-trigger - 19.2.28.
/proc/uptime - 19.2.29.
/proc/version
- 19.2.1.
- 19.3. Directories within
/proc/ - 19.4. Using the
sysctlCommand - 19.5. References
- IV. System Monitoring
- V. Kernel, Module and Driver Configuration
- 22. Working with Kernel Modules
- 23. Manually Upgrading the Kernel
- 24. The
kdumpCrash Recovery Service
- A. Revision History
- Index
Preface
1. Document Conventions
1.1. Typographic Conventions
Mono-spaced Bold
To see the contents of the filemy_next_bestselling_novelin your current working directory, enter thecat my_next_bestselling_novelcommand at the shell prompt and press Enter to execute the command.
Press Enter to execute the command.Press Ctrl+Alt+F2 to switch to the first virtual terminal. Press Ctrl+Alt+F1 to return to your X-Windows session.
mono-spaced bold. For example:
File-related classes includefilesystemfor file systems,filefor files, anddirfor directories. Each class has its own associated set of permissions.
Choose → → from the main menu bar to launch Mouse Preferences. In the Buttons tab, click the Left-handed mouse check box and click to switch the primary mouse button from the left to the right (making the mouse suitable for use in the left hand).To insert a special character into a gedit file, choose → → from the main menu bar. Next, choose → from the Character Map menu bar, type the name of the character in the Search field and click . The character you sought will be highlighted in the Character Table. Double-click this highlighted character to place it in the Text to copy field and then click the button. Now switch back to your document and choose → from the gedit menu bar.
Mono-spaced Bold ItalicProportional Bold Italic
To connect to a remote machine using ssh, typesshat a shell prompt. If the remote machine isusername@domain.nameexample.comand your username on that machine is john, typessh john@example.com.Themount -o remountcommand remounts the named file system. For example, to remount thefile-system/homefile system, the command ismount -o remount /home.To see the version of a currently installed package, use therpm -qcommand. It will return a result as follows:package.package-version-release
Publican is a DocBook publishing system.
1.2. Pull-quote Conventions
mono-spaced roman and presented thus:
books Desktop documentation drafts mss photos stuff svn books_tests Desktop1 downloads images notes scripts svgs
mono-spaced roman but add syntax highlighting as follows:
package org.jboss.book.jca.ex1; import javax.naming.InitialContext; public class ExClient { public static void main(String args[]) throws Exception { InitialContext iniCtx = new InitialContext(); Object ref = iniCtx.lookup("EchoBean"); EchoHome home = (EchoHome) ref; Echo echo = home.create(); System.out.println("Created Echo"); System.out.println("Echo.echo('Hello') = " + echo.echo("Hello")); } }
1.3. Notes and Warnings
Note
Important
Warning
2. We Need Feedback!
6.
2.1. Technical Review Requests
- New Content
- content documented for the first time — an entirely new feature, procedure, or concept. For example: "Section now describes the new procedure for creating bootable USB devices."
- Correction
- a factual error previously present in the text has been corrected. For example: "Section previously stated (incorrectly) that IPv4 and IPv6 were both supported; section now states that IPv6 has never been supported."
- Clarification
- material that was already factually correct but is now better explained. Clarifications are usually in response to reader feedback that the previous content was confusing or misleading in some way. For example: "Paths described in Example 1.2.3 now better reflect the directory structure of an actual installed system."
- Obsoletion
- a description of a feature or a procedure has been dropped. Material might be obsolete because of a feature that is no longer supported, a known issue that has been corrected, or hardware that is now obsolete. For example, "Section no longer describes how to update kernel modules using a floppy disk."
- Verification
- a request to check a fact, procedure, or whether material should be obsoleted. For example, "Section describes how to connect to a generic iSCSI storage device. Please verify this on your hardware" or "Section still describes how to update kernel modules using a LS-120 SuperDisk; please verify that we still need to tell readers about this obsolete hardware."
3. Acknowledgements
Introduction
- Installing and managing packages using the graphical PackageKit and command line Yum package managers
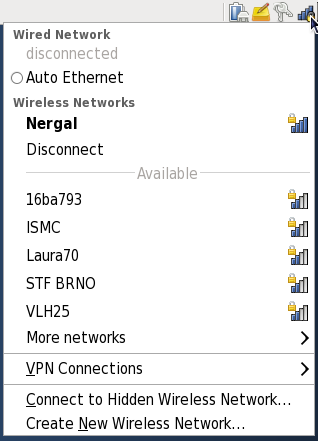
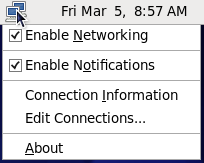
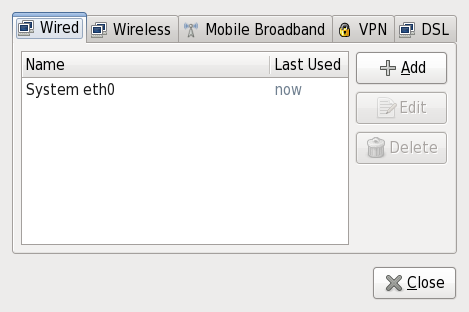
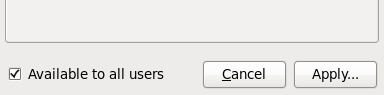
- Setting up a network—from establishing an Ethernet connection using NetworkManager to configuring channel bonding interfaces to increase server bandwidth
- Configuring
DHCP, BIND, Apache, Postfix, Sendmail and other enterprise-class servers and software - Gathering information about your system, including obtaining user-space crash data with the Automatic Bug Reporting Tool, and kernel-space crash data with
kdump - Easily working with kernel modules and upgrading the kernel
Part I. Package Management
Table of Contents
- 1. Yum
- 2. PackageKit
- 3. RPM
Chapter 1. Yum
Secure Package Management with GPG-Signed Packages
1.1. Checking For and Updating Packages
1.1.1. Checking For Updates
yum check-update command to see which installed packages on your system have updates available.
Note: Yum and Superuser Privileges
yum
to install, update or remove packages on your system. All examples in
this chapter assume that you have already obtained superuser privileges
by using either the su or sudo command.
~]# yum check-update
Loaded plugins: presto, refresh-packagekit, security
PackageKit.x86_64 0.5.8-2.el6 rhel
PackageKit-glib.x86_64 0.5.8-2.el6 rhel
PackageKit-yum.x86_64 0.5.8-2.el6 rhel
PackageKit-yum-plugin.x86_64 0.5.8-2.el6 rhel
glibc.x86_64 2.11.90-20.el6 rhel
glibc-common.x86_64 2.10.90-22 rhel
kernel.x86_64 2.6.31-14.el6 rhel
kernel-firmware.noarch 2.6.31-14.el6 rhel
rpm.x86_64 4.7.1-5.el6 rhel
rpm-libs.x86_64 4.7.1-5.el6 rhel
rpm-python.x86_64 4.7.1-5.el6 rhel
udev.x86_64 147-2.15.el6 rhel
yum.noarch 3.2.24-4.el6 rhel
PackageKit— the name of the packagex86_64— the CPU architecture the package was built for0.5.8— the version of the updated package to be installedrhel— the repository in which the updated package is located
yum and rpm packages), as well as their dependencies (such as the kernel-firmware, rpm-libs and rpm-python packages), all using yum.
1.1.2. Updating Packages
yum update <package_name>:
~]# yum update udev
Loaded plugins: presto, refresh-packagekit, rhnplugin, security
Setting up Update Process
Resolving Dependencies
--> Running transaction check
---> Package udev.x86_64 0:147-2.15.el6 set to be updated
--> Finished Dependency Resolution
Dependencies Resolved
===========================================================================
Package Arch Version Repository Size
===========================================================================
Updating:
udev x86_64 147-2.15.el6 rhel 337 k
Transaction Summary
===========================================================================
Install 0 Package(s)
Upgrade 1 Package(s)
Total download size: 337 k
Is this ok [y/N]:
Loaded plugins: presto, refresh-packagekit, security—yumalways informs you which Yum plugins are installed and enabled. Here,yumis using the presto, refresh-packagekit and security plugins. Refer to Section 1.4, “Yum Plugins” for general information on Yum plugins, or to Section 1.4.3, “Plugin Descriptions” for descriptions of specific plugins.kernel.x86_64— you can download and install new kernels safely withyum.Important: Updating and Installing Kernels with Yum
yumalways installs a new kernel in the same sense that RPM installs a new kernel when you use the commandrpm -i kernel. Therefore, you do not need to worry about the distinction between installing and upgrading a kernel package when you useyum: it will do the right thing, regardless of whether you are using theyum updateoryum installcommand.When using RPM, on the other hand, it is important to use therpm -i kernelcommand (which installs a new kernel) instead ofrpm -u kernel(which replaces the current kernel). Refer to Section 3.2.2, “Installing and Upgrading” for more information on installing/updating kernels with RPM.yumpresents the update information and then prompts you as to whether you want it to perform the update;yumruns interactively by default. If you already know which transactionsyumplans to perform, you can use the-yoption to automatically answeryesto any questionsyummay ask (in which case it runs non-interactively). However, you should always examine which changesyumplans to make to the system so that you can easily troubleshoot any problems that might arise.If a transaction does go awry, you can view Yum's log of transactions by enteringcat /var/log/yum.logat the shell prompt. The most recent transactions are listed at the end of the log file.
Updating All Packages and Their Dependencies
yum update (without any arguments):
Example 1.1. Updating all packages at once
~]# yum update1.1.3. Updating Security-Related Packages
yum command with a set of highly-useful security-centric commands, subcommands and options. Refer to Section 1.4.3, “security (yum-plugin-security)” for specific information.
1.1.4. Preserving Configuration File Changes
1.2. Packages and Package Groups
1.2.1. Searching, Listing and Displaying Package Information
yum search <term> [more_terms] command. yum displays the list of matches for each term:
~]# yum search meld kompare
Loaded plugins: presto, refresh-packagekit, rhnplugin, security
============================ Matched: kompare =============================
kdesdk.x86_64 : The KDE Software Development Kit (SDK)
Warning: No matches found for: meld
yum search is useful for searching for packages you do not know the name of, but for which you know a related term.
Listing Packages
Tip: Filtering Results with Glob Expressions
* (which expands to match any character multiple times) and ?
(which expands to match any one character). Be careful to escape both
of these glob characters when passing them as arguments to a yum command. If you do not, the bash shell will interpret the glob expressions as pathname expansions, and potentially pass all files in the current directory that match the globs to yum, which is not what you want. Instead, you want to pass the glob expressions themselves to yum, which you can do by either:
- escaping the wildcard characters
- double-quoting or single-quoting the entire glob expression.
Example 1.2. Filtering results using a single glob expression with two escaped wildcard characters
~]# yum list available gstreamer\*plugin\*
Loaded plugins: presto, refresh-packagekit, rhnplugin, security
Available Packages
gstreamer-plugins-bad-free.i686 0.10.17-4.el6 rhel
gstreamer-plugins-base.i686 0.10.26-1.el6 rhel
gstreamer-plugins-base-devel.i686 0.10.26-1.el6 rhel
gstreamer-plugins-base-devel.x86_64 0.10.26-1.el6 rhel
gstreamer-plugins-good.i686 0.10.18-1.el6 rhel
Example 1.3. Filtering results using a double-quoted glob expression
~]# yum list installed "krb?-*"
Loaded plugins: presto, refresh-packagekit, rhnplugin, security
Installed Packages
krb5-libs.x86_64 1.8.1-3.el6 @rhel
krb5-workstation.x86_64 1.8.1-3.el6 @rhel
yum list— List information on installed and available packages matching all glob expressions.<glob_expr>[more_glob_exprs]Example 1.4. Listing all ABRT addons and plugins using glob expressions
~]#
yum list abrt-addon\* abrt-plugin\*Loaded plugins: presto, refresh-packagekit, rhnplugin, security Installed Packages abrt-addon-ccpp.x86_64 1.0.7-5.el6 @rhel abrt-addon-kerneloops.x86_64 1.0.7-5.el6 @rhel abrt-addon-python.x86_64 1.0.7-5.el6 @rhel abrt-plugin-bugzilla.x86_64 1.0.7-5.el6 @rhel abrt-plugin-logger.x86_64 1.0.7-5.el6 @rhel abrt-plugin-sosreport.x86_64 1.0.7-5.el6 @rhel abrt-plugin-ticketuploader.x86_64 1.0.7-5.el6 @rhel
Displaying Package Info
yum info <package_name> [more_names]
displays information about one or more packages (glob expressions are valid here as well):
~]# yum info abrt
Loaded plugins: presto, refresh-packagekit, rhnplugin, security
Installed Packages
Name : abrt
Arch : x86_64
Version : 1.0.7
Release : 5.el6
Size : 578 k
Repo : installed
From repo : rhel
Summary : Automatic bug detection and reporting tool
URL : https://fedorahosted.org/abrt/
License : GPLv2+
Description: abrt is a tool to help users to detect defects in applications
: and to create a bug report with all informations needed by
: maintainer to fix it. It uses plugin system to extend its
: functionality.
yum info <package_name> is similar to the rpm -q --info <package_name> command, but provides as additional information the ID of the Yum repository the RPM package is found in (look for the From repo: line in the output).
yumdb info <package_name> [more_names] can be used to query the Yum
database for alternative and useful information about a package,
including the checksum of the package (and algorithm used to produce it,
such as SHA-256), the command given on the command line that was
invoked to install the package (if any), and the reason that the package
is installed on the system (where user indicates it was installed by the user, and dep means it was brought in as a dependency):
~]# yumdb info yum
yum-3.2.27-4.el6.noarch
checksum_data = 15c8eaf583fabad6974a35b9f6c6527e49362fe4e23baec1682ef51a598e4abb
checksum_type = sha256
command_line = update
from_repo = rhel
from_repo_revision = 1271991599
from_repo_timestamp = 1271991721
reason = user
releasever = 6man yumdb for more information on the yumdb command.
yum history command, which is new in Red Hat Enterprise Linux 6, can be used to show a timeline of Yum
transactions, the dates and times on when they occurred, the number of
packages affected, whether transactions succeeded or were aborted, and
if the RPM database was changed between transactions. Refer to the history section of man yum for details.
1.2.2. Installing
~]# yum install <package_name> yum install <package_name> [more_names] .
.arch to the package name:
~]# yum install sqlite2.i586~]# yum install audacious-plugins-\*yum install. If you know the name of the binary you want to install, but not its package name, you can give yum install the path name:
~]# yum install /usr/sbin/namedyum then searches through its package
lists, finds the package which provides /usr/sbin/named, if any, and
prompts you as to whether you want to install it.
named binary, but don't know in which bin or sbin directory that file lives? In that situation, you can give yum provides a glob expression:
Example 1.5. Finding which package owns a file and installing it
~]#yum provides "*bin/named"Loaded plugins: presto, refresh-packagekit, rhnplugin, security 32:bind-9.7.0-4.P1.el6.x86_64 : The Berkeley Internet Name Domain (BIND) : DNS (Domain Name System) server Repo : rhel Matched from: Filename : /usr/sbin/named ~]#yum install bind
Note
yum provides is the same as yum whatprovides.
Tip: yum provides/whatprovides and Glob Expressions
yum provides "*/<file_name>" is a common and useful trick to quickly find the package(s) that contain <file_name>.
Installing a Package Group
yum grouplist -v command lists the names of all package groups, and, next to each of them, their groupid in parentheses. The groupid is always the term in the last pair of parentheses, such as kde-desktop and kde-software-development in this example:
Not all packages used in examples may be available on RHN
~]# yum -v grouplist kde\*
KDE (K Desktop Environment) (kde-desktop)
KDE Software Development (kde-software-development)
groupinstall:
~]# yum groupinstall "KDE (K Desktop Environment)"~]# yum groupinstall kde-desktopinstall command if you prepend it with an @-symbol (which tells yum that you want to perform a groupinstall):
~]# yum install @kde-desktop1.2.3. Removing
yum remove <package_name>
uninstalls (removes in RPM and Yum
terminology) the package, as well as any packages that depend on it. As
when you install multiple packages, you can remove several at once by
adding more package names to the command:
yum remove foo bar bazinstall, remove can take these arguments:
- package names
- glob expressions
- file lists
- package provides
Warning: Removing a Package when Other Packages Depend On It
Removing a Package Group
install syntax.
Example 1.6. Alternative but equivalent ways of removing a package group
~]#yum groupremove "KDE (K Desktop Environment)"~]#yum groupremove kde-desktop~]#yum remove @kde-desktop
Smart package group removal
yum to remove only those packages which are not required by any other packages or groups by adding the groupremove_leaf_only=1 directive to the [main] section of the /etc/yum.conf configuration file. For more information on this directive, refer to Section 1.3.1, “Setting [main] Options”.
1.3. Configuring Yum and Yum Repositories
- set global Yum options by editing the
[main]section of the/etc/yum.confconfiguration file; - set options for individual repositories by editing the [
repository] sections in/etc/yum.confand.repofiles in the/etc/yum.repos.d/directory; - use Yum variables in
/etc/yum.confand files in/etc/yum.repos.d/so that dynamic version and architecture values are handled correctly; and, - set up your own custom Yum repository.
/etc/yum.conf configuration file contains one mandatory [main] section under which you can set Yum options. The values that you define in the [main] section of yum.conf have global effect, and may override values set any individual [repository] sections. You can also add [repository] sections to /etc/yum.conf; however, best practice is to define individual repositories in new or existing .repo files in the /etc/yum.repos.d/directory. Refer to Section 1.3.2, “Setting [repository] Options” if you need to add or edit repository-specific information.
1.3.1. Setting [main] Options
/etc/yum.conf configuration file contains exactly one [main] section. You can add many additional options under the [main] section heading in /etc/yum.conf. Some of the key-value pairs in the [main] section affect how yum operates; others affect how Yum treats repositories. The best source of information for all Yum options is in the [main] OPTIONS and [repository] OPTIONS sections of man yum.conf.
/etc/yum.conf configuration file:
[main]
cachedir=/var/cache/yum/$basearch/$releasever
keepcache=0
debuglevel=2
logfile=/var/log/yum.log
exactarch=1
obsoletes=1
gpgcheck=1
plugins=1
installonly_limit=3
[comments abridged]
# PUT YOUR REPOS HERE OR IN separate files named file.repo
# in /etc/yum.repos.d
[main] section, and descriptions for each:
- assumeyes=
<value> - ...where
<value>is one of:0—yumshould prompt for confirmation of critical actions it performs. This is the default.1— Do not prompt for confirmation of criticalyumactions. Ifassumeyes=1is set,yumbehaves in the same way that the command line option-ydoes. - cachedir=
/var/cache/yum/$basearch/$releasever - This option specifies the directory where Yum should store its cache and database files. By default, Yum's cache directory is
/var/cache/yum/$basearch/$releasever. See Section 1.3.3, “Using Yum Variables” for descriptions of the$basearchand$releaseverYum variables. - debuglevel=
value - ...where
<value>is an integer between1and10. Setting a higherdebuglevelvalue causesyumto display more detailed debugging output.debuglevel=0disables debugging output, whiledebuglevel=2is the default. - exactarch=
<value> - ...where
<value>is one of:0— Do not take into account the exact architecture when updating packages.1— Consider the exact architecture when updating packages. With this setting,yumwill not install an i686 package to update an i386 package already installed on the system. This is the default. - exclude=
<package_name>[more_package_names] - This option allows you to exclude packages by keyword during installation/updates. Listing multiple packages for exclusion can be accomplished by quoting a space-delimited list of packages. Shell globs using wildcards (for example,
*and?) are allowed. - gpgcheck=
<value> - ...where
<value>is one of:0— Disable GPG signature-checking on packages in all repositories, including local package installation.1— Enable GPG signature-checking on all packages in all repositories, including local package installation.gpgcheck=1is the default, and thus all packages' signatures are checked.If this option is set in the[main]section of the/etc/yum.conffile, it sets the GPG-checking rule for all repositories. However, you can also setgpgcheck=<value>for individual repositories instead; i.e., you can enable GPG-checking on one repository while disabling it on another. Settinggpgcheck=for an individual repository in its correpsonding<value>.repofile overrides the default if it is present in/etc/yum.conf. Refer to Section 3.3, “Checking a Package's Signature” for further information on GPG signature-checking. - groupremove_leaf_only=
<value> - ...where
<value>is one of:0—yumshould not check the dependencies of each package when removing a package group. With this setting,yumremoves all packages in a package group, regardless of whether those packages are required by other packages or groups.groupremove_leaf_only=0is the default.1—yumshould check the dependencies of each package when removing a package group, and remove only those packages which are not not required by any other package or group.For more information on removing packages, refer to Smart package group removal. - installonlypkgs=
<space><separated><list><of><packages> - Here you can provide a space-separated list of packages which
yumcan install, but will never update. Refer toman yum.conffor the list of packages which are install-only by default. If you add theinstallonlypkgsdirective to/etc/yum.conf, you should ensure that you list all of the packages that should be install-only, including any of those listed under theinstallonlypkgssection ofman yum.conf. In particular, kernel packages should always be listed ininstallonlypkgs(as they are by default), andinstallonly_limitshould always be set to a value greater than2so that a backup kernel is always available in case the default one fails to boot. Refer to installonly_limit=<value>for details on theinstallonly_limitdirective. - installonly_limit=
<value> - ...where
<value>is an integer representing the maximum number of versions that can be installed simultaneously for any single package listed in theinstallonlypkgsdirective. The defaults for theinstallonlypkgsdirective include several different kernel packages, so be aware that changing the value ofinstallonly_limitwill also affect the maximum number of installed versions of any single kernel package. The default value listed in/etc/yum.confisinstallonly_limit=3, and it is not recommended to decrease this value, particularly below2. - keepcache=
<value> - ...where value is one of:
0— Do not retain the cache of headers and packages after a successful installation. This is the default.1— Retain the cache after a successful installation. - logfile=
/var/log/yum.log - This option specifies where
yumshould send its logging output. By default,yumlogs to/var/log/yum.log. - multilib_policy=
<value> - ...where
<value>is one of:best— install the best-choice architecture for this system. For example, settingmultilib_policy=beston an AMD64 system causesyumto install 64-bit versions of all packages.all— always install every possible architecture for every package. For example, withmultilib_policyset toallon an AMD64 system,yumwould install both the i586 and AMD64 versions of a package, if both were available. - obsoletes=
<value> - ...where
<value>is one of:0— Disableyum's obsoletes processing logic when performing updates.1— Enableyum's obsoletes processing logic when performing updates. When one package declares in its spec file that it obsoletes another package, the latter package will be replaced by the former package when the former package is installed. Obsoletes are declared, for example, when a package is renamed.obsoletes=1the default. - plugins=
<value> - ...where
<value>is one of:0— Disable all Yum plugins globally.Disabling plugins is not advised
Disabling all plugins is not advised because certain plugins provide importantYumservices. In particular, rhnplugin enables connecting toRed Hat Network, and the security plugin allows system administrators to easily update the system with (sometimes critical) security updates. Disabling plugins globally is provided as a convenience option, and is generally only recommended when diagnosing a potential problem withYum.1— Enable all Yum plugins globally. Withplugins=1, you can still disable a specific Yum plugin by settingenabled=0in that plugin's configuration file. Refer to Section 1.4, “Yum Plugins” for more information about various Yum plugins, or to Section 1.4.1, “Enabling, Configuring and Disabling Yum Plugins” for further information on controlling plugins. - reposdir=
</absolute/path/to/directory/containing/repo/files> - This option allows you to specify a directory where
.repofiles are located. All.repofiles contain repository information (similar to the [repository] section(s) of/etc/yum.conf).yumcollects all repository information from.repofiles and the [repository] section of the/etc/yum.conffile to create a master list of repositories to use for transactions. Refer to Section 1.3.2, “Setting [repository] Options” for more information about options you can use for both the [repository] section and.repofiles. Ifreposdiris not set,yumuses the default directory/etc/yum.repos.d/. - retries=
<value> - ...where
<value>is an integer0or greater. This value sets the number of timesyumshould attempt to retrieve a file before returning an error. Setting this to0makesyumretry forever. The default value is10.
1.3.2. Setting [repository] Options
repository] sections (where repository is a unique repository ID, such as [my_personal_repo]) to /etc/yum.conf or to .repo files in the /etc/yum.repos.d/directory. All .repo files in /etc/yum.repos.d/are read by yum; best practice is to define your repositories here instead of in /etc/yum.conf. You can create new, custom .repo files in this directory, add [repository] sections to those files, and the next time you run a yum command, it will take all newly-added repositories into account.
.repo file should take:
[repository_ID] name=A Repository Name baseurl=http://path/to/repo or ftp://path/to/repo or file://path/to/local/repo
repository] section must contain the following minimum parts:
- [
repository_ID] - The repository ID is a unique, one-word (no spaces; underscores are allowed) string of characters (enclosed by brackets) that serves as a repository identifier.
- name=
<My Repository Name> - This is a human-readable string describing the repository.
- baseurl=http://path/to/repo, ftp://path/to/repo, file://path/to/local/repo
- This is a URL to the directory where the repodata directory of a repository is located. Usually this URL is an HTTP link, such as:
baseurl=http://path/to/repo/releases/$releasever/server/$basearch/os/
Yum always expands the$releasever,$archand$basearchvariables in URLs. See the following section for explanations of all Yum variables: Section 1.3.3, “Using Yum Variables”.- If the repository is available over FTP, use: ftp://path/to/repo
- If the repository is local to the machine, use file://path/to/local/repo
- If a specific online repository requires basic HTTP authentication, you can specify your username and password in the
http://path/to/repoby prepending it asusername:password@link. For example, if a repository on http://www.example.com/repo/ requires a username of "user" and a password of "password", then thebaseurllink could be specified as:baseurl=http://
user:password@www.example.com/repo/
repository] directive:
- enabled=
<value> - ...where
<value>is one of:0— do not include this repository as a package source when performing updates and installs. This is an easy way of quickly turning repositories on and off, which is useful when you desire a single package from a repository that you do not want to enable for updates or installs.1— include this repository as a package source.Turning repositories on and off can also be performed quickly by passing either the--enablerepo=<orrepo_name>--disablerepo=<option torepo_name>yum, or easily through PackageKit's Add/Remove Software window.
repository] options exist. Refer to the [repository] OPTIONS section of man yum.conf for the exhaustive list and descriptions for each.
1.3.3. Using Yum Variables
yum commands and in all Yum configuration files (/etc/yum.conf and all .repo files in /etc/yum.repos.d/.
-
$releasever - You can use this variable to reference the release version of Red Hat Enterprise Linux. Yum obtains the value of
$releaseverfrom thedistroverpkg=<value>line in the/etc/yum.confconfiguration file. If there is no such line in/etc/yum.conf, thenyuminfers the correct value by deriving the version number from theredhat-releasepackage. -
$arch - You can use this variable to refer to the system's CPU architecture as returned when calling Python's
os.uname()function. Valid values for$archinclude:i586,i686andx86_64. -
$basearch - You can use
$basearchto reference the base architecture of the system. For example, i686 and i586 machines both have a base architecture ofi386, and AMD64 and Intel64 machines have a base architecture ofx86_64. -
$YUM0-9 - These ten variables are each replaced with the value of any shell environment variables with the same name. If one of these variables is referenced (in
/etc/yum.conffor example) and a shell environment variable with the same name does not exist, then the configuration file variable is not replaced.
1.3.4. Creating a Yum Repository
Procedure 1.1. Setting Up a Yum repository
- Install the
createrepopackage:~]#
yum install createrepo - Copy all of the packages into one directory, such as
/mnt/local_repo/. - Run the
createrepo --databasecommand on that directory:~]#
createrepo --database /mnt/local_repoImportant
Because RPM packages for Red Hat Enterprise Linux 6 are compressed using the XZ lossless data compression format, and may also be signed using alternative (and stronger) hash algorithms such as SHA-256, it is not possible to runcreaterepoon Red Hat Enterprise Linux 5 to create the package metadata for Red Hat Enterprise Linux 6 packages. Thecreaterepocommand relies onrpmto open and inspect the packages, andrpmon Red Hat Enterprise Linux 5 is not able to open the improved Red Hat Enterprise Linux 6 RPM package format.
yum operations.
1.4. Yum Plugins
yum command:
~]# yum info yum
Loaded plugins: presto, refresh-packagekit, security
[output truncated]Loaded plugins are the names you can provide to the --disableplugins=<plugin_name> option.
1.4.1. Enabling, Configuring and Disabling Yum Plugins
plugins= is present in the [main] section of /etc/yum.conf, and that its value is set to 1:
plugins=1
plugins=0.
Disabling plugins is not advised
Yum services. In particular, rhnplugin enables connecting to Red Hat Network,
and the security plugin allows system administrators to easily update
the system with (sometimes critical) security updates. Disabling plugins
globally is provided as a convenience option, and is generally only
recommended when diagnosing a potential problem with Yum.
/etc/yum/pluginconf.d/ directory. You can set plugin-specific options in these files. For example, here is the security plugin's security.conf configuration file:
Example 1.7. A minimal Yum plugin configuration file
[main] enabled=1
[main] section (similar to Yum's /etc/yum.conf file) in which there is (or you can place if it is missing) an enabled= option that controls whether the plugin is enabled when you run yum commands.
enabled=0 in /etc/yum.conf, then all plugins are disabled regardless of whether they are enabled in their individual configuration files.
yum command, use the --noplugins option.
yum command, then you can add the --disableplugin=<plugin_name> option to the command:
Example 1.8. Disabling the presto plugin while running yum update
~]# yum update --disableplugin=presto--disableplugin= option are the same names listed after the Loaded plugins: line in the output of any yum
command. You can disable multiple plugins by separating their names
with commas. In addition, you can match multiple similarly-named plugin
names or simply shorten long ones by using glob expressions: --disableplugin=presto,refresh-pack*.
1.4.2. Installing More Yum Plugins
yum-plugin-<plugin_name> package-naming convention, but not always: the package which provides the presto plugin is named yum-presto, for example. You can install a Yum plugin in the same way you install other packages:
~]# yum install yum-plugin-security1.4.3. Plugin Descriptions
presto (yum-presto)
protect-packages (yum-plugin-protect-packages)
yum
package and all packages it depends on from being purposefully or
accidentally removed. This simple scheme prevents many of the most
important packages necessary for your system to run from being removed.
In addition, you can list more packages, one per line, in the /etc/sysconfig/protected-packages file[1] (which you should create if it does not exist), and protect-packages will extend protection-from-removal to those packages as well. To temporarily override package protection, use the --override-protection option with an applicable yum command.
rhnplugin (yum-rhn-plugin)
Red Hat Network (RHN). Systems registered with RHN are able to update and install packages from Red Hat Network.
man rhnplugin for more information.
refresh-packagekit (PackageKit-yum-plugin)
security (yum-plugin-security)
yum with a set of highly-useful security-related commands, subcommands and options.
~]# yum check-update --security
Loaded plugins: presto, refresh-packagekit, security
Limiting package lists to security relevant ones
Needed 3 of 7 packages, for security
elinks.x86_64 0.12-0.13.el6 rhel
kernel.x86_64 2.6.30.8-64.el6 rhel
kernel-headers.x86_64 2.6.30.8-64.el6 rhelyum update --security or yum update-minimal --security
to update those packages which are affected by security advisories.
Both of these commands update all packages on the system for which a
security advisiory has been issued. yum update-minimal --security updates them to the latest packages which were released as part of a security advisory, while yum update --security will update all packages affected by a security advisory to the latest version of that package available.
- the kernel-2.6.30.8-16 package is installed on your system;
- the kernel-2.6.30.8-32 package was released as a security update;
- then kernel-2.6.30.8-64 was released as a bug fix update,
yum update-minimal --security will update you to kernel-2.6.30.8-32, and yum update --security will update you to kernel-2.6.30.8-64. Conservative system administrators may want to use update-minimal to reduce the risk incurred by updating packages as much as possible.
man yum-security for usage details and further explanation of the enhancements the security plugin adds to yum.
1.5. Additional Resources
- The Yum home page and wiki — http://yum.baseurl.org/wiki/Guides
- The
Yum Guidessection of the wiki contains more Yum documentation. - Managing Software with Yum — http://docs.fedoraproject.org/en-US/Fedora_Core/5/html-single/Software_Management_Guide/
- A useful resource that provides additional information about using the Yum package manager.
[1]
You can also place files with the extension .list in the /etc/sysconfig/protected-packages.d/ directory (which you should create if it does not exist), and list packages—one per line—in these files. protect-packages will protect these too.
Chapter 2. PackageKit
2.1. Updating Packages with Software Update

gpk-update-viewer command at the shell prompt. In the Software Updates window, all available updates are listed along with the names of the packages being updated (minus the .rpm
suffix, but including the CPU architecture), a short summary of the
package, and, usually, short descriptions of the changes the update
provides. Any updates you do not wish to install can be de-selected here
by unchecking the checkbox corresponding to the update.
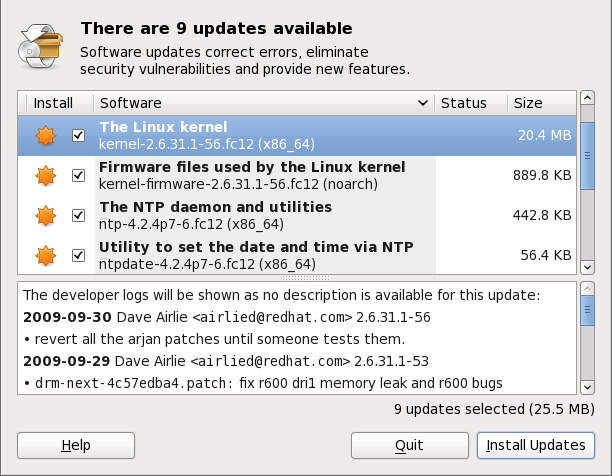
Figure 2.1. Installing updates with Software Update
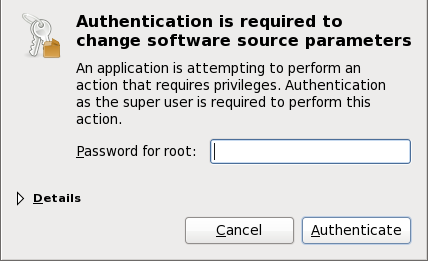
Figure 2.2. PackageKit uses PolicyKit to authenticate
kernel
package, then it will prompt you after installation, asking you whether
you want to reboot the system and thereby boot into the newly-installed
kernel.
Setting the Update-Checking Interval

Figure 2.3. Setting PackageKit's update-checking interval
2.2. Using Add/Remove Software
gpk-application command at the shell prompt.
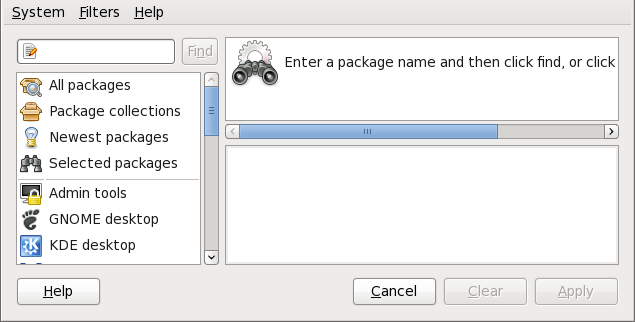
Figure 2.4. PackageKit's Add/Remove Software window
2.2.1. Refreshing Software Sources (Yum Repositories)
name=<My Repository Name> field of all [repository] sections in the /etc/yum.conf configuration file, and in all repository.repo/etc/yum.repos.d/ directory.
enabled=<1 or 0> field in [repository]
sections. Checking an unchecked box enables the Yum repository, and
unchecking it disables it. Performing either function causes PolicyKit to prompt for superuser authentication to enable or disable the repository. PackageKit actually inserts the enabled=<1 or 0> line into the correct [repository] section if it does not exist, or changes the value if it does. This means that enabling or disabling a repository through the Software Sources
window causes that change to persist after closing the window or
rebooting the system. The ability to quickly enable and disable
repositories based on our needs is a highly-convenient feature of PackageKit.
Showing Source RPM, Test and Debuginfo Repositories
2.2.2. Finding Packages with Filters
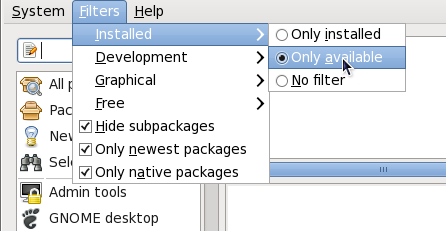
Figure 2.5. Filtering out already-installed packages
<package_name>-devel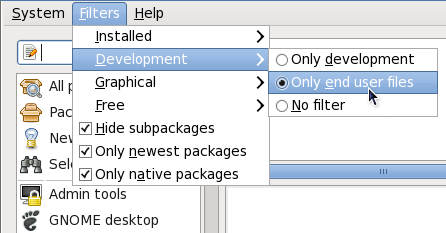
Figure 2.6. Filtering out development packages from the list of Find results
- Narrows the search to either applications which provide a GUI interface or those that do not (). This filter is useful when browsing for GUI applications that perform a specific function.
- Search for packages which are considered to be free software Refer to the Fedora Licensing List for details on approved licenses.
- Checking the checkbox filters out generally-uninteresting packages that are typically only dependencies of other packages that we want. For example, checking and searching for
<package><package>-devel<package>-libs<package>-libs-devel<package>-debuginfo
- Checking filters out all older versions of the same package from the list of results, which is generally what we want.
Important: Using the Only newest items filter
Checking filters out all but the most recent version of any package from the results list. This filter is often combined with the filter to search for the latest available versions of new (not installed) packages. - Only native packages
- Checking the box on a multilib system causes PackageKit to omit listing results for packages compiled for the architecture that runs in compatibility mode. For example, enabling this filter on a 64-bit system with an AMD64 CPU would cause all packages built for the 32-bit x86 CPU architecture not to be shown in the list of results, even though those packages are able to run on an AMD64 machine. Packages which are architecture-agnostic (i.e. noarch packages such as
crontabs-1.10-32.1.el6.noarch.rpm) are never filtered out by checking . This filter has no affect on non-multilib systems, such as x86 machines.
2.2.3. Installing and Removing Packages (and Dependencies)
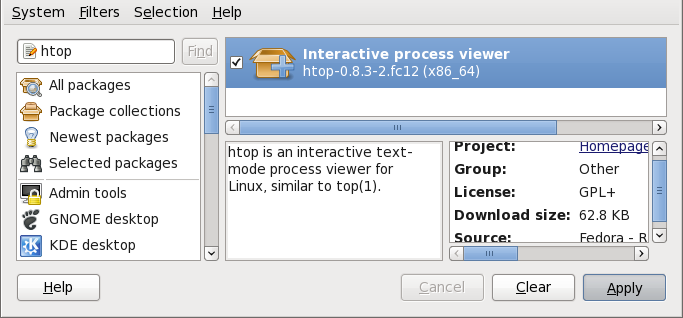
Figure 2.7. Viewing and installing a package with PackageKit's Add/Remove Software window
htop, an colorful and enhanced version of the top process viewer, by opening a shell prompt and entering:
~]$ htop
top is good enough for us and we want to uninstall it. Remembering that we need to change the filter we recently used to install it to in → , we search for htop
again and uncheck it. The program did not install any dependencies of
its own; if it had, those would be automatically removed as well, as
long as they were not also dependencies of any other packages still
installed on our system.
Warning: Removing a Package when Other Packages Depend On It

Figure 2.8. Removing a package with PackageKit's Add/Remove Software window
2.2.4. Installing and Removing Package Groups
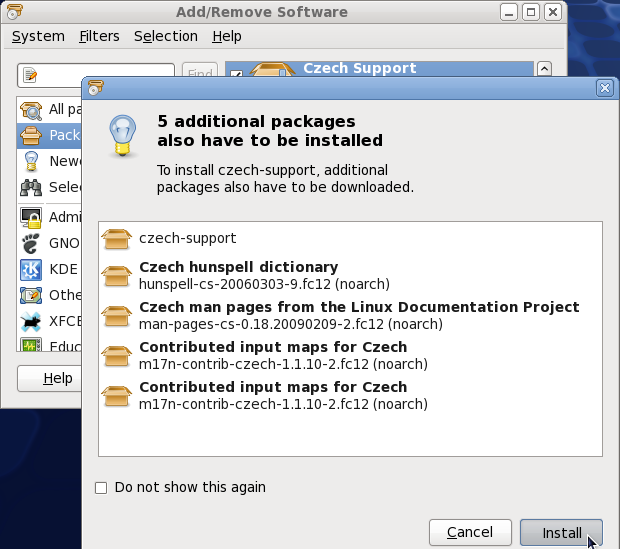
Figure 2.9. Installing the Czech Support package group
2.2.5. Viewing the Transaction Log
gpk-log command at the shell prompt.
Updated System or Installed Packages, the Date on which that action was performed, the Username of the user who performed the action, and the front end Application the user used (such as Update Icon, or kpackagekit). The Details column provides the types of the transactions, such as Updated, Installed or Removed, as well as the list of packages the transactions were performed on.
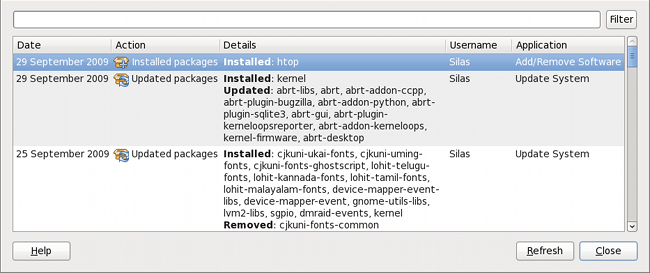
Figure 2.10. Viewing the log of package management transactions with the Software Log Viewer
2.3. PackageKit Architecture
packagekitd daemon back end, which communicates with a package manager-specific back end that utilizes Yum to perform the actual transactions, such as installing and removing packages, etc.
Table 2.1. PackageKit GUI Windows, Menu Locations, and Shell Prompt Commands
| Window Title | Function | How to Open | Shell Command |
|---|---|---|---|
| Add/Remove Software | Install, remove or view package info |
From the GNOME panel: → →
| gpk-application |
| Software Update | Perform package updates |
From the GNOME panel: → →
| gpk-update-viewer |
| Software Sources | Enable and disable Yum repositories |
From Add/Remove Software: →
| gpk-repo |
| Software Log Viewer | View the transaction log |
From Add/Remove Software: →
| gpk-log |
| Software Update Preferences | Set PackageKit preferences | gpk-prefs | |
| (Notification Area Alert) | Alerts you when updates are available |
From the GNOME panel: → → , Startup Programs tab
| gpk-update-icon |
packagekitd daemon runs outside the user session and communicates with the various graphical front ends. The packagekitd daemon[2] communicates via the DBus system message bus with another back end, which utilizes Yum's Python API to perform queries and make changes to the sytem. On Linux systems other than Red Hat and Fedora, packagekitd
can communicate with other back ends that are able to utilize the
native package manager for that system. This modular architecture
provides the abstraction necessary for the graphical interfaces to work
with many different package managers to perform essentially the same
types of package management tasks. Learning how to use the PackageKit
front ends means that you can use the same familiar graphical interface
across many different Linux distributions, even when they utilize a
native package manager other than Yum.
packagekitd daemon, which runs outside of the user session.
gnome-packagekit package instead of by PackageKit and its dependencies. Users working in a KDE environment may prefer to install the kpackagekit package, which provides a KDE interface for PackageKit.
pkcon.
2.4. Additional Resources
- PackageKit home page — http://www.packagekit.org/index.html
- Information about and mailing lists for PackageKit.
- PackageKit FAQ — http://www.packagekit.org/pk-faq.html
- An informative list of Frequently Asked Questions for the PackageKit software suite.
- PackageKit Feature Matrix — http://www.packagekit.org/pk-matrix.html
- Cross-reference PackageKit-provided features with the long list of package manager back ends.
[2]
System daemons are typically long-running processes that provide
services to the user or to other programs, and which are started, often
at boot time, by special initialization scripts (often shortened to init scripts). Daemons respond to the service command and can be turned on or off permanently by using the chkconfig on or chkconfig offcommands. They can typically be recognized by a “d ” appended to their name, such as the packagekitd daemon. Refer to Chapter 7, Controlling Access to Services for information about system services.
Chapter 3. RPM
Use Yum Instead of RPM Whenever Possible
Important
x86_64.rpm.
.tar.gz files.
Note
3.1. RPM Design Goals
- Upgradability
- With RPM, you can upgrade individual components of your system without completely reinstalling. When you get a new release of an operating system based on RPM, such as Red Hat Enterprise Linux, you do not need to reinstall a fresh copy of the operating system your machine (as you might need to with operating systems based on other packaging systems). RPM allows intelligent, fully-automated, in-place upgrades of your system. In addition, configuration files in packages are preserved across upgrades, so you do not lose your customizations. There are no special upgrade files needed to upgrade a package because the same RPM file is used to both install and upgrade the package on your system.
- Powerful Querying
- RPM is designed to provide powerful querying options. You can perform searches on your entire database for packages or even just certain files. You can also easily find out what package a file belongs to and from where the package came. The files an RPM package contains are in a compressed archive, with a custom binary header containing useful information about the package and its contents, allowing you to query individual packages quickly and easily.
- System Verification
- Another powerful RPM feature is the ability to verify packages. If you are worried that you deleted an important file for some package, you can verify the package. You are then notified of anomalies, if any—at which point you can reinstall the package, if necessary. Any configuration files that you modified are preserved during reinstallation.
- Pristine Sources
- A crucial design goal was to allow the use of pristine software sources, as distributed by the original authors of the software. With RPM, you have the pristine sources along with any patches that were used, plus complete build instructions. This is an important advantage for several reasons. For instance, if a new version of a program is released, you do not necessarily have to start from scratch to get it to compile. You can look at the patch to see what you might need to do. All the compiled-in defaults, and all of the changes that were made to get the software to build properly, are easily visible using this technique.The goal of keeping sources pristine may seem important only for developers, but it results in higher quality software for end users, too.
3.2. Using RPM
rpm --help or man rpm. You can also refer to Section 3.5, “Additional Resources” for more information on RPM.
3.2.1. Finding RPM Packages
- The initial RPM repositories provided with the YUM package manager . Refer to Chapter 1, Yum for details on how to use the official Red Hat Enterprise Linux package repositories.
- The Extra Packages for Enterprise Linux (EPEL) is a community effort to provide high-quality add-on packages for Red Hat Enterprise Linux . Refer to http://fedoraproject.org/wiki/EPEL for details on EPEL RPM packages.
- Unofficial, third-party repositories not ahffiliated Red Hat also provide RPM packages.
Important
When considering third-party repositories for use with your Red Hat Enterprise Linux system, pay close attention to the repository's web site with regard to package compatibility before adding the repository as a package source. Alternate package repositories may offer different, incompatible versions of the same software, including packages already included in the Red Hat Enterprise Linux repositories. - The Red Hat Errata Page, available at http://www.redhat.com/apps/support/errata/
3.2.2. Installing and Upgrading
tree-1.5.3-2.el6.x86_64.rpm. The file name includes the package name (tree), version (1.5.3), release (2), operating system major version (el6) and CPU architecture (x86_64).
rpm's -U option to:
- upgrade an existing but older package on the system to a newer version, or
- install the package even if an older version is not already installed.
rpm -U <rpm_file> is able to perform the function of either upgrading or installing as is appropriate for the package.
tree-1.5.3-2.el6.x86_64.rpm
package is in the current directory, log in as root and type the
following command at a shell prompt to either upgrade or install the tree package as determined by rpm:
rpm -Uvh tree-1.5.3-2.el6.x86_64.rpmUse -Uvh for nicely-formatted RPM installs
-v and -h options (which are combined with -U) cause rpm to print more verbose output and display a progress meter using hash signs.
Preparing... ########################################### [100%] 1:tree ########################################### [100%]
Always use the -i (install) option to install new kernel packages!
rpm provides two different options for installing packages: the aforementioned -U option (which historically stands for upgrade), and the -i option, historically standing for install. Because the -U option subsumes both install and upgrade functions, we recommend to use rpm -Uvh with all packages except kernel packages.
-i option to simply install a new kernel package instead of upgrading it. This is because using the -U
option to upgrade a kernel package removes the previous (older) kernel
package, which could render the system unable to boot if there is a
problem with the new kernel. Therefore, use the rpm -i <kernel_package> command to install a new kernel without replacing any older kernel packages. For more information on installing kernel packages, refer to Chapter 23, Manually Upgrading the Kernel.
error: tree-1.5.3-2.el6.x86_64.rpm: Header V3 RSA/SHA256 signature: BAD, key ID d22e77f2
error: tree-1.5.3-2.el6.x86_64.rpm: Header V3 RSA/SHA256 signature: BAD, key ID d22e77f2
NOKEY:
warning: tree-1.5.3-2.el6.x86_64.rpm: Header V3 RSA/SHA1 signature: NOKEY, key ID 57bbccba
3.2.2.1. Package Already Installed
Preparing... ########################################### [100%] package tree-1.5.3-2.el6.x86_64 is already installed
--replacepkgs option, which tells RPM to ignore the error:
rpm -Uvh --replacepkgs tree-1.5.3-2.el6.x86_64.rpm3.2.2.2. Conflicting Files
Preparing... ################################################## file /usr/bin/foobar from install of foo-1.0-1.el6.x86_64 conflicts with file from package bar-3.1.1.el6.x86_64
--replacefiles option:
rpm -Uvh --replacefiles foo-1.0-1.el6.x86_64.rpm3.2.2.3. Unresolved Dependency
error: Failed dependencies: bar.so.3()(64bit) is needed by foo-1.0-1.el6.x86_64
rpm -Uvh foo-1.0-1.el6.x86_64.rpm bar-3.1.1.el6.x86_64.rpmPreparing... ########################################### [100%] 1:foo ########################################### [ 50%] 2:bar ########################################### [100%]
--whatprovides option to determine which package contains the required file.
rpm -q --whatprovides "bar.so.3"bar.so.3 is in the RPM database, the name of the package is displayed:
bar-3.1.1.el6.i586.rpm
Warning: Forcing Package Installation
rpm to install a package that gives us a Failed dependencies error (using the --nodeps option), this is not recommended, and will usually result in the installed package failing to run. Installing or removing packages with rpm --nodeps
can cause applications to misbehave and/or crash, and can cause serious
package management problems or, possibly, system failure. For these
reasons, it is best to heed such warnings; the package manager—whether RPM, Yum or PackageKit—shows us these warnings and suggests possible fixes because accounting for dependencies is critical. The Yum
package manager can perform dependency resolution and fetch
dependencies from online repositories, making it safer, easier and
smarter than forcing rpm to carry out actions without regard to resolving dependencies.
3.2.3. Configuration File Changes
saving /etc/foo.conf as /etc/foo.conf.rpmsave
foo.conf.rpmnew,
and leave the configuration file you modified untouched. You should
still resolve any conflicts between your modified configuration file and
the new one, usually by merging changes from the old one to the new one
with a diff program.
package foo-2.0-1.el6.x86_64.rpm (which is newer than foo-1.0-1) is already installed
--oldpackage option:
rpm -Uvh --oldpackage foo-1.0-1.el6.x86_64.rpm3.2.4. Uninstalling
rpm -e foo
Note
foo, not the name of the original package file, foo-1.0-1.el6.x86_64. If you attempt to uninstall a package using the rpm -e command and the original full file name, you will receive a package name error.
rpm -e ghostscript
error: Failed dependencies:
libgs.so.8()(64bit) is needed by (installed) libspectre-0.2.2-3.el6.x86_64
libgs.so.8()(64bit) is needed by (installed) foomatic-4.0.3-1.el6.x86_64
libijs-0.35.so()(64bit) is needed by (installed) gutenprint-5.2.4-5.el6.x86_64
ghostscript is needed by (installed) printer-filters-1.1-4.el6.noarch<library_name>.so.<number> ~]# rpm -q --whatprovides "libgs.so.8()(64bit)"
ghostscript-8.70-1.el6.x86_64Warning: Forcing Package Installation
rpm to remove a package that gives us a Failed dependencies error (using the --nodeps option), this is not recommended, and may cause harm to other installed applications. Installing or removing packages with rpm --nodeps
can cause applications to misbehave and/or crash, and can cause serious
package management problems or, possibly, system failure. For these
reasons, it is best to heed such warnings; the package manager—whether RPM, Yum or PackageKit—shows us these warnings and suggests possible fixes because accounting for dependencies is critical. The Yum
package manager can perform dependency resolution and fetch
dependencies from online repositories, making it safer, easier and
smarter than forcing rpm to carry out actions without regard to resolving dependencies.
3.2.5. Freshening
rpm -Fvh foo-2.0-1.el6.x86_64.rpm*.rpm glob:
rpm -Fvh *.rpm3.2.6. Querying
/var/lib/rpm/,
and is used to query what packages are installed, what versions each
package is, and to calculate any changes to any files in the package
since installation, among other use cases.
-q option. The rpm -q package name command displays the package name, version, and release number of the installed package <package_name>. For example, using rpm -q tree to query installed package tree might generate the following output:
tree-1.5.2.2-4.el6.x86_64
man rpm for details) to further refine or qualify your query:
-a— queries all currently installed packages.-f— queries the RPM database for which package owns<file_name><file_name>rpm -qfinstead of/bin/lsrpm -qf ls).-p— queries the uninstalled package<package_file><package_file>
-idisplays package information including name, description, release, size, build date, install date, vendor, and other miscellaneous information.-ldisplays the list of files that the package contains.-sdisplays the state of all the files in the package.-ddisplays a list of files marked as documentation (man pages, info pages, READMEs, etc.) in the package.-cdisplays a list of files marked as configuration files. These are the files you edit after installation to adapt and customize the package to your system (for example,sendmail.cf,passwd,inittab, etc.).
-v to the command to display the lists in a familiar ls -l format.
3.2.7. Verifying
rpm -V verifies a package. You can use any of the Verify Options listed for querying to specify the packages you wish to verify. A simple use of verifying is rpm -V tree, which verifies that all the files in the tree package are as they were when they were originally installed. For example:
- To verify a package containing a particular file:
rpm -Vf /usr/bin/treeIn this example,/usr/bin/treeis the absolute path to the file used to query a package. - To verify ALL installed packages throughout the system (which will take some time):
rpm -Va - To verify an installed package against an RPM package file:
rpm -Vp tree-1.5.3-2.el6.x86_64.rpmThis command can be useful if you suspect that your RPM database is corrupt.
c"
denotes a configuration file) and then the file name. Each of the eight
characters denotes the result of a comparison of one attribute of the
file to the value of that attribute recorded in the RPM database. A
single period (.) means the test passed. The following characters denote specific discrepancies:
5— MD5 checksumS— file sizeL— symbolic linkT— file modification timeD— deviceU— userG— groupM— mode (includes permissions and file type)?— unreadable file (file permission errors, for example)
3.3. Checking a Package's Signature
<rpm_file> is the file name of the RPM package):
rpm -K --nosignature <rpm_file> <rpm_file>: rsa sha1 (md5) pgp md5 OK-K with -Kvv in the command.
x files as well.
3.3.1. Importing Keys
rpm --import /usr/share/rhn/RPM-GPG-KEYrpm -qa gpg-pubkey*gpg-pubkey-db42a60e-37ea5438
rpm -qi followed by the output from the previous command:
rpm -qi gpg-pubkey-db42a60e-37ea54383.3.2. Verifying Signature of Packages
<rpm-file> with the filename of the RPM package):
rpm -K <rpm-file> md5 gpg OK.
This means that the signature of the package has been verified, that it
is not corrupt, and therefore is safe to install and use.
3.4. Practical and Common Examples of RPM Usage
- Perhaps you have deleted some files by accident, but you are not sure what you deleted. To verify your entire system and see what might be missing, you could try the following command:
rpm -VaIf some files are missing or appear to have been corrupted, you should probably either re-install the package or uninstall and then re-install the package. - At some point, you might see a file that you do not recognize. To find out which package owns it, enter:
rpm -qf /usr/bin/ghostscriptThe output would look like the following:ghostscript-8.70-1.el6.x86_64
- We can combine the above two examples in the following scenario. Say you are having problems with
/usr/bin/paste. You would like to verify the package that owns that program, but you do not know which package ownspaste. Enter the following command,rpm -Vf /usr/bin/pasteand the appropriate package is verified. - Do you want to find out more information about a particular program? You can try the following command to locate the documentation which came with the package that owns that program:
rpm -qdf /usr/bin/freeThe output would be similar to the following:/usr/share/doc/procps-3.2.8/BUGS /usr/share/doc/procps-3.2.8/FAQ /usr/share/doc/procps-3.2.8/NEWS /usr/share/doc/procps-3.2.8/TODO /usr/share/man/man1/free.1.gz /usr/share/man/man1/pgrep.1.gz /usr/share/man/man1/pkill.1.gz /usr/share/man/man1/pmap.1.gz /usr/share/man/man1/ps.1.gz /usr/share/man/man1/pwdx.1.gz /usr/share/man/man1/skill.1.gz /usr/share/man/man1/slabtop.1.gz /usr/share/man/man1/snice.1.gz /usr/share/man/man1/tload.1.gz /usr/share/man/man1/top.1.gz /usr/share/man/man1/uptime.1.gz /usr/share/man/man1/w.1.gz /usr/share/man/man1/watch.1.gz /usr/share/man/man5/sysctl.conf.5.gz /usr/share/man/man8/sysctl.8.gz /usr/share/man/man8/vmstat.8.gz
- You may find a new RPM, but you do not know what it does. To find information about it, use the following command:
rpm -qip crontabs-1.10-32.1.el6.noarch.rpmThe output would be similar to the following:Name : crontabs Relocations: (not relocatable) Version : 1.10 Vendor: Red Hat, Inc. Release : 32.1.el6 Build Date: Thu 03 Dec 2009 02:17:44 AM CET Install Date: (not installed) Build Host: js20-bc1-11.build.redhat.com Group : System Environment/Base Source RPM: crontabs-1.10-32.1.el6.src.rpm Size : 2486 License: Public Domain and GPLv2 Signature : RSA/8, Wed 24 Feb 2010 08:46:13 PM CET, Key ID 938a80caf21541eb Packager : Red Hat, Inc. <http://bugzilla.redhat.com/bugzilla> Summary : Root crontab files used to schedule the execution of programs Description : The crontabs package contains root crontab files and directories. You will need to install cron daemon to run the jobs from the crontabs. The cron daemon such as cronie or fcron checks the crontab files to see when particular commands are scheduled to be executed. If commands are scheduled, it executes them. Crontabs handles a basic system function, so it should be installed on your system.
- Perhaps you now want to see what files the
crontabsRPM package installs. You would enter the following:rpm -qlp crontabs-1.10-32.1.el6.noarch.rpmThe output is similar to the following:/etc/cron.daily /etc/cron.hourly /etc/cron.monthly /etc/cron.weekly /etc/crontab /usr/bin/run-parts /usr/share/man/man4/crontabs.4.gz
3.5. Additional Resources
3.5.1. Installed Documentation
rpm --help— This command displays a quick reference of RPM parameters.man rpm— The RPM man page gives more detail about RPM parameters than therpm --helpcommand.
3.5.2. Useful Websites
- The RPM website — http://www.rpm.org/
- The RPM mailing list can be subscribed to, and its archives read from, here — https://lists.rpm.org/mailman/listinfo/rpm-list
Part III. System Configuration
Table of Contents
- 13. Date and Time Configuration
- 14. Keyboard Configuration
- 15. Users and Groups
- 16. Automated Tasks
- 17. Log Files
- 18. The sysconfig Directory
- 18.1. Files in the
/etc/sysconfig/Directory - 18.1.1.
/etc/sysconfig/arpwatch - 18.1.2.
/etc/sysconfig/authconfig - 18.1.3.
/etc/sysconfig/autofs - 18.1.4.
/etc/sysconfig/clock - 18.1.5.
/etc/sysconfig/dhcpd - 18.1.6.
/etc/sysconfig/firstboot - 18.1.7.
/etc/sysconfig/i18n - 18.1.8.
/etc/sysconfig/init - 18.1.9.
/etc/sysconfig/ip6tables-config - 18.1.10.
/etc/sysconfig/keyboard - 18.1.11.
/etc/sysconfig/ldap - 18.1.12.
/etc/sysconfig/named - 18.1.13.
/etc/sysconfig/network - 18.1.14.
/etc/sysconfig/ntpd - 18.1.15.
/etc/sysconfig/quagga - 18.1.16.
/etc/sysconfig/radvd - 18.1.17.
/etc/sysconfig/samba - 18.1.18.
/etc/sysconfig/selinux - 18.1.19.
/etc/sysconfig/sendmail - 18.1.20.
/etc/sysconfig/spamassassin - 18.1.21.
/etc/sysconfig/squid - 18.1.22.
/etc/sysconfig/system-config-users - 18.1.23.
/etc/sysconfig/vncservers - 18.1.24.
/etc/sysconfig/xinetd
- 18.1.1.
- 18.2. Directories in the
/etc/sysconfig/Directory - 18.3. Additional Resources
- 18.1. Files in the
- 19. The
procFile System - 19.1. A Virtual File System
- 19.2. Top-level Files within the
procFile System - 19.2.1.
/proc/buddyinfo - 19.2.2.
/proc/cmdline - 19.2.3.
/proc/cpuinfo - 19.2.4.
/proc/crypto - 19.2.5.
/proc/devices - 19.2.6.
/proc/dma - 19.2.7.
/proc/execdomains - 19.2.8.
/proc/fb - 19.2.9.
/proc/filesystems - 19.2.10.
/proc/interrupts - 19.2.11.
/proc/iomem - 19.2.12.
/proc/ioports - 19.2.13.
/proc/kcore - 19.2.14.
/proc/kmsg - 19.2.15.
/proc/loadavg - 19.2.16.
/proc/locks - 19.2.17.
/proc/mdstat - 19.2.18.
/proc/meminfo - 19.2.19.
/proc/misc - 19.2.20.
/proc/modules - 19.2.21.
/proc/mounts - 19.2.22.
/proc/mtrr - 19.2.23.
/proc/partitions - 19.2.24.
/proc/slabinfo - 19.2.25.
/proc/stat - 19.2.26.
/proc/swaps - 19.2.27.
/proc/sysrq-trigger - 19.2.28.
/proc/uptime - 19.2.29.
/proc/version
- 19.2.1.
- 19.3. Directories within
/proc/ - 19.4. Using the
sysctlCommand - 19.5. References
Chapter 13. Date and Time Configuration
13.1. Date/Time Properties Tool
system-config-date command at a shell prompt (e.g., xterm or GNOME Terminal). Unless you are already authenticated, you will be prompted to enter the superuser password.
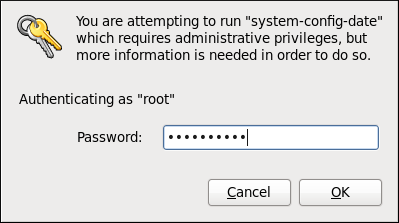
Figure 13.1. Authentication Query
13.1.1. Date and Time Properties
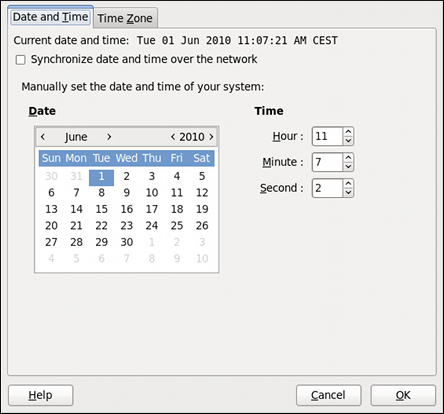
Figure 13.2. Date and Time Properties
- Change the current date. Use the arrows to the left and right of the month and year to change the month and year respectively. Then click inside the calendar to select the day of the month.
- Change the current time. Use the up and down arrow buttons beside the Hour, Minute, and Second, or replace the values directly.
13.1.2. Network Time Protocol Properties
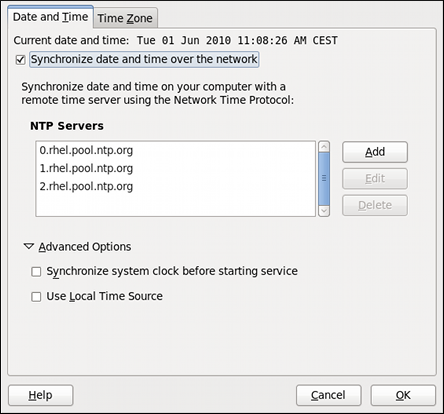
Figure 13.3. Network Time Protocol Properties
Note
13.1.3. Time Zone Properties

Figure 13.4. Time Zone Properties
- Using the interactive map. Click “zoom in” and “zoom out” buttons next to the map, or click on the map itself to zoom into the selected region. Then choose the city specific to your time zone. A red X appears and the time zone selection changes in the list below the map.
- Use the list below the map. To make the selection easier, cities and countries are grouped within their specific continents. Note that non-geographic time zones have also been added to address needs in the scientific community.
13.2. Command Line Configuration
~]$ su -
Password:13.2.1. Date and Time Setup
date command allows the superuser to set the system date and time manually:
- Change the current date. Type the command in the following form at a shell prompt, replacing the
YYYYwith a four-digit year,MMwith a two-digit month, andDDwith a two-digit day of the month:~]#
date +%D -sYYYY-MM-DDFor example, to set the date to 2 June 2010, type:~]#
date +%D -s 2010-06-02 - Change the current time. Use the following command, where
HHstands for an hour,MMis a minute, andSSis a second, all typed in a two-digit form:~]#
date +%T -sHH:MM:SSIf your system clock is set to use UTC (Coordinated Universal Time), add the following option:~]#
date +%T -sHH:MM:SS-uFor instance, to set the system clock to 11:26 PM using the UTC, type:~]#
date +%T -s 23:26:00 -u
date without any additional argument:
Example 13.1. Displaying the current date and time
~]$ date
Wed Jun 2 11:58:48 CEST 201013.2.2. Network Time Protocol Setup
- Firstly, check whether the selected NTP server is accessible:
~]#
ntpdate -qserver_addressFor example:~]#
ntpdate -q 0.rhel.pool.ntp.org - When you find a satisfactory server, run the ntpdate command followed with on or more server addresses:
~]#
ntpdateserver_address...For instance:~]#
ntpdate 0.rhel.pool.ntp.org 1.rhel.pool.ntp.orgUnless an error message is displayed, the system time should now be set. You can check the current by setting typingdatewithout any additional arguments as shown in Section 13.2.1, “Date and Time Setup”. - In most cases, these steps are sufficient. Only if you really need one or more system services to always use the correct time, enable running the ntpdate at boot time:
~]#
chkconfig ntpdate onFor more information about system services and their setup, see Chapter 7, Controlling Access to Services.Note
If the synchronization with the time server at boot time keeps failing, i.e., you find a relevant error message in the/var/log/boot.logsystem log, try to add the following line to/etc/sysconfig/network:NETWORKWAIT=1
- Open the NTP configuration file
/etc/ntp.confin a text editor such as vi or nano, or create a new one if it does not already exist:~]#
nano /etc/ntp.conf - Now add or edit the list of public NTP servers. If you are using Red Hat Enterprise Linux 6, the file should already contain the following lines, but feel free to change or expand these according to your needs:
server 0.rhel.pool.ntp.org server 1.rhel.pool.ntp.org server 2.rhel.pool.ntp.org
Tip
To speed the initial synchronization up, add theiburstdirective at the end of each server line:server 0.rhel.pool.ntp.org iburst server 1.rhel.pool.ntp.org iburst server 2.rhel.pool.ntp.org iburst
- Once you have the list of servers complete, in the same file, set the proper permissions, giving the unrestricted access to localhost only:
restrict default kod nomodify notrap nopeer noquery restrict -6 default kod nomodify notrap nopeer noquery restrict 127.0.0.1 restrict -6 ::1
- Save all changes, exit the editor, and restart the NTP daemon:
~]#
service ntpd restart - Make sure that
ntpddaemon is started at boot time:~]#
chkconfig ntpd on
Chapter 14. Keyboard Configuration
14.1. Changing the Keyboard Layout
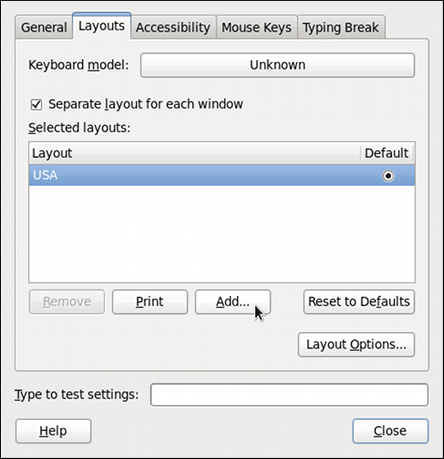
Figure 14.1. Keybord Layout Preferences
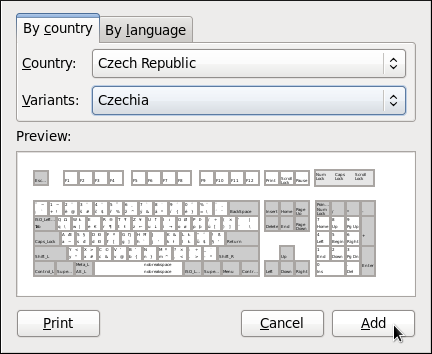
Figure 14.2. Choosing a layout
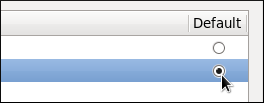
Figure 14.3. Selecting the default layout

Figure 14.4. Testing the layout
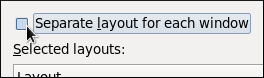
Suggestion: Disable Separate Layout for Each Window

14.2. Adding the Keyboard Layout Indicator
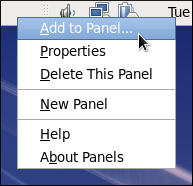
Figure 14.5. Adding a new applet
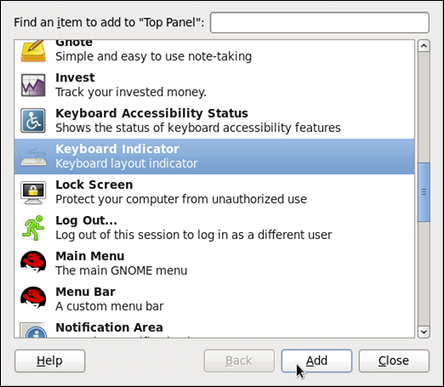
Figure 14.6. Selecting the Keyboard Indicator

Figure 14.7. The Keyboard Indicator applet
14.3. Setting Up a Typing Break
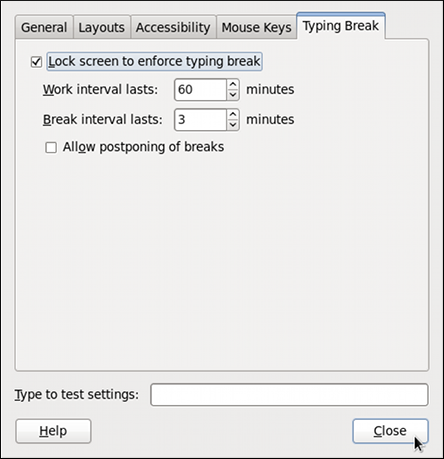
Figure 14.8. Typing Break Properties

Figure 14.9. Taking a break
Chapter 15. Users and Groups
15.1. User and Group Configuration
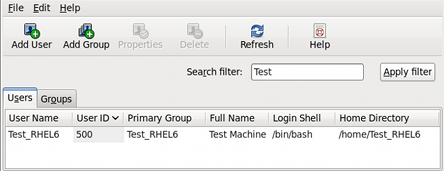
Figure 15.1. The GNOME User Manager
system-config-users at the shell prompt to open the User Manager.
Viewing and modifying user and group information requires superuser
privileges. If you are not the superuser when you open the User Manager, it will prompt you for the superuser password.
15.1.1. Adding a New User
Tip
/bin/bash. The default home directory is /home/<username>/.
You can change the home directory that is created for the user, or you
can choose not to create the home directory by unselecting Create home directory.
/etc/skel/ directory into the new home directory.
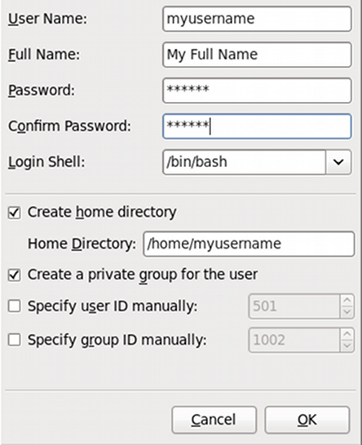
Figure 15.2. Creating a new user
Modifying User Properties
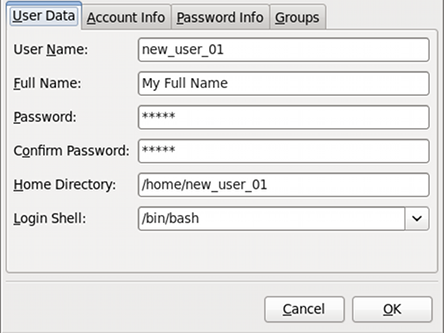
Figure 15.3. User Properties
- User Data — Shows the basic user information configured when you added the user. Use this tab to change the user's full name, password, home directory, or login shell.
- Account Info — Select if you want the account to expire on a certain date. Enter the date in the provided fields. Select Local password is locked to lock the user account and prevent the user from logging into the system.
- Password Info — Displays the date that the user's password last changed. To force the user to change passwords after a certain number of days, select Enable password expiration and enter a desired value in the Days before change required: field. The number of days before the user's password expires, the number of days before the user is warned to change passwords, and days before the account becomes inactive can also be changed.
- Groups — Allows you to view and configure the Primary Group of the user, as well as other groups that you want the user to be a member of.
15.1.2. Adding a New Group
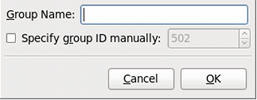
Figure 15.4. New Group
15.1.3. Modifying Group Properties

Figure 15.5. Group Properties
15.2. User and Group Management Tools
system-config-users). For more information on User Manager, refer to Section 15.1, “User and Group Configuration”.
useradd,usermod, anduserdel— Industry-standard methods of adding, deleting and modifying user accountsgroupadd,groupmod, andgroupdel— Industry-standard methods of adding, deleting, and modifying user groupsgpasswd— Industry-standard method of administering the/etc/groupfilepwck,grpck— Tools used for the verification of the password, group, and associated shadow filespwconv,pwunconv— Tools used for the conversion of passwords to shadow passwords and back to standard passwords
15.2.1. Command Line Configuration
Adding a User
useradd are detailed in Table 15.1, “ useradd Command Line Options”.
Table 15.1. useradd Command Line Options
| Option | Description |
|---|---|
-c '<comment>'
|
<comment> can be replaced with any string. This option is generally used to specify the full name of a user.
|
-d <home-dir>
|
Home directory to be used instead of default /home/
|
-e <date>
| Date for the account to be disabled in the format YYYY-MM-DD |
-f <days>
|
Number of days after the password expires until the account is disabled. If 0 is specified, the account is disabled immediately after the password expires. If -1 is specified, the account is not be disabled after the password expires.
|
-g <group-name>
| Group name or group number for the user's default group. The group must exist prior to being specified here. |
-G <group-list>
| List of additional (other than default) group names or group numbers, separated by commas, of which the user is a member. The groups must exist prior to being specified here. |
-m
| Create the home directory if it does not exist. |
-M
| Do not create the home directory. |
-N
| Do not create a user private group for the user. |
-p <password>
|
The password encrypted with crypt
|
-r
| Create a system account with a UID less than 500 and without a home directory |
-s
|
User's login shell, which defaults to /bin/bash
|
-u <uid>
| User ID for the user, which must be unique and greater than 499 |
Adding a Group
groupadd:
groupadd <group-name> groupadd are detailed in Table 15.2, “ groupadd Command Line Options”.
Table 15.2. groupadd Command Line Options
| Option | Description |
|---|---|
| -f, --force |
When used with -g <gid> and <gid> already exists, groupadd will choose another unique <gid> for the group.
|
-g <gid>
| Group ID for the group, which must be unique and greater than 499 |
-K, --key KEY=VALUE
|
override /etc/login.defs defaults
|
-o, --non-unique
| allow to create groups with duplicate |
-p, --password PASSWORD
| use this encrypted password for the new group |
-r
| Create a system group with a GID less than 500 |
Password Aging
chage command with an option from Table 15.3, “ chage Command Line Options”, followed by the username.
Important
chage command. For more information, see Section 15.6, “Shadow Passwords”.
Table 15.3. chage Command Line Options
| Option | Description |
|---|---|
-d <days>
| Specifies the number of days since January 1, 1970 the password was changed |
-E <date>
| Specifies the date on which the account is locked, in the format YYYY-MM-DD. Instead of the date, the number of days since January 1, 1970 can also be used. |
-I <days>
| Specifies the number of inactive days after the password expiration before locking the account. If the value is 0, the account is not locked after the password expires. |
-l
| Lists current account aging settings. |
-m <days>
| Specify the minimum number of days after which the user must change passwords. If the value is 0, the password does not expire. |
-M <days>
|
Specify the maximum number of days for which the password is
valid. When the number of days specified by this option plus the number
of days specified with the -d option is less than the current day, the user must change passwords before using the account.
|
-W <days>
| Specifies the number of days before the password expiration date to warn the user. |
Tip
chage command is followed
directly by a username (with no options), it displays the current
password aging values and allows them to be changed interactively.
- Set up an initial password — There are two common approaches to this step. The administrator can assign a default password or assign a null password.To assign a default password, use the following steps:
- Start the command line Python interpreter with the
pythoncommand. It displays the following:Python 2.4.3 (#1, Jul 21 2006, 08:46:09) [GCC 4.1.1 20060718 (Application Stack 4.1.1-9)] on linux2 Type "help", "copyright", "credits" or "license" for more information. >>>
- At the prompt, type the following commands. Replace
<password>with the password to encrypt and<salt>with a random combination of at least 2 of the following: any alphanumeric character, the slash (/) character or a dot (.):import crypt; print crypt.crypt("<password>","<salt>")The output is the encrypted password, similar to'12CsGd8FRcMSM'. - Press Ctrl-D to exit the Python interpreter.
- At the shell, enter the following command (replacing
<encrypted-password>with the encrypted output of the Python interpreter):usermod -p "
<encrypted-password>"<username>
Alternatively, you can assign a null password instead of an initial password. To do this, use the following command:usermod -p ""
usernameCaution
Using a null password, while convenient, is a highly unsecure practice, as any third party can log in first and access the system using the unsecure username. Always make sure that the user is ready to log in before unlocking an account with a null password. - Force immediate password expiration — Type the following command:
chage -d 0
usernameThis command sets the value for the date the password was last changed to the epoch (January 1, 1970). This value forces immediate password expiration no matter what password aging policy, if any, is in place.
15.2.2. Explaining the Process
useradd juan is issued on a system that has shadow passwords enabled:
- A new line for
juanis created in/etc/passwd.
The line has the following characteristics:juan:x:501:501::/home/juan:/bin/bash- It begins with the username
juan. - There is an
xfor the password field indicating that the system is using shadow passwords. - A UID greater than 499 is created. Under Red Hat Enterprise Linux. UIDs and GIDs below 500 are reserved for system use. These should not be assigned to users.
- A GID greater than 499 is created.
- The optional GECOS information is left blank.
- The home directory for
juanis set to/home/juan/. - The default shell is set to
/bin/bash.
- A new line for
juanis created in/etc/shadow.
The line has the following characteristics:juan:!!:14798:0:99999:7:::- It begins with the username
juan. - Two exclamation points (
!!) appear in the password field of the/etc/shadowfile, which locks the account.Note
If an encrypted password is passed using the-pflag, it is placed in the/etc/shadowfile on the new line for the user. - The password is set to never expire.
- A new line for a group named
juanis created in/etc/group.
A group with the same name as a user is called a user private group. For more information on user private groups, refer to Section 15.1.1, “Adding a New User”.juan:x:501:The line created in/etc/grouphas the following characteristics:- It begins with the group name
juan. - An
xappears in the password field indicating that the system is using shadow group passwords. - The GID matches the one listed for user
juanin/etc/passwd.
- A new line for a group named
juanis created in/etc/gshadow.
The line has the following characteristics:juan:!::- It begins with the group name
juan. - An exclamation point (
!) appears in the password field of the/etc/gshadowfile, which locks the group. - All other fields are blank.
- A directory for user
juanis created in the/home/directory.
This directory is owned by userls -l /homedrwx------. 4 juan juan 4096 Jul 9 14:55 juanjuanand groupjuan. It has read, write, and execute privileges only for the userjuan. All other permissions are denied. - The files within the
/etc/skel/directory (which contain default user settings) are copied into the new/home/juan/directory.
juan exists on the system. To activate it, the administrator must next assign a password to the account using the passwd command and, optionally, set password aging guidelines.
15.3. Standard Users
/etc/passwd file by an Everything installation. The groupid (GID) in this table is the primary group for the user. See Section 15.4, “Standard Groups” for a listing of standard groups.
Table 15.4. Standard Users
| User | UID | GID | Home Directory | Shell | Packages |
|---|---|---|---|---|---|
| root | 0 | 0 | /root |
/bin/bash
|
setup
|
| bin | 1 | 1 | /bin |
/sbin/nologin
|
setup
|
| daemon | 2 | 2 | /sbin |
/sbin/nologin
|
setup
|
| sys | - | 3 | - |
-
|
setup
|
| adm | 3 | 4 | /var/adm |
/bin/bash
|
setup
|
| tty | - | 5 | - |
-
|
setup
|
| disk | - | 6 | - |
-
|
setup
|
| lp | 4 | 7 | /var/spool/lpd |
/sbin/nologin
|
setup
|
| mem | - | 8 | - |
-
|
setup
|
| kmem | - | 9 | - |
-
|
setup
|
| wheel | - | 10 | - |
-
|
setup
|
| cdrom | - | 11 | - |
-
|
udev,MAKEDEV
|
| sync | 5 | (0) | /sbin |
/bin/sync
|
setup
|
| shutdown | 6 | (0) | /sbin |
/sbin/shutdown
|
setup
|
| halt | 7 | (0) | /sbin |
/sbin/halt
|
setup
|
| 8 | 12 | /var/spool/mail |
/sbin/nologin
|
setup
| |
| news | 9 | 13 | /var/spool/news |
/sbin/nologin
|
setup
|
| uucp | 10 | 14 | /var/spool/uucp |
/sbin/nologin
|
setup
|
| operator | 11 | (0) | /root |
/sbin/nologin
|
setup
|
| games | 12 | (100) | /usr/games |
/sbin/nologin
|
setup
|
| gopher | 13 | 30 | /usr/lib/gopher-data |
/sbin/nologin
|
setup
|
| ftp | 14 | 50 | /var/ftp |
/sbin/nologin
|
setup
|
| man | - | 15 | - |
-
|
setup
|
| oprofile | 16 | 16 | /home/oprofile |
/sbin/nologin
|
oprofile
|
| pkiuser | 17 | 17 | /usr/share/pki |
/sbin/nologin
|
pki-ca,rhpki-ca
|
| dialout | - | 18 | - |
-
|
udev,MAKEDEV
|
| floppy | - | 19 | - |
-
|
dev,MAKEDEV
|
| games | - | 20 | - |
-
|
setup
|
| slocate | - | 21 | - |
-
|
slocate
|
| utmp | - | 22 | - |
-
|
initscripts,libutempter
|
| squid | 23 | 23 | /var/spool/squid |
/dev/null
|
squid
|
| pvm | 24 | 24 | /usr/share/pvm3 |
/bin/bash
|
pvm
|
| named | 25 | 25 | /var/named |
/bin/false
|
bind
|
| postgres | 26 | 26 | /var/lib/pgsql |
/bin/bash
|
postgresql-server
|
| mysql | 27 | 27 | /var/lib/mysql |
/bin/bash
|
mysql
|
| nscd | 28 | 28 | / |
/bin/false
|
nscd
|
| rpcuser | 29 | 29 | /var/lib/nfs |
/bin/false
|
nfs-utils
|
| console | - | 31 | - |
-
|
dev
|
| rpc | 32 | 32 | / |
/bin/false
|
portmap
|
| amanda | 33 | (6) | /var/lib/amanda |
/bin/false
|
amanda
|
| tape | - | 33 | - |
-
|
udev,MAKEDEV
|
| netdump | 34 | 34 | /var/crash |
/bin/bash
|
netdump-client, netdump-server
|
| utempter | - | 35 | - |
-
|
libutempter
|
| vdsm | 36 | - | / |
/bin/bash
|
kvm, vdsm
|
| kvm | - | 36 | - |
-
|
kvm, vdsm, libvirt
|
| rpm | 37 | 37 | /var/lib/rpm |
/bin/bash
|
rpm
|
| ntp | 38 | 38 | /etc/ntp |
/sbin/nologin
|
ntp
|
| video | - | 39 | - |
-
|
setup
|
| dip | - | 40 | - |
-
|
setup
|
| mailman | 41 | 41 | /var/mailman |
/bin/false
|
mailman
|
| gdm | 42 | 42 | /var/gdm |
/bin/bash
|
gdm
|
| xfs | 43 | 43 | /etc/X11/fs |
/bin/false
|
XFree86-xfs
|
| pppusers | - | 44 | - |
-
|
linuxconf
|
| popusers | - | 45 | - |
-
|
linuxconf
|
| slipusers | - | 46 | - |
-
|
linuxconf
|
| mailnull | 47 | 47 | /var/spool/mqueue |
/dev/null
|
sendmail
|
| apache | 48 | 48 | /var/www |
/bin/false
|
apache
|
| wnn | 49 | 49 | /home/wnn |
/bin/bash
|
FreeWnn
|
| smmsp | 51 | 51 | /var/spool/mqueue |
/dev/null
|
sendmail
|
| puppet | 52 | 52 | /var/lib/puppet |
/sbin/nologin
|
puppet
|
| tomcat | 53 | 53 | /var/lib/tomcat |
/sbin/nologin
|
tomcat
|
| lock | - | 54 | - |
-
|
lockdev
|
| ldap | 55 | 55 | /var/lib/ldap |
/bin/false
|
openldap-servers
|
| frontpage | 56 | 56 | /var/www |
/bin/false
|
mod_frontpage
|
| nut | 57 | 57 | /var/lib/ups |
/bin/false
|
nut
|
| beagleindex | 58 | 58 | /var/cache/beagle |
/bin/false
|
beagle
|
| tss | 59 | 59 | - |
/sbin/nologin
|
trousers
|
| piranha | 60 | 60 | /etc/sysconfig/ha |
/dev/null
|
piranha
|
| prelude-manager | 61 | 61 | - |
/sbin/nologin
|
prelude-manager
|
| snortd | 62 | 62 | - |
/sbin/nologin
|
snortd
|
| audio | - | 63 | - |
-
|
setup
|
| condor | 64 | 64 | /var/lib/condor |
/sbin/nologin
|
condord
|
| nslcd | 65 | (55) | / |
/sbin/nologin
|
nslcd
|
| wine | - | 66 | - |
-
|
wine
|
| pegasus | 66 | 65 | /var/lib/Pegasus |
/sbin/nologin
|
tog-pegasus
|
| webalizer | 67 | 67 | /var/www/html/usage |
/sbin/nologin
|
webalizer
|
| haldaemon | 68 | 68 | / |
/sbin/nologin
|
hal
|
| vcsa | 69 | 69 | - |
/sbin/nologin
|
dev,MAKEDEV
|
| avahi | 70 | 70 | /var/run/avahi-daemon |
/sbin/nologin
|
avahi
|
| realtime | - | 71 | - |
-
|
-
|
| tcpdump | 72 | 72 | / |
/sbin/nologin
|
tcpdump
|
| privoxy | 73 | 73 | /etc/privoxy |
/bin/bash
|
privoxy
|
| sshd | 74 | 74 | /var/empty/sshd |
/sbin/nologin
|
openssh-server
|
| radvd | 75 | 75 | / |
/bin/false
|
radvd
|
| cyrus | 76 | (12) | /var/imap |
/bin/bash
|
cyrus-imapd
|
| saslauth | - | 76 | - |
-
|
cyrus-imapd
|
| arpwatch | 77 | 77 | /var/lib/arpwatch |
/sbin/nologin
|
arpwatch
|
| fax | 78 | 78 | /var/spool/fax |
/sbin/nologin
|
mgetty
|
| nocpulse | 79 | 79 | /etc/sysconfig/nocpulse |
/bin/bash
|
nocpulse
|
| desktop | 80 | 80 | - |
/sbin/nologin
|
desktop-file-utils
|
| dbus | 81 | 81 | / |
/sbin/nologin
|
dbus
|
| jonas | 82 | 82 | /var/lib/jonas |
/sbin/nologin
|
jonas
|
| clamav | 83 | 83 | /tmp |
/sbin/nologin
|
clamav
|
| screen | - | 84 | - |
-
|
screen
|
| quaggavt | - | 85 | - |
-
|
quagga
|
| sabayon | 86 | 86 | - |
/sbin/nologin
|
sabayon
|
| polkituser | 87 | 87 | / |
/sbin/nologin
|
PolicyKit
|
| wbpriv | - | 88 | - |
-
|
samba-common
|
| postfix | 89 | 89 | /var/spool/postfix |
/bin/true
|
postfix
|
| postdrop | - | 90 | - |
-
|
postfix
|
| majordomo | 91 | 91 | /usr/lib/majordomo |
/bin/bash
|
majordomo
|
| quagga | 92 | 92 | / |
/sbin/nologin
|
quagga
|
| exim | 93 | 93 | /var/spool/exim |
/sbin/nologin
|
exim
|
| distcache | 94 | 94 | / |
/sbin/nologin
|
distcache
|
| radiusd | 95 | 95 | / |
/bin/false
|
freeradius
|
| hsqldb | 96 | 96 | /var/lib/hsqldb |
/sbin/nologin
|
hsqldb
|
| dovecot | 97 | 97 | /usr/libexec/dovecot |
/sbin/nologin
|
dovecot
|
| ident | 98 | 98 | / |
/sbin/nologin
|
ident
|
| nobody | 99 | 99 | / |
/sbin/nologin
|
setup
|
| users | - | 100 | - |
-
|
setup
|
| qemu | 107 | 107 | / |
/sbin/nologin
|
libvirt
|
| ovirt | 108 | 108 | / |
/sbin/nologin
|
libvirt
|
| saned | 111 | 111 | / |
/sbin/nologin
|
sane-backends
|
| vhostmd | 112 | 112 | /usr/share/vhostmd |
/sbin/nologin
|
vhostmd
|
| usbmuxd | 113 | 113 | / |
/sbin/nologin
|
usbmuxd
|
| bacula | 133 | 133 | /var/spool/bacula |
/sbin/nologin
|
bacula
|
| ricci | 140 | 140 | /var/lib/ricci |
/sbin/nologin
|
ricci
|
| luci | 141 | 141 | /var/lib/luci |
/sbin/nologin
|
luci
|
| stap-server | 155 | 155 | /var/lib/stap-server |
/sbin/nologin
|
systemtap
|
| avahi-autoipd | 170 | 170 | /var/lib/avahi-autoipd |
/sbin/nologin
|
avahi
|
| pulse | 171 | 171 | /var/run/pulse |
/sbin/nologin
|
pulseaudio
|
| rtkit | 172 | 172 | /proc |
/sbin/nologin
|
rtkit
|
| nfsnobody | 65534[a] | 65534 | /var/lib/nfs |
/sbin/nologin
|
nfs-utils
|
[a] nfsnobdy is 4294967294 on 64-bit platforms | |||||
15.4. Standard Groups
/etc/group file.
Table 15.5. Standard Groups
| Group | GID | Members |
|---|---|---|
| root | 0 | root |
| bin | 1 | root, bin, daemon |
| daemon | 2 | root, bin, daemon |
| sys | 3 | root, bin, adm |
| adm | 4 | root, adm, daemon |
| tty | 5 | |
| disk | 6 | root |
| lp | 7 | daemon, lp |
| mem | 8 | |
| kmem | 9 | |
| wheel | 10 | root |
| 12 | mail, postfix | |
| uucp | 14 | uucp |
| man | 15 | |
| games | 20 | |
| gopher | 30 | |
| video | 39 | |
| dip | 40 | |
| ftp | 50 | |
| lock | 54 | |
| audio | 63 | |
| nobody | 99 | |
| users | 100 | |
| dbus | 81 | |
| usbmuxd | 113 | |
| utmp | 22 | |
| utempter | 35 | |
| avahi-autoipd | 170 | |
| floppy | 19 | |
| vcsa | 69 | |
| rpc | 32 | |
| rtkit | 499 | |
| abrt | 498 | |
| nscd | 28 | |
| desktop_admin_r | 497 | |
| desktop_user_r | 496 | |
| cdrom | 11 | |
| tape | 33 | |
| dialout | 18 | |
| haldaemon | 68 | haldaemon |
| apache | 48 | |
| ldap | 55 | |
| saslauth | 495 | |
| postdrop | 90 | |
| postfix | 89 | |
| avahi | 70 | |
| ntp | 38 | |
| rpcuser | 29 | |
| nfsnobody | 4294967294 | |
| pulse | 494 | |
| pulse-access | 493 | |
| fuse | 492 | |
| gdm | 42 | |
| stapdev | 491 | |
| stapusr | 490 | |
| sshd | 74 | |
| tcpdump | 72 | |
| slocate | 21 | |
| dovecot | 97 | |
| dovenull | 489 | |
| mailnull | 47 | |
| smmsp | 51 |
15.5. User Private Groups
/etc/bashrc file. Traditionally on UNIX systems, the umask is set to 022, which allows only the user who created the file or directory to make modifications. Under this scheme, all other users, including members of the creator's group,
are not allowed to make any modifications. However, under the UPG
scheme, this "group protection" is not necessary since every user has
their own private group.
15.5.1. Group Directories
/usr/share/emacs/site-lisp/ directory. Some people are trusted to modify the directory, but not everyone. First create an emacs group, as in the following command:
/usr/sbin/groupadd emacsemacs group, type:
chown -R root.emacs /usr/share/emacs/site-lisp gpasswd command:
/usr/bin/gpasswd -a <username> emacschmod 775 /usr/share/emacs/site-lisp emacs). Use the following command:
chmod 2775 /usr/share/emacs/site-lispemacs group can create and edit files in the /usr/share/emacs/site-lisp/ directory without the administrator having to change file permissions every time users write new files.
ls -l /usr/share/emacs/ displays the current settings:
total 4drwxrwsr-x. 2 root emacs 4096 May 18 15:41 site-lisp
15.6. Shadow Passwords
shadow-utils
package). Doing so enhances the security of system authentication
files. For this reason, the installation program enables shadow
passwords by default.
- Improves system security by moving encrypted password hashes from the world-readable
/etc/passwdfile to/etc/shadow, which is readable only by the root user. - Stores information about password aging.
- Allows the
/etc/login.defsfile to enforce security policies.
shadow-utils
package work properly whether or not shadow passwords are enabled.
However, since password aging information is stored exclusively in the /etc/shadow file, any commands which create or modify password aging information do not work.
chagegpasswd/usr/sbin/usermod-eor-foptions/usr/sbin/useradd-eor-foptions
15.7. Additional Resources
15.7.1. Installed Documentation
- Related man pages — There are a number of man pages for the various applications and configuration files involved with managing users and groups. Some of the more important man pages have been listed here:
- User and Group Administrative Applications
man chage— A command to modify password aging policies and account expiration.man gpasswd— A command to administer the/etc/groupfile.man groupadd— A command to add groups.man grpck— A command to verify the/etc/groupfile.man groupdel— A command to remove groups.man groupmod— A command to modify group membership.man pwck— A command to verify the/etc/passwdand/etc/shadowfiles.man pwconv— A tool to convert standard passwords to shadow passwords.man pwunconv— A tool to convert shadow passwords to standard passwords.man useradd— A command to add users.man userdel— A command to remove users.man usermod— A command to modify users.
- Configuration Files
man 5 group— The file containing group information for the system.man 5 passwd— The file containing user information for the system.man 5 shadow— The file containing passwords and account expiration information for the system.
Chapter 16. Automated Tasks
locate command
is updated daily. A system administrator can use automated tasks to
perform periodic backups, monitor the system, run custom scripts, and
more.
cron, at, and batch.
16.1. Cron and Anacron
cronie RPM package must be installed and the crond service must be running. anacron is a sub-package of cronie. To determine if these packages are installed, use the rpm -q cronie cronie-anacron command.
16.1.1. Starting and Stopping the Service
/sbin/service crond status. To start the cron service, use the command /sbin/service crond start. To stop the service, use the command /sbin/service crond stop. It is recommended that you start the service at boot time. Refer to Chapter 7, Controlling Access to Services for details on starting the cron service automatically at boot time.
16.1.2. Configuring Anacron Jobs
/etc/anacrontab (only root is allowed to modify this file), which contains the following lines:
SHELL=/bin/sh PATH=/sbin:/bin:/usr/sbin:/usr/bin MAILTO=root # the maximal random delay added to the base delay of the jobs RANDOM_DELAY=45 # the jobs will be started during the following hours only START_HOURS_RANGE=3-22 #period in days delay in minutes job-identifier command 1 5 cron.daily nice run-parts /etc/cron.daily 7 25 cron.weekly nice run-parts /etc/cron.weekly @monthly 45 cron.monthly nice run-parts /etc/cron.monthly
SHELL variable tells the system which shell environment to use (in this example the bash shell). The PATH
variable defines the path used to execute commands. The output of the
anacron jobs are emailed to the username defined with the MAILTO variable. If the MAILTO variable is not defined, (i.e. is empty, MAILTO=), email is not sent.
RANDOM_DELAY variable denotes the maximum number of minutes that will be added to the delay in minutes variable which is specified for each job. The minimum delay value is set, by default, to 6 minutes. A RANDOM_DELAY set to 12 would therefore add, randomly, between 6 and 12 minutes to the delay in minutes for each job in that particular anacrontab. RANDOM_DELAY
can also be set to a value below 6, or even 0. When set to 0, no random
delay is added. This proves to be useful when, for example, more
computers that share one network connection need to download the same
data every day. The START_HOURS_RANGE
variable defines an interval (in hours) when scheduled jobs can be run.
In case this time interval is missed, for example, due to a power down,
then scheduled jobs are not executed that day.
/etc/anacrontab file represent scheduled jobs and have the following format:
period in days delay in minutes job-identifier command
period in days— specifies the frequency of execution of a job in days. This variable can be represented by an integer or a macro (@daily,@weekly,@monthly), where@dailydenotes the same value as the integer 1,@weeklythe same as 7, and@monthlyspecifies that the job is run once a month, independent on the length of the month.delay in minutes— specifies the number of minutes anacron waits, if necessary, before executing a job. This variable is represented by an integer where 0 means no delay.job-identifier— specifies a unique name of a job which is used in the log files.command— specifies the command to execute. The command can either be a command such asls /proc >> /tmp/procor a command to execute a custom script.
16.1.2.1. Examples of Anacron Jobs
/etc/anacrontab file:
SHELL=/bin/sh PATH=/sbin:/bin:/usr/sbin:/usr/bin MAILTO=root # the maximal random delay added to the base delay of the jobs RANDOM_DELAY=30 # the jobs will be started during the following hours only START_HOURS_RANGE=16-20 #period in days delay in minutes job-identifier command 1 20 dailyjob nice run-parts /etc/cron.daily 7 25 weeklyjob /etc/weeklyjob.bash @monthly 45 monthlyjob ls /proc >> /tmp/proc
anacrontab
file are randomly delayed by 6-30 minutes and can be executed between
16:00 and 20:00. Thus, the first defined job will run anywhere between
16:26 and 16:50 every day. The command specified for this job will
execute all present programs in the /etc/cron.daily directory (using the run-parts
script which takes a directory as a command-line argument and
sequentially executes every program within that directory). The second
specified job will be executed once a week and will execute the weeklyjob.bash script in the /etc directory. The third job is executed once a month and runs a command to write the contents of the /proc to the /tmp/proc file (e.g. ls /proc >> /tmp/proc).
16.1.2.1.1. Disabling Anacron
cronie-anacron package. Thus, you will be able to define jobs using crontabs only.
16.1.3. Configuring Cron Jobs
/etc/crontab (only root is allowed to modify this file), contains the following lines:
SHELL=/bin/bash PATH=/sbin:/bin:/usr/sbin:/usr/bin MAILTO=root HOME=/ # For details see man 4 crontabs # Example of job definition: # .---------------- minute (0 - 59) # | .------------- hour (0 - 23) # | | .---------- day of month (1 - 31) # | | | .------- month (1 - 12) OR jan,feb,mar,apr ... # | | | | .---- day of week (0 - 6) (Sunday=0 or 7) OR sun,mon,tue,wed,thu,fri,sat # | | | | | # * * * * * user command to be executed
anacrontab file, SHELL, PATH and MAILTO. For more information about these variables, refer to Section 16.1.2, “Configuring Anacron Jobs”. The fourth line contains the HOME variable. The HOME variable can be used to set the home directory to use when executing commands or scripts.
/etc/crontab file represent scheduled jobs and have the following format:
minute hour day month day of week user command
minute— any integer from 0 to 59hour— any integer from 0 to 23day— any integer from 1 to 31 (must be a valid day if a month is specified)month— any integer from 1 to 12 (or the short name of the month such as jan or feb)day of week— any integer from 0 to 7, where 0 or 7 represents Sunday (or the short name of the week such as sun or mon)user— specifies the user under which the jobs are runcommand— the command to execute (the command can either be a command such asls /proc >> /tmp/procor the command to execute a custom script)
1-4 means the integers 1, 2, 3, and 4.
3, 4, 6, 8 indicates those four specific integers.
/<integer>. For example, 0-59/2
can be used to define every other minute in the minute field. Step
values can also be used with an asterisk. For instance, the value */3 can be used in the month field to run the task every third month.
crontab utility. All user-defined crontabs are stored in the /var/spool/cron/
directory and are executed using the usernames of the users that
created them. To create a crontab as a user, login as that user and type
the command crontab -e to edit the user's crontab using the editor specified by the VISUAL or EDITOR environment variable. The file uses the same format as /etc/crontab. When the changes to the crontab are saved, the crontab is stored according to username and written to the file /var/spool/cron/username . To list the contents of your own personal crontab file, use the crontab -l command.
Note
crontab utility, there is no need to specify a user when defining a job.
/etc/cron.d/ directory contains files that have the same syntax as the /etc/crontab file. Only root is allowed to create and modify files in this directory.
Note
/etc/anacrontab file, the /etc/crontab file, the /etc/cron.d/ directory, and the /var/spool/cron/
directory every minute for any changes. If any changes are found, they
are loaded into memory. Thus, the daemon does not need to be restarted
if an anacrontab or a crontab file is changed.
16.1.4. Controlling Access to Cron
/etc/cron.allow and /etc/cron.deny
files are used to restrict access to cron. The format of both access
control files is one username on each line. Whitespace is not permitted
in either file. The cron daemon (crond)
does not have to be restarted if the access control files are modified.
The access control files are checked each time a user tries to add or
delete a cron job.
cron.allow exists, only users listed in it are allowed to use cron, and the cron.deny file is ignored.
cron.allow does not exist, users listed in cron.deny are not allowed to use cron.
/etc/security/access.conf. For example, adding the following line in this file forbids creating crontabs for all users except the root user:
-:ALL EXCEPT root :cron
access.conf.5 (i.e. man 5 access.conf).
16.1.5. Black/White Listing of Cron Jobs
run-parts script on a cron folder, such as /etc/cron.daily, we can define which of the programs in this folder will not be executed by run-parts.
jobs.deny file in the folder that run-parts will be executing from. For example, if we need to omit a particular program from /etc/cron.daily, then, a file /etc/cron.daily/jobs.deny
has to be created. In this file, specify the names of the omitted
programs from the same directory. These will not be executed when a
command, such as run-parts /etc/cron.daily, is executed by a specific job.
jobs.allow file.
jobs.deny and jobs.allow are the same as those of cron.deny and cron.allow described in section Section 16.1.4, “Controlling Access to Cron”.
16.2. At and Batch
at command is used to schedule a one-time task at a specific time and the batch command is used to schedule a one-time task to be executed when the systems load average drops below 0.8.
at or batch, the at RPM package must be installed, and the atd service must be running. To determine if the package is installed, use the rpm -q at command. To determine if the service is running, use the command /sbin/service atd status.
16.2.1. Configuring At Jobs
at time , where time time can be one of the following:
- HH:MM format — For example, 04:00 specifies 4:00 a.m. If the time is already past, it is executed at the specified time the next day.
- midnight — Specifies 12:00 a.m.
- noon — Specifies 12:00 p.m.
- teatime — Specifies 4:00 p.m.
- month-name day year format — For example, January 15 2002 specifies the 15th day of January in the year 2002. The year is optional.
- MMDDYY, MM/DD/YY, or MM.DD.YY formats — For example, 011502 for the 15th day of January in the year 2002.
- now + time — time is in minutes, hours, days, or weeks. For example, now + 5 days specifies that the command should be executed at the same time five days from now.
/usr/share/doc/at-<version>/timespec text file.
at command with the time argument, the at> prompt is displayed. Type the command to execute, press Enter, and press Ctrl+D . Multiple commands can be specified by typing each command followed by the Enter key. After typing all the commands, press Enter to go to a blank line and press Ctrl+D . Alternatively, a shell script can be entered at the prompt, pressing Enter after each line in the script, and pressing Ctrl+D on a blank line to exit. If a script is entered, the shell used is the shell set in the user's SHELL environment, the user's login shell, or /bin/sh (whichever is found first).
atq to view pending jobs. Refer to Section 16.2.3, “Viewing Pending Jobs” for more information.
at command can be restricted. For more information, refer to Section 16.2.5, “Controlling Access to At and Batch” for details.
16.2.2. Configuring Batch Jobs
batch command.
batch command, the at> prompt is displayed. Type the command to execute, press Enter, and press Ctrl+D . Multiple commands can be specified by typing each command followed by the Enter key. After typing all the commands, press Enter to go to a blank line and press Ctrl+D . Alternatively, a shell script can be entered at the prompt, pressing Enter after each line in the script, and pressing Ctrl+D on a blank line to exit. If a script is entered, the shell used is the shell set in the user's SHELL environment, the user's login shell, or /bin/sh (whichever is found first). As soon as the load average is below 0.8, the set of commands or script is executed.
atq to view pending jobs. Refer to Section 16.2.3, “Viewing Pending Jobs” for more information.
batch command can be restricted. For more information, refer to Section 16.2.5, “Controlling Access to At and Batch” for details.
16.2.3. Viewing Pending Jobs
at and batch jobs, use the atq command. The atq
command displays a list of pending jobs, with each job on a line. Each
line follows the job number, date, hour, job class, and username format.
Users can only view their own jobs. If the root user executes the atq command, all jobs for all users are displayed.
16.2.4. Additional Command Line Options
at and batch include:
Table 16.1. at and batch Command Line Options
| Option | Description |
|---|---|
-f
| Read the commands or shell script from a file instead of specifying them at the prompt. |
-m
| Send email to the user when the job has been completed. |
-v
| Display the time that the job is executed. |
16.2.5. Controlling Access to At and Batch
/etc/at.allow and /etc/at.deny files can be used to restrict access to the at and batch
commands. The format of both access control files is one username on
each line. Whitespace is not permitted in either file. The at daemon (atd)
does not have to be restarted if the access control files are modified.
The access control files are read each time a user tries to execute the
at or batch commands.
at and batch commands, regardless of the access control files.
at.allow exists, only users listed in it are allowed to use at or batch, and the at.deny file is ignored.
at.allow does not exist, users listed in at.deny are not allowed to use at or batch.
16.2.6. Starting and Stopping the Service
at service, use the command /sbin/service atd start. To stop the service, use the command /sbin/service atd stop. It is recommended that you start the service at boot time. Refer to Chapter 7, Controlling Access to Services for details on starting the cron service automatically at boot time.
16.3. Additional Resources
16.3.1. Installed Documentation
cronman page — contains an overview of cron.crontabman pages in sections 1 and 5 — The man page in section 1 contains an overview of thecrontabfile. The man page in section 5 contains the format for the file and some example entries.anacronman page — contains an overview of anacron.anacrontabman page — contains an overview of theanacrontabfile./usr/share/doc/at-contains more detailed information about the times that can be specified for cron jobs.<version>/timespecatman page — description ofatandbatchand their command line options.
Chapter 17. Log Files
rsyslogd. A list of log messages maintained by rsyslogd can be found in the /etc/rsyslog.conf configuration file.
rsyslog replaced syslogd as the default program for forwarding syslog messages over the network. rsyslog uses the basic syslog
protocol and extends its functionality with enhanced filtering,
encryption protected relaying of messages, various configuration
options, or support for transportation via the TCP or UDP protocols.
17.1. Configuring rsyslog
rsyslog is /etc/rsyslog.conf. It is essentially divided in the following parts:
- Modules
- Global directives
- Rules
- Templates
- Filter conditions
- Output channels
/etc/rsyslog.conf configuration file is described in the sections below.
Note
/etc/rsyslog.conf configuration file, any empty lines or any text following a hash sign (#) are comments and are not processed.
17.1.1. Modules
rsyslog offers a variety of modules
which provide dynamic functionality. Note that modules can be written
by third parties. Essentially, modules are comprised of various
configuration directives that become available when a module is loaded.
To load a module, use the following syntax:
$ModLoad <MODULE><MODULE> represents your desired module. For example, if you want to load the Text File Input Module (imfile — enables rsyslog to convert any standard text files into a syslog messages), specify the following line in your /etc/rsyslog.conf configuration file:
$ModLoad imfile
rsyslog offers a number of modules which are split into these main categories:
- Input Modules — Input modules gather messages from various sources. The name of an input module always starts with the
imprefix, such asimfile,imrelp, etc. - Output Modules — Output modules process messages into different formats or perform various actions on them. The name of an output module always starts with the
omprefix, such asomsnmp,omrelp, etc. - Filter Modules — Filter modules provide the ability to filter messages according to specified rules. The name of a filter module always starts with the
fmprefix. - Parser Modules — Parser modules use the message parsers to parse message content of any received messages. The name of a parser module always starts with the
pmprefix, such aspmrfc5424,pmrfc3164, etc. - Message Modification Modules — Message modification modules change the content of asyslog message. The message modification modules only differ in their implementation from the output and filter modules but share the same interface.
- String Generator Modules — String generator modules generate strings based on the message content and strongly cooperate with the template feature provided by
rsyslog. For more information on templates, refer to . The name of a string generator module always starts with thesmprefix, such assmfile,smtradfile, etc. - Library Modules — Library modules provide the ability to load and handle other loadable modules. These modules are loaded automatically by
rsyslogwhen needed and cannot be configured by the user.
Warning
rsyslog loads any
modules, it provides them with access to some of its functions and data.
This poses a possible security threat. To minimize security risks, use
trustworthy modules only.
17.1.2. Global Directives
rsyslogd daemon. All of the global directives must start with a dollar sign ($).
Only one directive can be specified per line. The following is an
example of a global directive that specifies the maximum size of the
syslog message queue:
$MainMsgQueueSize
10,000 messages) can be overridden by specifying a different value.
/usr/share/doc/rsyslog-4.4.2/rsyslog_conf_global.html or online at http://www.rsyslog.com/doc/rsyslog_conf_global.html.
17.1.3. Rules
/etc/rsyslog.conf
configuration file, define both, a selector and an action, on one line
and separate them with one or more spaces or tabs. For more information
on selectors, refer to Section 17.1.3.1, “Selectors” and for information on actions, refer to Section 17.1.3.2, “Actions”.
17.1.3.1. Selectors
<FACILITY>.<PRIORITY>
<FACILITY>specifies the subsystem that produces a specific syslog message. For example, themailsubsystem handles all mail related syslog messages.<FACILITY>can be represented by one of these keywords:auth,authpriv,cron,daemon,kern,lpr,mail,news,syslog,user,uucp, andlocal0throughlocal7.<PRIORITY>specifies a priority of a syslog message.<PRIORITY>can be represented by one of these keywords:debug,info,notice,warning,err,crit,alert, andemerg.By preceding any priority with an equal sign (=), you specify that only syslog messages with that priority will be selected. All other priorities will be ignored. Conversely, preceding a priority with an exclamation mark (!) selects all syslog messages but those with the defined priority. By not using either of these two extensions, you specify a selection of syslog messages with the defined priority and higher.
*)
to define all facilities or priorities (depending on where you place
the asterisk, before or after the dot). Specifying the keyword none serves for facilities with no given priorities.
,). To define multiple selectors on one line, separate them with a semi-colon (;).
kern.* # Selects all kernel syslog messages with any priority
mail.crit # Selects all mail syslog messages with priority crit and higher.
cron.!info,!debug # Selects all cron syslog messages except those with theinfoordebugpriority.
17.1.3.2. Actions
- Syslog message placement
- The majority of actions specify to which log file a syslog message is saved. This is done by specifying a file path after your already defined selector. The following is a rule comprised of a selector that selects all cron syslog messages and an action that saves them into the
/var/log/cronlog file:cron.* /var/log/cron
Use a dash mark (-) as a prefix of the file path you specified if you want to omit syncing the desired log file after every syslog message is generated.Your specified file path can be either static or dynamic. Static files are represented by a simple file path as was shown in the example above. Dynamic files are represented by a template and a question mark (?) prefix. For more information on templates, refer to Section 17.1.4, “Templates”. - Sending syslog messages over the network
rsyslogallows you to send and receive syslog messages over the network. This feature allows to administer syslog messages of multiple hosts on one machine. To forward syslog messages to a remote machine, use the following syntax:@[(
<OPTION>,<MORE OPTIONS>)]<HOST>:[<PORT>]where:- The at sign (
@) indicates that the syslog messages are forwarded to a host using theUDPprotocol. To use theTCPprotocol, use two at signs with no space between them (@@). - The
<OPTION>and<MORE OPTIONS>attributes can be replaced with an option such asz. This option enables zlib compression for syslog messages; the<NUMBER><NUMBER>attribute specifies the level of compression. - The
<HOST>attribute specifies the host which receives the selected syslog messages. - The
<PORT>attribute specifies the host machine's port.
When specifying anIPv6address as the hoset, enclose the address in square brackets ([,]).The following are some examples of actions that forward syslog messages over the network (note that all actions are preceded with a selector that selects all messages with any priority):*.* @192.168.0.1 # Forwards messages to 192.168.0.1 via the
UDPprotocol*.* @@example.com:18 # Forwards messages to "example.com" using port 18 and the
TCPprotocol*.* @(z9)[2001::1] # Compresses messages with zlib (level 9 compression) # and forwards them to 2001::1 using the
UDPprotocol- Sending syslog messages to specific users
- rsyslog can send syslog messages to specific users by simply specifying a username of the user you wish to send the messages to. To specify more than one user, separate each username with a comma (
,). To send messages to every user that is currently logged on, use an asterisk (*). - Discarding syslog messages
- To discard your selected messages, use the tilde character (
~). The following rule discards any cron syslog messages:cron.* ~
;) and specify the name of the template.
Caution
/usr/share/doc/rsyslog-4.4.2/rsyslog_conf_actions.html.
17.1.4. Templates
17.1.5. Filter Conditions
17.1.6. Output Channels
17.2. rsyslog Performance
17.3. Locating Log Files
/var/log/ directory. Some applications such as httpd and samba have a directory within /var/log/ for their log files.
/var/log/ directory with numbers after them (e.g.: cron-20100906).
These numbers represent a timestamp that has been added to a rotated
log file. Log files are rotated so their file sizes do not become too
large. The logrotate package contains a cron task that automatically rotates log files according to the /etc/logrotate.conf configuration file and the configuration files in the /etc/logrotate.d/ directory.
17.3.1. Configuring logrotate
/etc/logrotate.conf configuration file:
# rotate log files weekly weekly # keep 4 weeks worth of backlogs rotate 4 # uncomment this if you want your log files compressed compress
.gz format. Any lines that begin with a hash sign (#) are comments and are not processed
/etc/logrotate.d/ directory and define any configuration options there.
/etc/logrotate.d/ directory:
/var/log/messages {
rotate 5
weekly
postrotate
/usr/bin/killall -HUP syslogd
endscript
}
/var/log/messages log file only. The settings specified here override the global settings where possible. Thus the rotated /var/log/messages log file will be kept for five weeks instead of four weeks as was defined in the global options.
weekly— Specifies the rotation of log files on a weekly basis. Similar directives include:dailymonthlyyearly
compress— Enables compression of rotated log files. Similar directives include:nocompresscompresscmd— Specifies the command to be used for compressing.uncompresscmdcompressext— Specifies what extension is to be used for compressing.compressoptions— Lets you specify any options that may be passed to the used compression program.delaycompress— Postpones the compression of log files to the next rotation of log files.
rotate— Specifies the number of rotations a log file undergoes before it is removed or mailed to a specific address. If the value<INTEGER>0is specified, old log files are removed instead of rotated.mail— This option enables mailing of log files that have been rotated as many times as is defined by the<ADDRESS>rotatedirective to the specified address. Similar directives include:nomailmailfirst— Specifies that the just-rotated log files are to be mailed, instead of the about-to-expire log files.maillast— Specifies that the just-rotated log files are to be mailed, instead of the about-to-expire log files. This is the default option whenmailis enabled.
logrotate man page (man logrotate).
17.4. Viewing Log Files
Vi or Emacs. Some log files are readable by all users on the system; however, root privileges are required to read most log files.
Note: Installing the gnome-system-log package
~]# yum install gnome-system-log~]$ gnome-system-log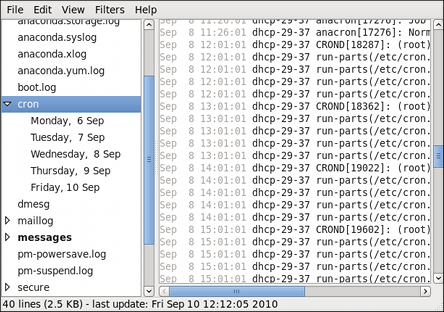
Figure 17.1. Log File Viewer

Figure 17.2. Log File Viewer - Filters
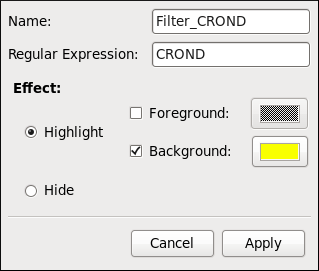
Figure 17.3. Log File Viewer - Defining a Filter
- Name — Specifies the name of the filter.
- Regular Expression — Specifies the regular expression that will be applied to the log file and will attempt to match any possible strings of text in it.
- Effect
- Highlight — If checked, the found results will be highlighted with the selected color. You may select whether to highlight the background or the foreground of the text.
- Hide — If checked, the found results will be hidden from the log file you are viewing.
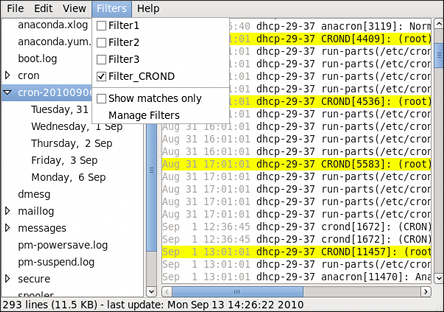
Figure 17.4. Log File Viewer - Enabling a Filter
17.5. Adding a Log File
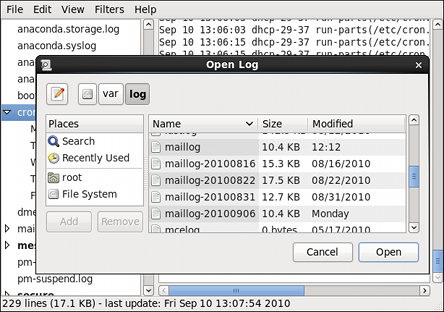
Figure 17.5. Log File Viewer - Adding a Log File
Note
.gz format.
17.6. Monitoring Log Files
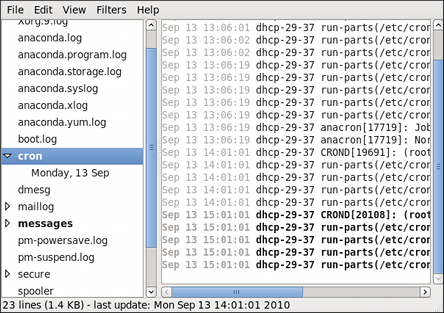
Figure 17.6. Log File Viewer - New Log Alert
17.7. Additional Resources
17.7.1. Installed Documentation
rsyslogdmanual page — Typeman rsyslogdto learn more aboutrsyslogdand its many options.rsyslog.confmanual page — Typeman rsyslog.confto learn more about the/etc/rsyslog.confconfiguration file and its many options./usr/share/doc/rsyslog-— After installing the rsyslog package, this directory contains extensive documentation in the<version-number>htmlformat.logrotatemanual page — Typeman logrotateto learn more aboutlogrotateand its many options.
17.7.2. Useful Websites
- http://www.rsyslog.com/ — Offers a thorough technical breakdown of rsyslog features, documentation, configuration examples, and video tutorials.
- http://wiki.rsyslog.com/index.php/Main_Page — Contains useful
/etc/rsyslog.confconfiguration examples.
Chapter 18. The sysconfig Directory
- 18.1. Files in the
/etc/sysconfig/Directory - 18.1.1.
/etc/sysconfig/arpwatch - 18.1.2.
/etc/sysconfig/authconfig - 18.1.3.
/etc/sysconfig/autofs - 18.1.4.
/etc/sysconfig/clock - 18.1.5.
/etc/sysconfig/dhcpd - 18.1.6.
/etc/sysconfig/firstboot - 18.1.7.
/etc/sysconfig/i18n - 18.1.8.
/etc/sysconfig/init - 18.1.9.
/etc/sysconfig/ip6tables-config - 18.1.10.
/etc/sysconfig/keyboard - 18.1.11.
/etc/sysconfig/ldap - 18.1.12.
/etc/sysconfig/named - 18.1.13.
/etc/sysconfig/network - 18.1.14.
/etc/sysconfig/ntpd - 18.1.15.
/etc/sysconfig/quagga - 18.1.16.
/etc/sysconfig/radvd - 18.1.17.
/etc/sysconfig/samba - 18.1.18.
/etc/sysconfig/selinux - 18.1.19.
/etc/sysconfig/sendmail - 18.1.20.
/etc/sysconfig/spamassassin - 18.1.21.
/etc/sysconfig/squid - 18.1.22.
/etc/sysconfig/system-config-users - 18.1.23.
/etc/sysconfig/vncservers - 18.1.24.
/etc/sysconfig/xinetd
- 18.1.1.
- 18.2. Directories in the
/etc/sysconfig/Directory - 18.3. Additional Resources
/etc/sysconfig/
directory, their function, and their contents. The information in this
chapter is not intended to be complete, as many of these files have a
variety of options that are only used in very specific or rare
circumstances.
Note
/etc/sysconfig/
directory depends on the programs you have installed on your machine.
To find the name of the package the configuration file belongs to, type
the following at a shell prompt:
~]$ yum provides /etc/sysconfig/filename 18.1. Files in the /etc/sysconfig/ Directory
/etc/sysconfig/ directory.
18.1.1. /etc/sysconfig/arpwatch
/etc/sysconfig/arpwatch file is used to pass arguments to the arpwatch daemon at boot time. By default, it contains the following option:
-
OPTIONS=value - Additional options to be passed to the
arpwatchdaemon. For example:OPTIONS="-u arpwatch -e root -s 'root (Arpwatch)'"
18.1.2. /etc/sysconfig/authconfig
/etc/sysconfig/authconfig file sets the authorization to be used on the host. By default, it contains the following options:
-
USEMKHOMEDIR=boolean - A boolean to enable (
yes) or disable (no) creating a home directory for a user on the first login. For example:USEMKHOMEDIR=no
-
USEPAMACCESS=boolean - A boolean to enable (
yes) or disable (no) the PAM authentication. For example:USEPAMACCESS=no
-
USESSSDAUTH=boolean - A boolean to enable (
yes) or disable (no) the SSSD authentication. For example:USESSSDAUTH=no
-
USESHADOW=boolean - A boolean to enable (
yes) or disable (no) shadow passwords. For example:USESHADOW=yes
-
USEWINBIND=boolean - A boolean to enable (
yes) or disable (no) using Winbind for user account configuration. For example:USEWINBIND=no
-
USEDB=boolean - A boolean to enable (
yes) or disable (no) the FAS authentication. For example:USEDB=no
-
USEFPRINTD=boolean - A boolean to enable (
yes) or disable (no) the fingerprint authentication. For example:USEFPRINTD=yes
-
FORCESMARTCARD=boolean - A boolean to enable (
yes) or disable (no) enforcing the smart card authentication. For example:FORCESMARTCARD=no
-
PASSWDALGORITHM=value - The password algorithm. The
valuecan bebigcrypt,descrypt,md5,sha256, orsha512. For example:PASSWDALGORITHM=sha512
-
USELDAPAUTH=boolean - A boolean to enable (
yes) or disable (no) the LDAP authentication. For example:USELDAPAUTH=no
-
USELOCAUTHORIZE=boolean - A boolean to enable (
yes) or disable (no) the local authorization for local users. For example:USELOCAUTHORIZE=yes
-
USECRACKLIB=boolean - A boolean to enable (
yes) or disable (no) using the CrackLib. For example:USECRACKLIB=yes
-
USEWINBINDAUTH=boolean - A boolean to enable (
yes) or disable (no) the Winbind authentication. For example:USEWINBINDAUTH=no
-
USESMARTCARD=boolean - A boolean to enable (
yes) or disable (no) the smart card authentication. For example:USESMARTCARD=no
-
USELDAP=boolean - A boolean to enable (
yes) or disable (no) using LDAP for user account configuration. For example:USELDAP=no
-
USENIS=boolean - A boolean to enable (
yes) or disable (no) using NIS for user account configuration. For example:USENIS=no
-
USEKERBEROS=boolean - A boolean to enable (
yes) or disable (no) the Kerberos authentication. For example:USEKERBEROS=no
-
USESYSNETAUTH=boolean - A boolean to enable (
yes) or disable (no) authenticating system accounts with network services. For example:USESYSNETAUTH=no
-
USESMBAUTH=boolean - A boolean to enable (
yes) or disable (no) the SMB authentication. For example:USESMBAUTH=no
-
USESSSD=boolean - A boolean to enable (
yes) or disable (no) using SSSD for obtaining user information. For example:USESSSD=no
-
USEHESIOD=boolean - A boolean to enable (
yes) or disable (no) using the Hesoid name service. For example:USEHESIOD=no
18.1.3. /etc/sysconfig/autofs
/etc/sysconfig/autofs file defines
custom options for the automatic mounting of devices. This file
controls the operation of the automount daemons, which automatically
mount file systems when you use them and unmount them after a period of
inactivity. File systems can include network file systems, CD-ROM
drives, diskettes, and other media.
-
MASTER_MAP_NAME=value - The default name for the master map. For example:
MASTER_MAP_NAME="auto.master"
-
TIMEOUT=value - The default mount timeout. For example:
TIMEOUT=300
-
NEGATIVE_TIMEOUT=value - The default negative timeout for unsuccessful mount attempts. For example:
NEGATIVE_TIMEOUT=60
-
MOUNT_WAIT=value - The time to wait for a response from
mount. For example:MOUNT_WAIT=-1
-
UMOUNT_WAIT=value - The time to wait for a response from
umount. For example:UMOUNT_WAIT=12
-
BROWSE_MODE=boolean - A boolean to enable (
yes) or disable (no) browsing the maps. For example:BROWSE_MODE="no"
-
MOUNT_NFS_DEFAULT_PROTOCOL=value - The default protocol to be used by
mount.nfs. For example:MOUNT_NFS_DEFAULT_PROTOCOL=4
-
APPEND_OPTIONS=boolean - A boolean to enable (
yes) or disable (no) appending the global options instead of replacing them. For example:APPEND_OPTIONS="yes"
-
LOGGING=value - The default logging level. The
valuehas to be eithernone,verbose, ordebug. For example:LOGGING="none"
-
LDAP_URI=value - A space-separated list of server URIs in the form of
protocol://serverLDAP_URI="ldaps://ldap.example.com/"
-
LDAP_TIMEOUT=value - The synchronous API calls timeout. For example:
LDAP_TIMEOUT=-1
-
LDAP_NETWORK_TIMEOUT=value - The network response timeout. For example:
LDAP_NETWORK_TIMEOUT=8
-
SEARCH_BASE=value - The base Distinguished Name (DN) for the map search. For example:
SEARCH_BASE=""
-
AUTH_CONF_FILE=value - The default location of the SASL authentication configuration file. For example:
AUTH_CONF_FILE="/etc/autofs_ldap_auth.conf"
-
MAP_HASH_TABLE_SIZE=value - The hash table size for the map cache. For example:
MAP_HASH_TABLE_SIZE=1024
-
USE_MISC_DEVICE=boolean - A boolean to enable (
yes) or disable (no) using the autofs miscellaneous device. For example:USE_MISC_DEVICE="yes"
-
OPTIONS=value - Additional options to be passed to the LDAP daemon. For example:
OPTIONS=""
18.1.4. /etc/sysconfig/clock
/etc/sysconfig/clock file controls the interpretation of values read from the system hardware clock. It is used by the Date/Time Properties tool, and should not be edited by hand. By default, it contains the following option:
-
ZONE=value - The time zone file under
/usr/share/zoneinfothat/etc/localtimeis a copy of. For example:ZONE="Europe/Prague"
18.1.5. /etc/sysconfig/dhcpd
/etc/sysconfig/dhcpd file is used to pass arguments to the dhcpd daemon at boot time. By default, it contains the following options:
-
DHCPDARGS=value - Additional options to be passed to the
dhcpddaemon. For example:DHCPDARGS=
18.1.6. /etc/sysconfig/firstboot
/etc/sysconfig/firstboot file defines whether to run the firstboot utility. By default, it contains the following option:
-
RUN_FIRSTBOOT=boolean - A boolean to enable (
YES) or disable (NO) running thefirstbootprogram. For example:RUN_FIRSTBOOT=NO
init program calls the /etc/rc.d/init.d/firstboot script, which looks for the /etc/sysconfig/firstboot file. If this file does not contain the RUN_FIRSTBOOT=NO option, the firstboot program is run, guiding a user through the initial configuration of the system.
Tip: You Can Run the firstboot Program Again
firstboot program the next time the system boots, change the value of RUN_FIRSTBOOT option to YES, and type the following at a shell prompt:
~]# chkconfig firstboot on18.1.7. /etc/sysconfig/i18n
/etc/sysconfig/i18n configuration
file defines the default language, any supported languages, and the
default system font. By default, it contains the following options:
-
LANG=value - The default language. For example:
LANG="en_US.UTF-8"
-
SUPPORTED=value - A colon-separated list of supported languages. For example:
SUPPORTED="en_US.UTF-8:en_US:en"
-
SYSFONT=value - The default system font. For example:
SYSFONT="latarcyrheb-sun16"
18.1.8. /etc/sysconfig/init
/etc/sysconfig/init file controls how the system appears and functions during the boot process. By default, it contains the following options:
-
BOOTUP=value - The bootup style. The value has to be either
color(the standard color boot display),verbose(an old style display which provides more information), or anything else for the new style display, but without ANSI formatting. For example:BOOTUP=color
-
RES_COL=value - The number of the column in which the status labels start. For example:
RES_COL=60
-
MOVE_TO_COL=value - The terminal sequence to move the cursor to the column specified in
RES_COL(see above). For example:MOVE_TO_COL="echo -en \\033[${RES_COL}G" -
SETCOLOR_SUCCESS=value - The terminal sequence to set the success color. For example:
SETCOLOR_SUCCESS="echo -en \\033[0;32m"
-
SETCOLOR_FAILURE=value - The terminal sequence to set the failure color. For example:
SETCOLOR_FAILURE="echo -en \\033[0;31m"
-
SETCOLOR_WARNING=value - The terminal sequence to set the warning color. For example:
SETCOLOR_WARNING="echo -en \\033[0;33m"
-
SETCOLOR_NORMAL=value - The terminal sequence to set the default color. For example:
SETCOLOR_NORMAL="echo -en \\033[0;39m"
-
LOGLEVEL=value - The initial console logging level. The
valuehas to be in the range from1(kernel panics only) to8(everything, including the debugging information). For example:LOGLEVEL=3
-
PROMPT=boolean - A boolean to enable (
yes) or disable (no) the hotkey interactive startup. For example:PROMPT=yes
-
AUTOSWAP=boolean - A boolean to enable (
yes) or disable (no) probing for devices with swap signatures. For example:AUTOSWAP=no
-
ACTIVE_CONSOLES=value - The list of active consoles. For example:
ACTIVE_CONSOLES=/dev/tty[1-6]
-
SINGLE=value - The single-user mode type. The
valuehas to be either/sbin/sulogin(a user will be prompted for a password to log in), or/sbin/sushell(the user will be logged in directly). For example:SINGLE=/sbin/sushell
18.1.9. /etc/sysconfig/ip6tables-config
/etc/sysconfig/ip6tables-config file stores information used by the kernel to set up IPv6 packet filtering at boot time or whenever the ip6tables service is started. Note that you should not modify it unless you are familiar with ip6tables rules. By default, it contains the following options:
-
IP6TABLES_MODULES=value - A space-separated list of helpers to be loaded after the firewall rules are applied. For example:
IP6TABLES_MODULES="ip_nat_ftp ip_nat_irc"
-
IP6TABLES_MODULES_UNLOAD=boolean - A boolean to enable (
yes) or disable (no) module unloading when the firewall is stopped or restarted. For example:IP6TABLES_MODULES_UNLOAD="yes"
-
IP6TABLES_SAVE_ON_STOP=boolean - A boolean to enable (
yes) or disable (no) saving the current firewall rules when the firewall is stopped. For example:IP6TABLES_SAVE_ON_STOP="no"
-
IP6TABLES_SAVE_ON_RESTART=boolean - A boolean to enable (
yes) or disable (no) saving the current firewall rules when the firewall is restarted. For example:IP6TABLES_SAVE_ON_RESTART="no"
-
IP6TABLES_SAVE_COUNTER=boolean - A boolean to enable (
yes) or disable (no) saving the rule and chain counters. For example:IP6TABLES_SAVE_COUNTER="no"
-
IP6TABLES_STATUS_NUMERIC=boolean - A boolean to enable (
yes) or disable (no) printing IP addresses and port numbers in a numeric format in the status output. For example:IP6TABLES_STATUS_NUMERIC="yes"
-
IP6TABLES_STATUS_VERBOSE=boolean - A boolean to enable (
yes) or disable (no) printing information about the number of packets and bytes in the status output. For example:IP6TABLES_STATUS_VERBOSE="no"
-
IP6TABLES_STATUS_LINENUMBERS=boolean - A boolean to enable (
yes) or disable (no) printing line numbers in the status output. For example:IP6TABLES_STATUS_LINENUMBERS="yes"
Tip: Use the ip6tables Command to Create the Rules
ip6tables command. Once created, type the following at a shell prompt:
~]# service ip6tables save/etc/sysconfig/ip6tables. Once this file exists, any firewall rules saved in it persist through a system reboot or a service restart.
18.1.10. /etc/sysconfig/keyboard
/etc/sysconfig/keyboard file controls the behavior of the keyboard. By default, it contains the following options:
-
KEYTABLE=value - The name of a keytable file. The files that can be used as keytables start in the
/lib/kbd/keymaps/i386/directory, and branch into different keyboard layouts from there, all labeledvalue.kmap.gzKEYTABLEsetting is used. For example:KEYTABLE="us"
-
MODEL=value - The keyboard model. For example:
MODEL="pc105+inet"
-
LAYOUT=value - The keyboard layout. For example:
LAYOUT="us"
-
KEYBOARDTYPE=value - The keyboard type. Allowed values are
pc(a PS/2 keyboard), orsun(a Sun keyboard). For example:KEYBOARDTYPE="pc"
18.1.11. /etc/sysconfig/ldap
/etc/sysconfig/ldap file holds the basic configuration for the LDAP server. By default, it contains the following options:
-
SLAPD_OPTIONS=value - Additional options to be passed to the
slapddaemon. For example:SLAPD_OPTIONS="-4"
-
SLURPD_OPTIONS=value - Additional options to be passed to the
slurpddaemon. For example:SLURPD_OPTIONS=""
-
SLAPD_LDAP=boolean - A boolean to enable (
yes) or disable (no) using the LDAP over TCP (that is,ldap:///). For example:SLAPD_LDAP="yes"
-
SLAPD_LDAPI=boolean - A boolean to enable (
yes) or disable (no) using the LDAP over IPC (that is,ldapi:///). For example:SLAPD_LDAPI="no"
-
SLAPD_LDAPS=boolean - A boolean to enable (
yes) or disable (no) using the LDAP over TLS (that is,ldaps:///). For example:SLAPD_LDAPS="no"
-
SLAPD_URLS=value - A space-separated list of URLs. For example:
SLAPD_URLS="ldapi:///var/lib/ldap_root/ldapi ldapi:/// ldaps:///"
-
SLAPD_SHUTDOWN_TIMEOUT=value - The time to wait for
slapdto shut down. For example:SLAPD_SHUTDOWN_TIMEOUT=3
-
SLAPD_ULIMIT_SETTINGS=value - The parameters to be passed to
ulimitbefore theslapddaemon is started. For example:SLAPD_ULIMIT_SETTINGS=""
18.1.12. /etc/sysconfig/named
/etc/sysconfig/named file is used to pass arguments to the named daemon at boot time. By default, it contains the following options:
-
ROOTDIR=value - The chroot environment under which the
nameddaemon runs. Thevaluehas to be a full directory path. For example:ROOTDIR="/var/named/chroot"
Note that the chroot environment has to be configured first (typeinfo chrootat a shell prompt for more information). -
OPTIONS=value - Additional options to be passed to
named. For example:OPTIONS="-6"
Note that you should not use the-toption. Instead, useROOTDIRas described above. -
KEYTAB_FILE=value - The keytab filename. For example:
KEYTAB_FILE="/etc/named.keytab"
18.1.13. /etc/sysconfig/network
/etc/sysconfig/network file is used to specify information about the desired network configuration. By default, it contains the following options:
-
NETWORKING=boolean - A boolean to enable (
yes) or disable (no) the networking. For example:NETWORKING=yes
-
HOSTNAME=value - The hostname of the machine. For example:
HOSTNAME=penguin.example.com
-
GATEWAY=value - The IP address of the network's gateway. For example:
GATEWAY=192.168.1.0
Warning: Avoid Using Custom Init Scripts
18.1.14. /etc/sysconfig/ntpd
/etc/sysconfig/ntpd file is used to pass arguments to the ntpd daemon at boot time. By default, it contains the following option:
-
OPTIONS=value - Additional options to be passed to
ntpd. For example:OPTIONS="-u ntp:ntp -p /var/run/ntpd.pid -g"
ntpd daemon.
18.1.15. /etc/sysconfig/quagga
/etc/sysconfig/quagga file holds the basic configuration for Quagga daemons. By default, it contains the following options:
-
QCONFDIR=value - The directory with the configuration files for Quagga daemons. For example:
QCONFDIR="/etc/quagga"
-
BGPD_OPTS=value - Additional options to be passed to the
bgpddaemon. For example:BGPD_OPTS="-A 127.0.0.1 -f ${QCONFDIR}/bgpd.conf" -
OSPF6D_OPTS=value - Additional options to be passed to the
ospf6ddaemon. For example:OSPF6D_OPTS="-A ::1 -f ${QCONFDIR}/ospf6d.conf" -
OSPFD_OPTS=value - Additional options to be passed to the
ospfddaemon. For example:OSPFD_OPTS="-A 127.0.0.1 -f ${QCONFDIR}/ospfd.conf" -
RIPD_OPTS=value - Additional options to be passed to the
ripddaemon. For example:RIPD_OPTS="-A 127.0.0.1 -f ${QCONFDIR}/ripd.conf" -
RIPNGD_OPTS=value - Additional options to be passed to the
ripngddaemon. For example:RIPNGD_OPTS="-A ::1 -f ${QCONFDIR}/ripngd.conf" -
ZEBRA_OPTS=value - Additional options to be passed to the
zebradaemon. For example:ZEBRA_OPTS="-A 127.0.0.1 -f ${QCONFDIR}/zebra.conf" -
ISISD_OPTS=value - Additional options to be passed to the
isisddaemon. For example:ISISD_OPTS="-A ::1 -f ${QCONFDIR}/isisd.conf" -
WATCH_OPTS=value - Additional options to be passed to the
watchquaggadaemon. For example:WATCH_OPTS="-Az -b_ -r/sbin/service_%s_restart -s/sbin/service_%s_start -k/sbin/service_%s_stop"
-
WATCH_DAEMONS=value - A space separated list of monitored daemons. For example:
WATCH_DAEMONS="zebra bgpd ospfd ospf6d ripd ripngd"
18.1.16. /etc/sysconfig/radvd
/etc/sysconfig/radvd file is used to pass arguments to the radvd daemon at boot time. By default, it contains the following option:
-
OPTIONS=value - Additional options to be passed to the
radvddaemon. For example:OPTIONS="-u radvd"
18.1.17. /etc/sysconfig/samba
/etc/sysconfig/samba file is used to pass arguments to the Samba daemons at boot time. By default, it contains the following options:
-
SMBDOPTIONS=value - Additional options to be passed to
smbd. For example:SMBDOPTIONS="-D"
-
NMBDOPTIONS=value - Additional options to be passed to
nmbd. For example:NMBDOPTIONS="-D"
-
WINBINDOPTIONS=value - Additional options to be passed to
winbindd. For example:WINBINDOPTIONS=""
18.1.18. /etc/sysconfig/selinux
/etc/sysconfig/selinux file contains the basic configuration options for SELinux. It is a symbolic link to /etc/selinux/config, and by default, it contains the following options:
-
SELINUX=value - The security policy. The
valuecan be eitherenforcing(the security policy is always enforced),permissive(instead of enforcing the policy, appropriate warnings are displayed), ordisabled(no policy is used). For example:SELINUX=enforcing
-
SELINUXTYPE=value - The protection type. The
valuecan be eithertargeted(the targeted processes are protected), ormls(the Multi Level Security protection). For example:SELINUXTYPE=targeted
18.1.19. /etc/sysconfig/sendmail
/etc/sysconfig/sendmail is used to set the default values for the Sendmail application. By default, it contains the following values:
-
DAEMON=boolean - A boolean to enable (
yes) or disable (no) runningsendmailas a daemon. For example:DAEMON=yes
-
QUEUE=value - The interval at which the messages are to be processed. For example:
QUEUE=1h
18.1.20. /etc/sysconfig/spamassassin
/etc/sysconfig/spamassassin file is used to pass arguments to the spamd daemon (a daemonized version of Spamassassin) at boot time. By default, it contains the following option:
-
SPAMDOPTIONS=value - Additional options to be passed to the
spamddaemon. For example:SPAMDOPTIONS="-d -c -m5 -H"
18.1.21. /etc/sysconfig/squid
/etc/sysconfig/squid file is used to pass arguments to the squid daemon at boot time. By default, it contains the following options:
-
SQUID_OPTS=value - Additional options to be passed to the
squiddaemon. For example:SQUID_OPTS=""
-
SQUID_SHUTDOWN_TIMEOUT=value - The time to wait for
squiddaemon to shut down. For example:SQUID_SHUTDOWN_TIMEOUT=100
-
SQUID_CONF=value - The default configuration file. For example:
SQUID_CONF="/etc/squid/squid.conf"
18.1.22. /etc/sysconfig/system-config-users
/etc/sysconfig/system-config-users file is the configuration file for the User Manager utility, and should not be edited by hand. By default, it contains the following options:
-
FILTER=boolean - A boolean to enable (
true) or disable (false) filtering of system users. For example:FILTER=true
-
ASSIGN_HIGHEST_UID=boolean - A boolean to enable (
true) or disable (false) assigning the highest available UID to newly added users. For example:ASSIGN_HIGHEST_UID=true
-
ASSIGN_HIGHEST_GID=boolean - A boolean to enable (
true) or disable (false) assigning the highest available GID to newly added groups. For example:ASSIGN_HIGHEST_GID=true
-
PREFER_SAME_UID_GID=boolean - A boolean to enable (
true) or disable (false) using the same UID and GID for newly added users when possible. For example:PREFER_SAME_UID_GID=true
18.1.23. /etc/sysconfig/vncservers
/etc/sysconfig/vncservers file configures the way the Virtual Network Computing (VNC) server starts up. By default, it contains the following options:
-
VNCSERVERS=value - A list of space separated
display:usernameVNCSERVERS="2:myusername"
-
VNCSERVERARGS[display]=value - Additional arguments to be passed to the VNC server running on the specified
display. For example:VNCSERVERARGS[2]="-geometry 800x600 -nolisten tcp -localhost"
18.1.24. /etc/sysconfig/xinetd
/etc/sysconfig/xinetd file is used to pass arguments to the xinetd daemon at boot time. By default, it contains the following options:
-
EXTRAOPTIONS=value - Additional options to be passed to
xinetd. For example:EXTRAOPTIONS=""
-
XINETD_LANG=value - The locale information to be passed to every service started by
xinetd. Note that to remove locale information from thexinetdenvironment, you can use an empty string ("") ornone. For example:XINETD_LANG="en_US"
xinetd services.
18.2. Directories in the /etc/sysconfig/ Directory
/etc/sysconfig/.
-
/etc/sysconfig/cbq/ -
/etc/sysconfig/networking/ - This directory is used by the Network Administration Tool (
system-config-network), and its contents should not be edited manually. For more information about configuring network interfaces using the Network Administration Tool, refer to Chapter 5, Network Configuration. -
/etc/sysconfig/network-scripts/ - Network configuration files for each configured network interface, such as
ifcfg-eth0for theeth0Ethernet interface. - Scripts used to bring network interfaces up and down, such as
ifupandifdown. - Scripts used to bring ISDN interfaces up and down, such as
ifup-isdnandifdown-isdn. - Various shared network function scripts which should not be edited directly.
For more information on the/etc/sysconfig/network-scripts/directory, refer to Chapter 4, Network Interfaces.-
/etc/sysconfig/rhn/ - This directory contains the configuration files and GPG keys for Red Hat Network. No files in this directory should be edited by hand. For more information on Red Hat Network, refer to the Red Hat Network website online at https://rhn.redhat.com/.
Chapter 19. The proc File System
- 19.1. A Virtual File System
- 19.2. Top-level Files within the
procFile System - 19.2.1.
/proc/buddyinfo - 19.2.2.
/proc/cmdline - 19.2.3.
/proc/cpuinfo - 19.2.4.
/proc/crypto - 19.2.5.
/proc/devices - 19.2.6.
/proc/dma - 19.2.7.
/proc/execdomains - 19.2.8.
/proc/fb - 19.2.9.
/proc/filesystems - 19.2.10.
/proc/interrupts - 19.2.11.
/proc/iomem - 19.2.12.
/proc/ioports - 19.2.13.
/proc/kcore - 19.2.14.
/proc/kmsg - 19.2.15.
/proc/loadavg - 19.2.16.
/proc/locks - 19.2.17.
/proc/mdstat - 19.2.18.
/proc/meminfo - 19.2.19.
/proc/misc - 19.2.20.
/proc/modules - 19.2.21.
/proc/mounts - 19.2.22.
/proc/mtrr - 19.2.23.
/proc/partitions - 19.2.24.
/proc/slabinfo - 19.2.25.
/proc/stat - 19.2.26.
/proc/swaps - 19.2.27.
/proc/sysrq-trigger - 19.2.28.
/proc/uptime - 19.2.29.
/proc/version
- 19.2.1.
- 19.3. Directories within
/proc/ - 19.4. Using the
sysctlCommand - 19.5. References
/proc/ directory (also called the proc
file system) contains a hierarchy of special files which represent the
current state of the kernel, allowing applications and users to peer
into the kernel's view of the system.
/proc/ directory contains a wealth
of information detailing system hardware and any running processes. In
addition, some of the files within /proc/ can be manipulated by users and applications to communicate configuration changes to the kernel.
Note
/proc/ide/ and /proc/pci/ directories obsolete. The /proc/ide/ file system is now superseded by files in sysfs; to retrieve information on PCI devices, use lspci instead. For more information on sysfs or lspci, refer to their respective man pages.
19.1. A Virtual File System
/proc/ directory contains another type of file called a virtual file. As such, /proc/ is often referred to as a virtual file system.
/proc/interrupts, /proc/meminfo, /proc/mounts, and /proc/partitions provide an up-to-the-moment glimpse of the system's hardware. Others, like the /proc/filesystems file and the /proc/sys/ directory provide system configuration information and interfaces.
19.1.1. Viewing Virtual Files
/proc/ files operate
similarly to text files, storing useful system and hardware data in
human-readable text format. As such, you can use cat, more, or less to view them. For example, to display information about the system's CPU, run cat /proc/cpuinfo. This will return output similar to the following:
processor : 0 vendor_id : AuthenticAMD cpu family : 5 model : 9 model name : AMD-K6(tm) 3D+ Processor stepping : 1 cpu MHz : 400.919 cache size : 256 KB fdiv_bug : no hlt_bug : no f00f_bug : no coma_bug : no fpu : yes fpu_exception : yes cpuid level : 1 wp : yes flags : fpu vme de pse tsc msr mce cx8 pge mmx syscall 3dnow k6_mtrr bogomips : 799.53
/proc/ contain information that is not human-readable. To retrieve information from such files, use tools such as lspci, apm, free, and top.
Note
/proc/ directory are readable only by the root user.
19.1.2. Changing Virtual Files
/proc/ directory are read-only. However, some can be used to adjust settings in the kernel. This is especially true for files in the /proc/sys/ subdirectory.
echo value > /proc/file
echo www.example.com > /proc/sys/kernel/hostname
cat /proc/sys/net/ipv4/ip_forward returns either a 0 (off or false) or a 1 (on or true). A 0 indicates that the kernel is not forwarding network packets. To turn packet forwarding on, run echo 1 > /proc/sys/net/ipv4/ip_forward.
Tip
/proc/sys/ subdirectory is /sbin/sysctl. For more information on this command, refer to Section 19.4, “Using the sysctl Command”
/proc/sys/ subdirectory, refer to Section 19.3.9, “ /proc/sys/ ”.
19.2. Top-level Files within the proc File System
/proc/ directory.
Note
19.2.1. /proc/buddyinfo
DMA row references the first 16 MB on a system, the HighMem row references all memory greater than 4 GB on a system, and the Normal row references all memory in between.
/proc/buddyinfo:
Node 0, zone DMA 90 6 2 1 1 ... Node 0, zone Normal 1650 310 5 0 0 ... Node 0, zone HighMem 2 0 0 1 1 ...
19.2.2. /proc/cmdline
/proc/cmdline file looks like the following:
ro root=/dev/VolGroup00/LogVol00 rhgb quiet 3
(ro)), located on the first logical volume (LogVol00) of the first volume group (/dev/VolGroup00). LogVol00 is the equivalent of a disk partition in a non-LVM system (Logical Volume Management), just as /dev/VolGroup00 is similar in concept to /dev/hda1, but much more extensible.
rhgb signals that the rhgb package has been installed, and graphical booting is supported, assuming /etc/inittab shows a default runlevel set to id:5:initdefault:.
quiet indicates all verbose kernel messages are suppressed at boot time.
19.2.3. /proc/cpuinfo
/proc/cpuinfo:
processor : 0 vendor_id : GenuineIntel cpu family : 15 model : 2 model name : Intel(R) Xeon(TM) CPU 2.40GHz stepping : 7 cpu MHz : 2392.371 cache size : 512 KB physical id : 0 siblings : 2 runqueue : 0 fdiv_bug : no hlt_bug : no f00f_bug : no coma_bug : no fpu : yes fpu_exception : yes cpuid level : 2 wp : yes flags : fpu vme de pse tsc msr pae mce cx8 apic sep mtrr pge mca cmov pat pse36 clflush dts acpi mmx fxsr sse sse2 ss ht tm bogomips : 4771.02
processor— Provides each processor with an identifying number. On systems that have one processor, only a0is present.cpu family— Authoritatively identifies the type of processor in the system. For an Intel-based system, place the number in front of "86" to determine the value. This is particularly helpful for those attempting to identify the architecture of an older system such as a 586, 486, or 386. Because some RPM packages are compiled for each of these particular architectures, this value also helps users determine which packages to install.model name— Displays the common name of the processor, including its project name.cpu MHz— Shows the precise speed in megahertz for the processor to the thousandths decimal place.cache size— Displays the amount of level 2 memory cache available to the processor.siblings— Displays the number of sibling CPUs on the same physical CPU for architectures which use hyper-threading.flags— Defines a number of different qualities about the processor, such as the presence of a floating point unit (FPU) and the ability to process MMX instructions.
19.2.4. /proc/crypto
/proc/crypto file looks like the following:
name : sha1 module : kernel type : digest blocksize : 64 digestsize : 20 name : md5 module : md5 type : digest blocksize : 64 digestsize : 16
19.2.5. /proc/devices
Character devices: 1 mem 4 /dev/vc/0 4 tty 4 ttyS 5 /dev/tty 5 /dev/console 5 /dev/ptmx 7 vcs 10 misc 13 input 29 fb 36 netlink 128 ptm 136 pts 180 usb Block devices: 1 ramdisk 3 ide0 9 md 22 ide1 253 device-mapper 254 mdp
/proc/devices includes the major number and name of the device, and is broken into two major sections: Character devices and Block devices.
- Character devices do not require buffering. Block devices have a buffer available, allowing them to order requests before addressing them. This is important for devices designed to store information — such as hard drives — because the ability to order the information before writing it to the device allows it to be placed in a more efficient order.
- Character devices send data with no preconfigured size. Block devices can send and receive information in blocks of a size configured per device.
/usr/share/doc/kernel-doc-<kernel_version>/Documentation/devices.txt19.2.6. /proc/dma
/proc/dma files looks like the following:
4: cascade
19.2.7. /proc/execdomains
0-0 Linux [kernel]
PER_LINUX execution domain, different personalities can be implemented as dynamically loadable modules.
19.2.8. /proc/fb
/proc/fb for systems which contain frame buffer devices looks similar to the following:
0 VESA VGA
19.2.9. /proc/filesystems
/proc/filesystems file looks similar to the following:
nodev sysfs nodev rootfs nodev bdev nodev proc nodev sockfs nodev binfmt_misc nodev usbfs nodev usbdevfs nodev futexfs nodev tmpfs nodev pipefs nodev eventpollfs nodev devpts ext2 nodev ramfs nodev hugetlbfs iso9660 nodev mqueue ext3 nodev rpc_pipefs nodev autofs
nodev are not mounted on a device. The second column lists the names of the file systems supported.
mount command cycles through the file systems listed here when one is not specified as an argument.
19.2.10. /proc/interrupts
/proc/interrupts looks similar to the following:
CPU0 0: 80448940 XT-PIC timer 1: 174412 XT-PIC keyboard 2: 0 XT-PIC cascade 8: 1 XT-PIC rtc 10: 410964 XT-PIC eth0 12: 60330 XT-PIC PS/2 Mouse 14: 1314121 XT-PIC ide0 15: 5195422 XT-PIC ide1 NMI: 0 ERR: 0
CPU0 CPU1 0: 1366814704 0 XT-PIC timer 1: 128 340 IO-APIC-edge keyboard 2: 0 0 XT-PIC cascade 8: 0 1 IO-APIC-edge rtc 12: 5323 5793 IO-APIC-edge PS/2 Mouse 13: 1 0 XT-PIC fpu 16: 11184294 15940594 IO-APIC-level Intel EtherExpress Pro 10/100 Ethernet 20: 8450043 11120093 IO-APIC-level megaraid 30: 10432 10722 IO-APIC-level aic7xxx 31: 23 22 IO-APIC-level aic7xxx NMI: 0 ERR: 0
XT-PIC— This is the old AT computer interrupts.IO-APIC-edge— The voltage signal on this interrupt transitions from low to high, creating an edge, where the interrupt occurs and is only signaled once. This kind of interrupt, as well as theIO-APIC-levelinterrupt, are only seen on systems with processors from the 586 family and higher.IO-APIC-level— Generates interrupts when its voltage signal is high until the signal is low again.
19.2.11. /proc/iomem
00000000-0009fbff : System RAM 0009fc00-0009ffff : reserved 000a0000-000bffff : Video RAM area 000c0000-000c7fff : Video ROM 000f0000-000fffff : System ROM 00100000-07ffffff : System RAM 00100000-00291ba8 : Kernel code 00291ba9-002e09cb : Kernel data e0000000-e3ffffff : VIA Technologies, Inc. VT82C597 [Apollo VP3] e4000000-e7ffffff : PCI Bus #01 e4000000-e4003fff : Matrox Graphics, Inc. MGA G200 AGP e5000000-e57fffff : Matrox Graphics, Inc. MGA G200 AGP e8000000-e8ffffff : PCI Bus #01 e8000000-e8ffffff : Matrox Graphics, Inc. MGA G200 AGP ea000000-ea00007f : Digital Equipment Corporation DECchip 21140 [FasterNet] ea000000-ea00007f : tulip ffff0000-ffffffff : reserved
19.2.12. /proc/ioports
/proc/ioports provides a
list of currently registered port regions used for input or output
communication with a device. This file can be quite long. The following
is a partial listing:
0000-001f : dma1 0020-003f : pic1 0040-005f : timer 0060-006f : keyboard 0070-007f : rtc 0080-008f : dma page reg 00a0-00bf : pic2 00c0-00df : dma2 00f0-00ff : fpu 0170-0177 : ide1 01f0-01f7 : ide0 02f8-02ff : serial(auto) 0376-0376 : ide1 03c0-03df : vga+ 03f6-03f6 : ide0 03f8-03ff : serial(auto) 0cf8-0cff : PCI conf1 d000-dfff : PCI Bus #01 e000-e00f : VIA Technologies, Inc. Bus Master IDE e000-e007 : ide0 e008-e00f : ide1 e800-e87f : Digital Equipment Corporation DECchip 21140 [FasterNet] e800-e87f : tulip
19.2.13. /proc/kcore
/proc/ files, kcore displays a size. This value is given in bytes and is equal to the size of the physical memory (RAM) used plus 4 KB.
gdb, and is not human readable.
Caution
/proc/kcore virtual file. The contents of the file scramble text output on the terminal. If this file is accidentally viewed, press Ctrl+C to stop the process and then type reset to bring back the command line prompt.
19.2.14. /proc/kmsg
/sbin/klogd or /bin/dmesg.
19.2.15. /proc/loadavg
uptime and other commands. A sample /proc/loadavg file looks similar to the following:
0.20 0.18 0.12 1/80 11206
19.2.16. /proc/locks
/proc/locks file for a lightly loaded system looks similar to the following:
1: POSIX ADVISORY WRITE 3568 fd:00:2531452 0 EOF 2: FLOCK ADVISORY WRITE 3517 fd:00:2531448 0 EOF 3: POSIX ADVISORY WRITE 3452 fd:00:2531442 0 EOF 4: POSIX ADVISORY WRITE 3443 fd:00:2531440 0 EOF 5: POSIX ADVISORY WRITE 3326 fd:00:2531430 0 EOF 6: POSIX ADVISORY WRITE 3175 fd:00:2531425 0 EOF 7: POSIX ADVISORY WRITE 3056 fd:00:2548663 0 EOF
FLOCK signifying the older-style UNIX file locks from a flock system call and POSIX representing the newer POSIX locks from the lockf system call.
ADVISORY or MANDATORY. ADVISORY means that the lock does not prevent other people from accessing the data; it only prevents other attempts to lock it. MANDATORY
means that no other access to the data is permitted while the lock is
held. The fourth column reveals whether the lock is allowing the holder READ or WRITE
access to the file. The fifth column shows the ID of the process
holding the lock. The sixth column shows the ID of the file being
locked, in the format of MAJOR-DEVICE:MINOR-DEVICE:INODE-NUMBER 19.2.17. /proc/mdstat
/proc/mdstat looks similar to the following:
Personalities : read_ahead not set unused devices: <none>
md device is present. In that case, view /proc/mdstat to find the current status of mdX RAID devices.
/proc/mdstat file below shows a system with its md0 configured as a RAID 1 device, while it is currently re-syncing the disks:
Personalities : [linear] [raid1] read_ahead 1024 sectors md0: active raid1 sda2[1] sdb2[0] 9940 blocks [2/2] [UU] resync=1% finish=12.3min algorithm 2 [3/3] [UUU] unused devices: <none>
19.2.18. /proc/meminfo
/proc/ directory, as it reports a large amount of valuable information about the systems RAM usage.
/proc/meminfo virtual file is from a system with 256 MB of RAM and 512 MB of swap space:
MemTotal: 255908 kB MemFree: 69936 kB Buffers: 15812 kB Cached: 115124 kB SwapCached: 0 kB Active: 92700 kB Inactive: 63792 kB HighTotal: 0 kB HighFree: 0 kB LowTotal: 255908 kB LowFree: 69936 kB SwapTotal: 524280 kB SwapFree: 524280 kB Dirty: 4 kB Writeback: 0 kB Mapped: 42236 kB Slab: 25912 kB Committed_AS: 118680 kB PageTables: 1236 kB VmallocTotal: 3874808 kB VmallocUsed: 1416 kB VmallocChunk: 3872908 kB HugePages_Total: 0 HugePages_Free: 0 Hugepagesize: 4096 kB
free, top, and ps commands. In fact, the output of the free command is similar in appearance to the contents and structure of /proc/meminfo. But by looking directly at /proc/meminfo, more details are revealed:
MemTotal— Total amount of physical RAM, in kilobytes.MemFree— The amount of physical RAM, in kilobytes, left unused by the system.Buffers— The amount of physical RAM, in kilobytes, used for file buffers.Cached— The amount of physical RAM, in kilobytes, used as cache memory.SwapCached— The amount of swap, in kilobytes, used as cache memory.Active— The total amount of buffer or page cache memory, in kilobytes, that is in active use. This is memory that has been recently used and is usually not reclaimed for other purposes.Inactive— The total amount of buffer or page cache memory, in kilobytes, that are free and available. This is memory that has not been recently used and can be reclaimed for other purposes.HighTotalandHighFree— The total and free amount of memory, in kilobytes, that is not directly mapped into kernel space. TheHighTotalvalue can vary based on the type of kernel used.LowTotalandLowFree— The total and free amount of memory, in kilobytes, that is directly mapped into kernel space. TheLowTotalvalue can vary based on the type of kernel used.SwapTotal— The total amount of swap available, in kilobytes.SwapFree— The total amount of swap free, in kilobytes.Dirty— The total amount of memory, in kilobytes, waiting to be written back to the disk.Writeback— The total amount of memory, in kilobytes, actively being written back to the disk.Mapped— The total amount of memory, in kilobytes, which have been used to map devices, files, or libraries using themmapcommand.Slab— The total amount of memory, in kilobytes, used by the kernel to cache data structures for its own use.Committed_AS— The total amount of memory, in kilobytes, estimated to complete the workload. This value represents the worst case scenario value, and also includes swap memory.PageTables— The total amount of memory, in kilobytes, dedicated to the lowest page table level.VMallocTotal— The total amount of memory, in kilobytes, of total allocated virtual address space.VMallocUsed— The total amount of memory, in kilobytes, of used virtual address space.VMallocChunk— The largest contiguous block of memory, in kilobytes, of available virtual address space.HugePages_Total— The total number of hugepages for the system. The number is derived by dividingHugepagesizeby the megabytes set aside for hugepages specified in/proc/sys/vm/hugetlb_pool. This statistic only appears on the x86, Itanium, and AMD64 architectures.HugePages_Free— The total number of hugepages available for the system. This statistic only appears on the x86, Itanium, and AMD64 architectures.Hugepagesize— The size for each hugepages unit in kilobytes. By default, the value is 4096 KB on uniprocessor kernels for 32 bit architectures. For SMP, hugemem kernels, and AMD64, the default is 2048 KB. For Itanium architectures, the default is 262144 KB. This statistic only appears on the x86, Itanium, and AMD64 architectures.
19.2.19. /proc/misc
63 device-mapper 175 agpgart 135 rtc 134 apm_bios
19.2.20. /proc/modules
/proc/modules file output:
Note
/sbin/lsmod command.
nfs 170109 0 - Live 0x129b0000 lockd 51593 1 nfs, Live 0x128b0000 nls_utf8 1729 0 - Live 0x12830000 vfat 12097 0 - Live 0x12823000 fat 38881 1 vfat, Live 0x1287b000 autofs4 20293 2 - Live 0x1284f000 sunrpc 140453 3 nfs,lockd, Live 0x12954000 3c59x 33257 0 - Live 0x12871000 uhci_hcd 28377 0 - Live 0x12869000 md5 3777 1 - Live 0x1282c000 ipv6 211845 16 - Live 0x128de000 ext3 92585 2 - Live 0x12886000 jbd 65625 1 ext3, Live 0x12857000 dm_mod 46677 3 - Live 0x12833000
Live, Loading, or Unloading are the only possible values.
oprofile.
19.2.21. /proc/mounts
rootfs / rootfs rw 0 0 /proc /proc proc rw,nodiratime 0 0 none /dev ramfs rw 0 0 /dev/mapper/VolGroup00-LogVol00 / ext3 rw 0 0 none /dev ramfs rw 0 0 /proc /proc proc rw,nodiratime 0 0 /sys /sys sysfs rw 0 0 none /dev/pts devpts rw 0 0 usbdevfs /proc/bus/usb usbdevfs rw 0 0 /dev/hda1 /boot ext3 rw 0 0 none /dev/shm tmpfs rw 0 0 none /proc/sys/fs/binfmt_misc binfmt_misc rw 0 0 sunrpc /var/lib/nfs/rpc_pipefs rpc_pipefs rw 0 0
/etc/mtab, except that /proc/mounts is more up-to-date.
ro) or read-write (rw). The fifth and sixth columns are dummy values designed to match the format used in /etc/mtab.
19.2.22. /proc/mtrr
/proc/mtrr file may look similar to the following:
reg00: base=0x00000000 ( 0MB), size= 256MB: write-back, count=1 reg01: base=0xe8000000 (3712MB), size= 32MB: write-combining, count=1
/proc/mtrr file can increase performance more than 150%.
/usr/share/doc/kernel-doc-<kernel_version>/Documentation/<arch>/mtrr.txt
19.2.23. /proc/partitions
major minor #blocks name 3 0 19531250 hda 3 1 104391 hda1 3 2 19422585 hda2 253 0 22708224 dm-0 253 1 524288 dm-1
major— The major number of the device with this partition. The major number in the/proc/partitions, (3), corresponds with the block deviceide0, in/proc/devices.minor— The minor number of the device with this partition. This serves to separate the partitions into different physical devices and relates to the number at the end of the name of the partition.#blocks— Lists the number of physical disk blocks contained in a particular partition.name— The name of the partition.
19.2.24. /proc/slabinfo
/proc/slabinfo file manually, the /usr/bin/slabtop
program displays kernel slab cache information in real time. This
program allows for custom configurations, including column sorting and
screen refreshing.
/usr/bin/slabtop usually looks like the following example:
Active / Total Objects (% used) : 133629 / 147300 (90.7%) Active / Total Slabs (% used) : 11492 / 11493 (100.0%) Active / Total Caches (% used) : 77 / 121 (63.6%) Active / Total Size (% used) : 41739.83K / 44081.89K (94.7%) Minimum / Average / Maximum Object : 0.01K / 0.30K / 128.00K OBJS ACTIVE USE OBJ SIZE SLABS OBJ/SLAB CACHE SIZE NAME 44814 43159 96% 0.62K 7469 6 29876K ext3_inode_cache 36900 34614 93% 0.05K 492 75 1968K buffer_head 35213 33124 94% 0.16K 1531 23 6124K dentry_cache 7364 6463 87% 0.27K 526 14 2104K radix_tree_node 2585 1781 68% 0.08K 55 47 220K vm_area_struct 2263 2116 93% 0.12K 73 31 292K size-128 1904 1125 59% 0.03K 16 119 64K size-32 1666 768 46% 0.03K 14 119 56K anon_vma 1512 1482 98% 0.44K 168 9 672K inode_cache 1464 1040 71% 0.06K 24 61 96K size-64 1320 820 62% 0.19K 66 20 264K filp 678 587 86% 0.02K 3 226 12K dm_io 678 587 86% 0.02K 3 226 12K dm_tio 576 574 99% 0.47K 72 8 288K proc_inode_cache 528 514 97% 0.50K 66 8 264K size-512 492 372 75% 0.09K 12 41 48K bio 465 314 67% 0.25K 31 15 124K size-256 452 331 73% 0.02K 2 226 8K biovec-1 420 420 100% 0.19K 21 20 84K skbuff_head_cache 305 256 83% 0.06K 5 61 20K biovec-4 290 4 1% 0.01K 1 290 4K revoke_table 264 264 100% 4.00K 264 1 1056K size-4096 260 256 98% 0.19K 13 20 52K biovec-16 260 256 98% 0.75K 52 5 208K biovec-64
/proc/slabinfo that are included into /usr/bin/slabtop include:
OBJS— The total number of objects (memory blocks), including those in use (allocated), and some spares not in use.ACTIVE— The number of objects (memory blocks) that are in use (allocated).USE— Percentage of total objects that are active. ((ACTIVE/OBJS)(100))OBJ SIZE— The size of the objects.SLABS— The total number of slabs.OBJ/SLAB— The number of objects that fit into a slab.CACHE SIZE— The cache size of the slab.NAME— The name of the slab.
/usr/bin/slabtop program, refer to the slabtop man page.
19.2.25. /proc/stat
/proc/stat, which can be quite long, usually begins like the following example:
cpu 259246 7001 60190 34250993 137517 772 0 cpu0 259246 7001 60190 34250993 137517 772 0 intr 354133732 347209999 2272 0 4 4 0 0 3 1 1249247 0 0 80143 0 422626 5169433 ctxt 12547729 btime 1093631447 processes 130523 procs_running 1 procs_blocked 0 preempt 5651840 cpu 209841 1554 21720 118519346 72939 154 27168 cpu0 42536 798 4841 14790880 14778 124 3117 cpu1 24184 569 3875 14794524 30209 29 3130 cpu2 28616 11 2182 14818198 4020 1 3493 cpu3 35350 6 2942 14811519 3045 0 3659 cpu4 18209 135 2263 14820076 12465 0 3373 cpu5 20795 35 1866 14825701 4508 0 3615 cpu6 21607 0 2201 14827053 2325 0 3334 cpu7 18544 0 1550 14831395 1589 0 3447 intr 15239682 14857833 6 0 6 6 0 5 0 1 0 0 0 29 0 2 0 0 0 0 0 0 0 94982 0 286812 ctxt 4209609 btime 1078711415 processes 21905 procs_running 1 procs_blocked 0
cpu— Measures the number of jiffies (1/100 of a second for x86 systems) that the system has been in user mode, user mode with low priority (nice), system mode, idle task, I/O wait, IRQ (hardirq), and softirq respectively. The IRQ (hardirq) is the direct response to a hardware event. The IRQ takes minimal work for queuing the "heavy" work up for the softirq to execute. The softirq runs at a lower priority than the IRQ and therefore may be interrupted more frequently. The total for all CPUs is given at the top, while each individual CPU is listed below with its own statistics. The following example is a 4-way Intel Pentium Xeon configuration with multi-threading enabled, therefore showing four physical processors and four virtual processors totaling eight processors.page— The number of memory pages the system has written in and out to disk.swap— The number of swap pages the system has brought in and out.intr— The number of interrupts the system has experienced.btime— The boot time, measured in the number of seconds since January 1, 1970, otherwise known as the epoch.
19.2.26. /proc/swaps
/proc/swaps may look similar to the following:
Filename Type Size Used Priority /dev/mapper/VolGroup00-LogVol01 partition 524280 0 -1
/proc/ directory, /proc/swap
provides a snapshot of every swap file name, the type of swap space,
the total size, and the amount of space in use (in kilobytes). The
priority column is useful when multiple swap files are in use. The lower
the priority, the more likely the swap file is to be used.
19.2.27. /proc/sysrq-trigger
echo command to write to this
file, a remote root user can execute most System Request Key commands
remotely as if at the local terminal. To echo values to this file, the /proc/sys/kernel/sysrq must be set to a value other than 0. For more information about the System Request Key, refer to Section 19.3.9.3, “ /proc/sys/kernel/ ”.
19.2.28. /proc/uptime
/proc/uptime is quite minimal:
350735.47 234388.90
19.2.29. /proc/version
gcc
used to compile the kernel, and the time of kernel compilation. It also
contains the kernel compiler's user name (in parentheses).
Linux version 2.6.8-1.523 (user@foo.redhat.com) (gcc version 3.4.1 20040714 \ (Red Hat Enterprise Linux 3.4.1-7)) #1 Mon Aug 16 13:27:03 EDT 2004
19.3. Directories within /proc/
/proc/ directory.
19.3.1. Process Directories
/proc/ directory contains a number of directories with numerical names. A listing of them may be similar to the following:
dr-xr-xr-x 3 root root 0 Feb 13 01:28 1 dr-xr-xr-x 3 root root 0 Feb 13 01:28 1010 dr-xr-xr-x 3 xfs xfs 0 Feb 13 01:28 1087 dr-xr-xr-x 3 daemon daemon 0 Feb 13 01:28 1123 dr-xr-xr-x 3 root root 0 Feb 13 01:28 11307 dr-xr-xr-x 3 apache apache 0 Feb 13 01:28 13660 dr-xr-xr-x 3 rpc rpc 0 Feb 13 01:28 637 dr-xr-xr-x 3 rpcuser rpcuser 0 Feb 13 01:28 666
/proc/ process directory vanishes.
cmdline— Contains the command issued when starting the process.cwd— A symbolic link to the current working directory for the process.environ— A list of the environment variables for the process. The environment variable is given in all upper-case characters, and the value is in lower-case characters.exe— A symbolic link to the executable of this process.fd— A directory containing all of the file descriptors for a particular process. These are given in numbered links:total 0 lrwx------ 1 root root 64 May 8 11:31 0 -> /dev/null lrwx------ 1 root root 64 May 8 11:31 1 -> /dev/null lrwx------ 1 root root 64 May 8 11:31 2 -> /dev/null lrwx------ 1 root root 64 May 8 11:31 3 -> /dev/ptmx lrwx------ 1 root root 64 May 8 11:31 4 -> socket:[7774817] lrwx------ 1 root root 64 May 8 11:31 5 -> /dev/ptmx lrwx------ 1 root root 64 May 8 11:31 6 -> socket:[7774829] lrwx------ 1 root root 64 May 8 11:31 7 -> /dev/ptmx
maps— A list of memory maps to the various executables and library files associated with this process. This file can be rather long, depending upon the complexity of the process, but sample output from thesshdprocess begins like the following:08048000-08086000 r-xp 00000000 03:03 391479 /usr/sbin/sshd 08086000-08088000 rw-p 0003e000 03:03 391479 /usr/sbin/sshd 08088000-08095000 rwxp 00000000 00:00 0 40000000-40013000 r-xp 0000000 03:03 293205 /lib/ld-2.2.5.so 40013000-40014000 rw-p 00013000 03:03 293205 /lib/ld-2.2.5.so 40031000-40038000 r-xp 00000000 03:03 293282 /lib/libpam.so.0.75 40038000-40039000 rw-p 00006000 03:03 293282 /lib/libpam.so.0.75 40039000-4003a000 rw-p 00000000 00:00 0 4003a000-4003c000 r-xp 00000000 03:03 293218 /lib/libdl-2.2.5.so 4003c000-4003d000 rw-p 00001000 03:03 293218 /lib/libdl-2.2.5.so
mem— The memory held by the process. This file cannot be read by the user.root— A link to the root directory of the process.stat— The status of the process.statm— The status of the memory in use by the process. Below is a sample/proc/statmfile:263 210 210 5 0 205 0
The seven columns relate to different memory statistics for the process. From left to right, they report the following aspects of the memory used:- Total program size, in kilobytes.
- Size of memory portions, in kilobytes.
- Number of pages that are shared.
- Number of pages that are code.
- Number of pages of data/stack.
- Number of library pages.
- Number of dirty pages.
status— The status of the process in a more readable form thanstatorstatm. Sample output forsshdlooks similar to the following:Name: sshd State: S (sleeping) Tgid: 797 Pid: 797 PPid: 1 TracerPid: 0 Uid: 0 0 0 0 Gid: 0 0 0 0 FDSize: 32 Groups: VmSize: 3072 kB VmLck: 0 kB VmRSS: 840 kB VmData: 104 kB VmStk: 12 kB VmExe: 300 kB VmLib: 2528 kB SigPnd: 0000000000000000 SigBlk: 0000000000000000 SigIgn: 8000000000001000 SigCgt: 0000000000014005 CapInh: 0000000000000000 CapPrm: 00000000fffffeff CapEff: 00000000fffffeff
The information in this output includes the process name and ID, the state (such asS (sleeping)orR (running)), user/group ID running the process, and detailed data regarding memory usage.
19.3.1.1. /proc/self/
/proc/self/ directory is a link
to the currently running process. This allows a process to look at
itself without having to know its process ID.
/proc/self/ directory produces the same contents as listing the process directory for that process.
19.3.2. /proc/bus/
/proc/bus/ by the same name, such as /proc/bus/pci/.
/proc/bus/
vary depending on the devices connected to the system. However, each
bus type has at least one directory. Within these bus directories are
normally at least one subdirectory with a numerical name, such as 001, which contain binary files.
/proc/bus/usb/
subdirectory contains files that track the various devices on any USB
buses, as well as the drivers required for them. The following is a
sample listing of a /proc/bus/usb/ directory:
total 0 dr-xr-xr-x 1 root root 0 May 3 16:25 001 -r--r--r-- 1 root root 0 May 3 16:25 devices -r--r--r-- 1 root root 0 May 3 16:25 drivers
/proc/bus/usb/001/ directory contains all devices on the first USB bus and the devices file identifies the USB root hub on the motherboard.
/proc/bus/usb/devices file:
T: Bus=01 Lev=00 Prnt=00 Port=00 Cnt=00 Dev#= 1 Spd=12 MxCh= 2 B: Alloc= 0/900 us ( 0%), #Int= 0, #Iso= 0 D: Ver= 1.00 Cls=09(hub ) Sub=00 Prot=00 MxPS= 8 #Cfgs= 1 P: Vendor=0000 ProdID=0000 Rev= 0.00 S: Product=USB UHCI Root Hub S: SerialNumber=d400 C:* #Ifs= 1 Cfg#= 1 Atr=40 MxPwr= 0mA I: If#= 0 Alt= 0 #EPs= 1 Cls=09(hub ) Sub=00 Prot=00 Driver=hub E: Ad=81(I) Atr=03(Int.) MxPS= 8 Ivl=255ms
19.3.3. /proc/bus/pci
/proc/pci directory in favor of the /proc/bus/pci directory. Although you can get a list of all PCI devices present on the system using the command cat /proc/bus/pci/devices, the output is difficult to read and interpret.
~]# /sbin/lspci -vb
00:00.0 Host bridge: Intel Corporation 82X38/X48 Express DRAM Controller
Subsystem: Hewlett-Packard Company Device 1308
Flags: bus master, fast devsel, latency 0
Capabilities: [e0] Vendor Specific Information <?>
Kernel driver in use: x38_edac
Kernel modules: x38_edac
00:01.0 PCI bridge: Intel Corporation 82X38/X48 Express Host-Primary PCI Express Bridge (prog-if 00 [Normal decode])
Flags: bus master, fast devsel, latency 0
Bus: primary=00, secondary=01, subordinate=01, sec-latency=0
I/O behind bridge: 00001000-00001fff
Memory behind bridge: f0000000-f2ffffff
Capabilities: [88] Subsystem: Hewlett-Packard Company Device 1308
Capabilities: [80] Power Management version 3
Capabilities: [90] MSI: Enable+ Count=1/1 Maskable- 64bit-
Capabilities: [a0] Express Root Port (Slot+), MSI 00
Capabilities: [100] Virtual Channel <?>
Capabilities: [140] Root Complex Link <?>
Kernel driver in use: pcieport
Kernel modules: shpchp
00:1a.0 USB Controller: Intel Corporation 82801I (ICH9 Family) USB UHCI Controller #4 (rev 02) (prog-if 00 [UHCI])
Subsystem: Hewlett-Packard Company Device 1308
Flags: bus master, medium devsel, latency 0, IRQ 5
I/O ports at 2100
Capabilities: [50] PCI Advanced Features
Kernel driver in use: uhci_hcd
[output truncated]19.3.4. /proc/driver/
rtc which provides output from the driver for the system's Real Time Clock (RTC), the device that keeps the time while the system is switched off. Sample output from /proc/driver/rtc looks like the following:
rtc_time : 16:21:00 rtc_date : 2004-08-31 rtc_epoch : 1900 alarm : 21:16:27 DST_enable : no BCD : yes 24hr : yes square_wave : no alarm_IRQ : no update_IRQ : no periodic_IRQ : no periodic_freq : 1024 batt_status : okay
/usr/share/doc/kernel-doc-<kernel_version>/Documentation/rtc.txt.
19.3.5. /proc/fs
cat /proc/fs/nfsd/exports
displays the file systems being shared and the permissions granted for
those file systems. For more on file system sharing with NFS, refer to
the Network File System (NFS) chapter of the Storage Administration Guide.
19.3.6. /proc/irq/
/proc/irq/prof_cpu_mask file is a bitmask that contains the default values for the smp_affinity file in the IRQ directory. The values in smp_affinity specify which CPUs handle that particular IRQ.
/proc/irq/ directory, refer to the following installed documentation:
/usr/share/doc/kernel-doc-kernel_version/Documentation/filesystems/proc.txt
19.3.7. /proc/net/
/proc/net/ directory:
arp— Lists the kernel's ARP table. This file is particularly useful for connecting a hardware address to an IP address on a system.atm/directory — The files within this directory contain Asynchronous Transfer Mode (ATM) settings and statistics. This directory is primarily used with ATM networking and ADSL cards.dev— Lists the various network devices configured on the system, complete with transmit and receive statistics. This file displays the number of bytes each interface has sent and received, the number of packets inbound and outbound, the number of errors seen, the number of packets dropped, and more.dev_mcast— Lists Layer2 multicast groups on which each device is listening.igmp— Lists the IP multicast addresses which this system joined.ip_conntrack— Lists tracked network connections for machines that are forwarding IP connections.ip_tables_names— Lists the types ofiptablesin use. This file is only present ifiptablesis active on the system and contains one or more of the following values:filter,mangle, ornat.ip_mr_cache— Lists the multicast routing cache.ip_mr_vif— Lists multicast virtual interfaces.netstat— Contains a broad yet detailed collection of networking statistics, including TCP timeouts, SYN cookies sent and received, and much more.psched— Lists global packet scheduler parameters.raw— Lists raw device statistics.route— Lists the kernel's routing table.rt_cache— Contains the current routing cache.snmp— List of Simple Network Management Protocol (SNMP) data for various networking protocols in use.sockstat— Provides socket statistics.tcp— Contains detailed TCP socket information.tr_rif— Lists the token ring RIF routing table.udp— Contains detailed UDP socket information.unix— Lists UNIX domain sockets currently in use.wireless— Lists wireless interface data.
19.3.8. /proc/scsi/
/proc/scsi/scsi,
which contains a list of every recognized SCSI device. From this
listing, the type of device, as well as the model name, vendor, SCSI
channel and ID data is available.
Attached devices: Host: scsi1 Channel: 00 Id: 05 Lun: 00 Vendor: NEC Model: CD-ROM DRIVE:466 Rev: 1.06 Type: CD-ROM ANSI SCSI revision: 02 Host: scsi1 Channel: 00 Id: 06 Lun: 00 Vendor: ARCHIVE Model: Python 04106-XXX Rev: 7350 Type: Sequential-Access ANSI SCSI revision: 02 Host: scsi2 Channel: 00 Id: 06 Lun: 00 Vendor: DELL Model: 1x6 U2W SCSI BP Rev: 5.35 Type: Processor ANSI SCSI revision: 02 Host: scsi2 Channel: 02 Id: 00 Lun: 00 Vendor: MegaRAID Model: LD0 RAID5 34556R Rev: 1.01 Type: Direct-Access ANSI SCSI revision: 02
/proc/scsi/, which contains files specific to each SCSI controller using that driver. From the previous example, aic7xxx/ and megaraid/
directories are present, since two drivers are in use. The files in
each of the directories typically contain an I/O address range, IRQ
information, and statistics for the SCSI controller using that driver.
Each controller can report a different type and amount of information.
The Adaptec AIC-7880 Ultra SCSI host adapter's file in this example
system produces the following output:
Adaptec AIC7xxx driver version: 5.1.20/3.2.4
Compile Options:
TCQ Enabled By Default : Disabled
AIC7XXX_PROC_STATS : Enabled
AIC7XXX_RESET_DELAY : 5
Adapter Configuration:
SCSI Adapter: Adaptec AIC-7880 Ultra SCSI host adapter
Ultra Narrow Controller PCI MMAPed
I/O Base: 0xfcffe000
Adapter SEEPROM Config: SEEPROM found and used.
Adaptec SCSI BIOS: Enabled
IRQ: 30
SCBs: Active 0, Max Active 1, Allocated 15, HW 16, Page 255
Interrupts: 33726
BIOS Control Word: 0x18a6
Adapter Control Word: 0x1c5f
Extended Translation: Enabled
Disconnect Enable Flags: 0x00ff
Ultra Enable Flags: 0x0020
Tag Queue Enable Flags: 0x0000
Ordered Queue Tag Flags: 0x0000
Default Tag Queue Depth: 8
Tagged Queue By Device array for aic7xxx
host instance 1: {255,255,255,255,255,255,255,255,255,255,255,255,255,255,255,255}
Actual queue depth per device for aic7xxx host instance 1: {1,1,1,1,1,1,1,1,1,1,1,1,1,1,1,1}
Statistics:
(scsi1:0:5:0) Device using Narrow/Sync transfers at 20.0 MByte/sec, offset 15
Transinfo settings: current(12/15/0/0), goal(12/15/0/0), user(12/15/0/0)
Total transfers 0 (0 reads and 0 writes)
< 2K 2K+ 4K+ 8K+ 16K+ 32K+ 64K+ 128K+
Reads: 0 0 0 0 0 0 0 0
Writes: 0 0 0 0 0 0 0 0
(scsi1:0:6:0) Device using Narrow/Sync transfers at 10.0 MByte/sec, offset 15
Transinfo settings: current(25/15/0/0), goal(12/15/0/0), user(12/15/0/0)
Total transfers 132 (0 reads and 132 writes)
< 2K 2K+ 4K+ 8K+ 16K+ 32K+ 64K+ 128K+
Reads: 0 0 0 0 0 0 0 0
Writes: 0 0 0 1 131 0 0 0
19.3.9. /proc/sys/
/proc/sys/ directory is different from others in /proc/
because it not only provides information about the system but also
allows the system administrator to immediately enable and disable kernel
features.
Caution
/proc/sys/ directory. Changing the wrong setting may render the kernel unstable, requiring a system reboot.
/proc/sys/.
-l option at the shell prompt. If the file is writable, it may be used to configure the kernel. For example, a partial listing of /proc/sys/fs looks like the following:
-r--r--r-- 1 root root 0 May 10 16:14 dentry-state -rw-r--r-- 1 root root 0 May 10 16:14 dir-notify-enable -rw-r--r-- 1 root root 0 May 10 16:14 file-max -r--r--r-- 1 root root 0 May 10 16:14 file-nr
dir-notify-enable and file-max
can be written to and, therefore, can be used to configure the kernel.
The other files only provide feedback on current settings.
/proc/sys/
file is done by echoing the new value into the file. For example, to
enable the System Request Key on a running kernel, type the command:
echo 1 > /proc/sys/kernel/sysrq
sysrq from 0 (off) to 1 (on).
/proc/sys/ configuration files
contain more than one value. To correctly send new values to them, place
a space character between each value passed with the echo command, such as is done in this example:
echo 4 2 45 > /proc/sys/kernel/acct
Note
echo
command disappear when the system is restarted. To make configuration
changes take effect after the system is rebooted, refer to Section 19.4, “Using the sysctl Command”.
/proc/sys/ directory contains several subdirectories controlling different aspects of a running kernel.
19.3.9.1. /proc/sys/dev/
cdrom/ and raid/. Customized kernels can have other directories, such as parport/, which provides the ability to share one parallel port between multiple device drivers.
cdrom/ directory contains a file called info, which reveals a number of important CD-ROM parameters:
CD-ROM information, Id: cdrom.c 3.20 2003/12/17 drive name: hdc drive speed: 48 drive # of slots: 1 Can close tray: 1 Can open tray: 1 Can lock tray: 1 Can change speed: 1 Can select disk: 0 Can read multisession: 1 Can read MCN: 1 Reports media changed: 1 Can play audio: 1 Can write CD-R: 0 Can write CD-RW: 0 Can read DVD: 0 Can write DVD-R: 0 Can write DVD-RAM: 0 Can read MRW: 0 Can write MRW: 0 Can write RAM: 0
/proc/sys/dev/cdrom, such as autoclose and checkmedia, can be used to control the system's CD-ROM. Use the echo command to enable or disable these features.
/proc/sys/dev/raid/ directory becomes available with at least two files in it: speed_limit_min and speed_limit_max. These settings determine the acceleration of RAID devices for I/O intensive tasks, such as resyncing the disks.
19.3.9.2. /proc/sys/fs/
binfmt_misc/ directory is used to provide kernel support for miscellaneous binary formats.
/proc/sys/fs/ include:
dentry-state— Provides the status of the directory cache. The file looks similar to the following:57411 52939 45 0 0 0
The first number reveals the total number of directory cache entries, while the second number displays the number of unused entries. The third number tells the number of seconds between when a directory has been freed and when it can be reclaimed, and the fourth measures the pages currently requested by the system. The last two numbers are not used and display only zeros.file-max— Lists the maximum number of file handles that the kernel allocates. Raising the value in this file can resolve errors caused by a lack of available file handles.file-nr— Lists the number of allocated file handles, used file handles, and the maximum number of file handles.overflowgidandoverflowuid— Defines the fixed group ID and user ID, respectively, for use with file systems that only support 16-bit group and user IDs.
19.3.9.3. /proc/sys/kernel/
acct— Controls the suspension of process accounting based on the percentage of free space available on the file system containing the log. By default, the file looks like the following:4 2 30
The first value dictates the percentage of free space required for logging to resume, while the second value sets the threshold percentage of free space when logging is suspended. The third value sets the interval, in seconds, that the kernel polls the file system to see if logging should be suspended or resumed.ctrl-alt-del— Controls whether Ctrl+Alt+Delete gracefully restarts the computer usinginit(0) or forces an immediate reboot without syncing the dirty buffers to disk (1).domainname— Configures the system domain name, such asexample.com.exec-shield— Configures the Exec Shield feature of the kernel. Exec Shield provides protection against certain types of buffer overflow attacks.There are two possible values for this virtual file:0— Disables Exec Shield.1— Enables Exec Shield. This is the default value.
Important
If a system is running security-sensitive applications that were started while Exec Shield was disabled, these applications must be restarted when Exec Shield is enabled in order for Exec Shield to take effect.hostname— Configures the system hostname, such aswww.example.com.hotplug— Configures the utility to be used when a configuration change is detected by the system. This is primarily used with USB and Cardbus PCI. The default value of/sbin/hotplugshould not be changed unless testing a new program to fulfill this role.modprobe— Sets the location of the program used to load kernel modules. The default value is/sbin/modprobewhich meanskmodcalls it to load the module when a kernel thread callskmod.msgmax— Sets the maximum size of any message sent from one process to another and is set to8192bytes by default. Be careful when raising this value, as queued messages between processes are stored in non-swappable kernel memory. Any increase inmsgmaxwould increase RAM requirements for the system.msgmnb— Sets the maximum number of bytes in a single message queue. The default is16384.msgmni— Sets the maximum number of message queue identifiers. The default is4008.osrelease— Lists the Linux kernel release number. This file can only be altered by changing the kernel source and recompiling.ostype— Displays the type of operating system. By default, this file is set toLinux, and this value can only be changed by changing the kernel source and recompiling.overflowgidandoverflowuid— Defines the fixed group ID and user ID, respectively, for use with system calls on architectures that only support 16-bit group and user IDs.panic— Defines the number of seconds the kernel postpones rebooting when the system experiences a kernel panic. By default, the value is set to0, which disables automatic rebooting after a panic.printk— This file controls a variety of settings related to printing or logging error messages. Each error message reported by the kernel has a loglevel associated with it that defines the importance of the message. The loglevel values break down in this order:0— Kernel emergency. The system is unusable.1— Kernel alert. Action must be taken immediately.2— Condition of the kernel is considered critical.3— General kernel error condition.4— General kernel warning condition.5— Kernel notice of a normal but significant condition.6— Kernel informational message.7— Kernel debug-level messages.
Four values are found in theprintkfile:6 4 1 7
Each of these values defines a different rule for dealing with error messages. The first value, called the console loglevel, defines the lowest priority of messages printed to the console. (Note that, the lower the priority, the higher the loglevel number.) The second value sets the default loglevel for messages without an explicit loglevel attached to them. The third value sets the lowest possible loglevel configuration for the console loglevel. The last value sets the default value for the console loglevel.random/directory — Lists a number of values related to generating random numbers for the kernel.sem— Configures semaphore settings within the kernel. A semaphore is a System V IPC object that is used to control utilization of a particular process.shmall— Sets the total amount of shared memory that can be used at one time on the system, in bytes. By default, this value is2097152.shmmax— Sets the largest shared memory segment size allowed by the kernel, in bytes. By default, this value is33554432. However, the kernel supports much larger values than this.shmmni— Sets the maximum number of shared memory segments for the whole system, in bytes. By default, this value is4096sysrq— Activates the System Request Key, if this value is set to anything other than zero (0), the default.The System Request Key allows immediate input to the kernel through simple key combinations. For example, the System Request Key can be used to immediately shut down or restart a system, sync all mounted file systems, or dump important information to the console. To initiate a System Request Key, type Alt+SysRq+system request code. Replacesystem request codewith one of the following system request codes:r— Disables raw mode for the keyboard and sets it to XLATE (a limited keyboard mode which does not recognize modifiers such as Alt, Ctrl, or Shift for all keys).k— Kills all processes active in a virtual console. Also called Secure Access Key (SAK), it is often used to verify that the login prompt is spawned frominitand not a trojan copy designed to capture usernames and passwords.b— Reboots the kernel without first unmounting file systems or syncing disks attached to the system.c— Crashes the system without first unmounting file systems or syncing disks attached to the system.o— Shuts off the system.s— Attempts to sync disks attached to the system.u— Attempts to unmount and remount all file systems as read-only.p— Outputs all flags and registers to the console.t— Outputs a list of processes to the console.m— Outputs memory statistics to the console.0through9— Sets the log level for the console.e— Kills all processes exceptinitusing SIGTERM.i— Kills all processes exceptinitusing SIGKILL.l— Kills all processes using SIGKILL (includinginit). The system is unusable after issuing this System Request Key code.h— Displays help text.
This feature is most beneficial when using a development kernel or when experiencing system freezes.Caution
The System Request Key feature is considered a security risk because an unattended console provides an attacker with access to the system. For this reason, it is turned off by default.Refer to/usr/share/doc/kernel-doc-for more information about the System Request Key.kernel_version/Documentation/sysrq.txttainted— Indicates whether a non-GPL module is loaded.0— No non-GPL modules are loaded.1— At least one module without a GPL license (including modules with no license) is loaded.2— At least one module was force-loaded with the commandinsmod -f.
threads-max— Sets the maximum number of threads to be used by the kernel, with a default value of2048.version— Displays the date and time the kernel was last compiled. The first field in this file, such as#3, relates to the number of times a kernel was built from the source base.
19.3.9.4. /proc/sys/net/
ethernet/, ipv4/, ipx/, and ipv6/.
By altering the files within these directories, system administrators
are able to adjust the network configuration on a running system.
/proc/sys/net/ directories are discussed.
/proc/sys/net/core/ directory
contains a variety of settings that control the interaction between the
kernel and networking layers. The most important of these files are:
message_burst— Sets the amount of time in tenths of a second required to write a new warning message. This setting is used to mitigate Denial of Service (DoS) attacks. The default setting is10.message_cost— Sets a cost on every warning message. The higher the value of this file (default of5), the more likely the warning message is ignored. This setting is used to mitigate DoS attacks.The idea of a DoS attack is to bombard the targeted system with requests that generate errors and fill up disk partitions with log files or require all of the system's resources to handle the error logging. The settings inmessage_burstandmessage_costare designed to be modified based on the system's acceptable risk versus the need for comprehensive logging.netdev_max_backlog— Sets the maximum number of packets allowed to queue when a particular interface receives packets faster than the kernel can process them. The default value for this file is1000.optmem_max— Configures the maximum ancillary buffer size allowed per socket.rmem_default— Sets the receive socket buffer default size in bytes.rmem_max— Sets the receive socket buffer maximum size in bytes.wmem_default— Sets the send socket buffer default size in bytes.wmem_max— Sets the send socket buffer maximum size in bytes.
/proc/sys/net/ipv4/ directory
contains additional networking settings. Many of these settings, used in
conjunction with one another, are useful in preventing attacks on the
system or when using the system to act as a router.
Caution
/proc/sys/net/ipv4/ directory:
icmp_echo_ignore_allandicmp_echo_ignore_broadcasts— Allows the kernel to ignore ICMP ECHO packets from every host or only those originating from broadcast and multicast addresses, respectively. A value of0allows the kernel to respond, while a value of1ignores the packets.ip_default_ttl— Sets the default Time To Live (TTL), which limits the number of hops a packet may make before reaching its destination. Increasing this value can diminish system performance.ip_forward— Permits interfaces on the system to forward packets to one other. By default, this file is set to0. Setting this file to1enables network packet forwarding.ip_local_port_range— Specifies the range of ports to be used by TCP or UDP when a local port is needed. The first number is the lowest port to be used and the second number specifies the highest port. Any systems that expect to require more ports than the default 1024 to 4999 should use a range from 32768 to 61000.tcp_syn_retries— Provides a limit on the number of times the system re-transmits a SYN packet when attempting to make a connection.tcp_retries1— Sets the number of permitted re-transmissions attempting to answer an incoming connection. Default of3.tcp_retries2— Sets the number of permitted re-transmissions of TCP packets. Default of15.
/usr/share/doc/kernel-doc-kernel_version/Documentation/networking/ip-sysctl.txt/proc/sys/net/ipv4/ directory.
/proc/sys/net/ipv4/ directory and each covers a different aspect of the network stack. The /proc/sys/net/ipv4/conf/
directory allows each system interface to be configured in different
ways, including the use of default settings for unconfigured devices (in
the /proc/sys/net/ipv4/conf/default/ subdirectory) and settings that override all special configurations (in the /proc/sys/net/ipv4/conf/all/ subdirectory).
/proc/sys/net/ipv4/neigh/
directory contains settings for communicating with a host directly
connected to the system (called a network neighbor) and also contains
different settings for systems more than one hop away.
/proc/sys/net/ipv4/route/. Unlike conf/ and neigh/, the /proc/sys/net/ipv4/route/ directory contains specifications that apply to routing with any interfaces on the system. Many of these settings, such as max_size, max_delay, and min_delay, relate to controlling the size of the routing cache. To clear the routing cache, write any value to the flush file.
/usr/share/doc/kernel-doc-kernel_version/Documentation/filesystems/proc.txt
19.3.9.5. /proc/sys/vm/
/proc/sys/vm/ directory:
block_dump— Configures block I/O debugging when enabled. All read/write and block dirtying operations done to files are logged accordingly. This can be useful if diagnosing disk spin up and spin downs for laptop battery conservation. All output whenblock_dumpis enabled can be retrieved viadmesg. The default value is0.Tip
Ifblock_dumpis enabled at the same time as kernel debugging, it is prudent to stop theklogddaemon, as it generates erroneous disk activity caused byblock_dump.dirty_background_ratio— Starts background writeback of dirty data at this percentage of total memory, via a pdflush daemon. The default value is10.dirty_expire_centisecs— Defines when dirty in-memory data is old enough to be eligible for writeout. Data which has been dirty in-memory for longer than this interval is written out next time a pdflush daemon wakes up. The default value is3000, expressed in hundredths of a second.dirty_ratio— Starts active writeback of dirty data at this percentage of total memory for the generator of dirty data, via pdflush. The default value is20.dirty_writeback_centisecs— Defines the interval between pdflush daemon wakeups, which periodically writes dirty in-memory data out to disk. The default value is500, expressed in hundredths of a second.laptop_mode— Minimizes the number of times that a hard disk needs to spin up by keeping the disk spun down for as long as possible, therefore conserving battery power on laptops. This increases efficiency by combining all future I/O processes together, reducing the frequency of spin ups. The default value is0, but is automatically enabled in case a battery on a laptop is used.This value is controlled automatically by the acpid daemon once a user is notified battery power is enabled. No user modifications or interactions are necessary if the laptop supports the ACPI (Advanced Configuration and Power Interface) specification.For more information, refer to the following installed documentation:/usr/share/doc/kernel-doc-kernel_version/Documentation/laptop-mode.txtmax_map_count— Configures the maximum number of memory map areas a process may have. In most cases, the default value of65536is appropriate.min_free_kbytes— Forces the Linux VM (virtual memory manager) to keep a minimum number of kilobytes free. The VM uses this number to compute apages_minvalue for eachlowmemzone in the system. The default value is in respect to the total memory on the machine.nr_hugepages— Indicates the current number of configuredhugetlbpages in the kernel.For more information, refer to the following installed documentation:/usr/share/doc/kernel-doc-kernel_version/Documentation/vm/hugetlbpage.txtnr_pdflush_threads— Indicates the number of pdflush daemons that are currently running. This file is read-only, and should not be changed by the user. Under heavy I/O loads, the default value of two is increased by the kernel.overcommit_memory— Configures the conditions under which a large memory request is accepted or denied. The following three modes are available:0— The kernel performs heuristic memory over commit handling by estimating the amount of memory available and failing requests that are blatantly invalid. Unfortunately, since memory is allocated using a heuristic rather than a precise algorithm, this setting can sometimes allow available memory on the system to be overloaded. This is the default setting.1— The kernel performs no memory over commit handling. Under this setting, the potential for memory overload is increased, but so is performance for memory intensive tasks (such as those executed by some scientific software).2— The kernel fails requests for memory that add up to all of swap plus the percent of physical RAM specified in/proc/sys/vm/overcommit_ratio. This setting is best for those who desire less risk of memory overcommitment.Note
This setting is only recommended for systems with swap areas larger than physical memory.
overcommit_ratio— Specifies the percentage of physical RAM considered when/proc/sys/vm/overcommit_memoryis set to2. The default value is50.page-cluster— Sets the number of pages read in a single attempt. The default value of3, which actually relates to 16 pages, is appropriate for most systems.swappiness— Determines how much a machine should swap. The higher the value, the more swapping occurs. The default value, as a percentage, is set to60.
/usr/share/doc/kernel-doc-kernel_version/Documentation/, which contains additional information.
19.3.10. /proc/sysvipc/
msg), semaphores (sem), and shared memory (shm).
19.3.11. /proc/tty/
drivers file is a list of the current tty devices in use, as in the following example:
serial /dev/cua 5 64-127 serial:callout serial /dev/ttyS 4 64-127 serial pty_slave /dev/pts 136 0-255 pty:slave pty_master /dev/ptm 128 0-255 pty:master pty_slave /dev/ttyp 3 0-255 pty:slave pty_master /dev/pty 2 0-255 pty:master /dev/vc/0 /dev/vc/0 4 0 system:vtmaster /dev/ptmx /dev/ptmx 5 2 system /dev/console /dev/console 5 1 system:console /dev/tty /dev/tty 5 0 system:/dev/tty unknown /dev/vc/%d 4 1-63 console
/proc/tty/driver/serial file lists the usage statistics and status of each of the serial tty lines.
19.3.12. /proc/PID/
PID//proc/sys/vm/panic_on_oom. When set to 1 the kernel will panic on OOM. A setting of 0 instructs the kernel to call a function named oom_killer on an OOM. Usually, oom_killer can kill rogue processes and the system will survive.
/proc/sys/vm/panic_on_oom.
# cat /proc/sys/vm/panic_on_oom 1 # echo 0 > /proc/sys/vm/panic_on_oom # cat /proc/sys/vm/panic_on_oom 0
oom_killer score. In /proc/PID/ there are two tools labelled oom_adj and oom_score. Valid scores for oom_adj are in the range -16 to +15. To see the current oom_killer score, view the oom_score for the process. oom_killer will kill processes with the highest scores first.
PID of 12465 to make it less likely that oom_killer will kill it.
# cat /proc/12465/oom_score 79872 # echo -5 > /proc/12465/oom_adj # cat /proc/12465/oom_score 78
oom_killer for that process. In the example below, oom_score returns a value of 0, indicating that this process would not be killed.
# cat /proc/12465/oom_score 78 # echo -17 > /proc/12465/oom_adj # cat /proc/12465/oom_score 0
badness() is used to
determine the actual score for each process. This is done by adding up
'points' for each examined process. The process scoring is done in the
following way:
- The basis of each process's score is its memory size.
- The memory size of any of the process's children (not including a kernel thread) is also added to the score
- The process's score is increased for 'niced' processes and decreased for long running processes.
- Processes with the
CAP_SYS_ADMINandCAP_SYS_RAWIOcapabilities have their scores reduced. - The final score is then bitshifted by the value saved in the
oom_adjfile.
oom_score
value will most probably be a non-priviliged, recently started process
that, along with its children, uses a large amount of memory, has been
'niced', and handles no raw I/O.
19.4. Using the sysctl Command
/sbin/sysctl command is used to view, set, and automate kernel settings in the /proc/sys/ directory.
/proc/sys/ directory, type the /sbin/sysctl -a command as root. This creates a large, comprehensive list, a small portion of which looks something like the following:
net.ipv4.route.min_delay = 2 kernel.sysrq = 0 kernel.sem = 250 32000 32 128
/proc/sys/net/ipv4/route/min_delay file is listed as net.ipv4.route.min_delay, with the directory slashes replaced by dots and the proc.sys portion assumed.
sysctl command can be used in place of echo to assign values to writable files in the /proc/sys/ directory. For example, instead of using the command
echo 1 > /proc/sys/kernel/sysrq
sysctl command as follows:
sysctl -w kernel.sysrq="1" kernel.sysrq = 1
/proc/sys/ is helpful during testing, this method does not work as well on a production system as special settings within /proc/sys/ are lost when the machine is rebooted. To preserve custom settings, add them to the /etc/sysctl.conf file.
init program runs the /etc/rc.d/rc.sysinit script. This script contains a command to execute sysctl using /etc/sysctl.conf to determine the values passed to the kernel. Any values added to /etc/sysctl.conf therefore take effect each time the system boots.
19.5. References
proc file system.
Installed Documentation
proc file system is installed on the system by default.
/usr/share/doc/kernel-doc-— Contains assorted, but limited, information about all aspects of thekernel_version/Documentation/filesystems/proc.txt/proc/directory./usr/share/doc/kernel-doc-— An overview of System Request Key options.kernel_version/Documentation/sysrq.txt/usr/share/doc/kernel-doc-— A directory containing a variety ofkernel_version/Documentation/sysctl/sysctltips, including modifying values that concern the kernel (kernel.txt), accessing file systems (fs.txt), and virtual memory use (vm.txt)./usr/share/doc/kernel-doc-— A detailed overview of IP networking options.kernel_version/Documentation/networking/ip-sysctl.txt
Useful Websites
- http://www.linuxhq.com/ — This website maintains a complete database of source, patches, and documentation for various versions of the Linux kernel.
Part IV. System Monitoring
Chapter 20. Gathering System Information
20.1. System Processes
ps ax command displays a list of
current system processes, including processes owned by other users. To
display the owner alongside each process, use the ps aux
command. This list is a static list; in other words, it is a snapshot
of what was running when you invoked the command. If you want a
constantly updated list of running processes, use top as described below.
ps output can be long. To prevent it from scrolling off the screen, you can pipe it through less:
ps aux | lessps command in combination with the grep command to see if a process is running. For example, to determine if Emacs is running, use the following command:
ps ax | grep emacstop command displays currently
running processes and important information about them including their
memory and CPU usage. The list is both real-time and interactive. An
example of output from the top command is provided as follows:
top - 18:11:48 up 1 min, 1 user, load average: 0.68, 0.30, 0.11
Tasks: 122 total, 1 running, 121 sleeping, 0 stopped, 0 zombie
Cpu(s): 0.0%us, 0.5%sy, 0.0%ni, 93.4%id, 5.7%wa, 0.2%hi, 0.2%si, 0.0
Mem: 501924k total, 376496k used, 125428k free, 29664k buffers
Swap: 1015800k total, 0k used, 1015800k free, 189008k cached
PID USER PR NI VIRT RES SHR S %CPU %MEM TIME+ COMMAND
1601 root 40 0 20172 1084 920 S 0.3 0.2 0:00.08 hald-addon-sto
1998 silas 40 0 14984 1160 880 R 0.3 0.2 0:00.13 top
1 root 40 0 19160 1412 1156 S 0.0 0.3 0:00.96 init
2 root 40 0 0 0 0 S 0.0 0.0 0:00.01 kthreadd
3 root RT 0 0 0 0 S 0.0 0.0 0:00.05 migration/0
4 root 20 0 0 0 0 S 0.0 0.0 0:00.00 ksoftirqd/0
5 root RT 0 0 0 0 S 0.0 0.0 0:00.00 watchdog/0
6 root RT 0 0 0 0 S 0.0 0.0 0:00.04 migration/1
7 root 20 0 0 0 0 S 0.0 0.0 0:00.00 ksoftirqd/1
8 root RT 0 0 0 0 S 0.0 0.0 0:00.00 watchdog/1
9 root 20 0 0 0 0 S 0.0 0.0 0:00.00 events/0
10 root 20 0 0 0 0 S 0.0 0.0 0:00.01 events/1
11 root 20 0 0 0 0 S 0.0 0.0 0:00.00 cpuset
12 root 20 0 0 0 0 S 0.0 0.0 0:00.00 khelper
[output truncated]top, press the q key.
top commands” contains useful interactive commands that you can use with top. For more information, refer to the top(1) manual page.
Table 20.1. Interactive top commands
| Command | Description |
|---|---|
| Space | Immediately refresh the display |
| h | Display a help screen |
| k | Kill a process. You are prompted for the process ID and the signal to send to it. |
| n | Change the number of processes displayed. You are prompted to enter the number. |
| u | Sort by user. |
| M | Sort by memory usage. |
| P | Sort by CPU usage. |
top, you can use the GNOME System Monitor. To start it from the desktop, select → → or execute gnome-system-monitor at a shell prompt. Select the Processes tab.
- Stop a process.
- Continue or start a process.
- End a processes.
- Kill a process.
- Change the priority of a selected process.
- Edit the System Monitor preferences. These include changing the interval seconds to refresh the list and selecting process fields to display in the System Monitor window.
- View only active processes.
- View all processes.
- View my processes.
- View process dependencies.
- View a memory map of a selected process.
- View the files opened by the selected process.
- Refresh the list of processes.
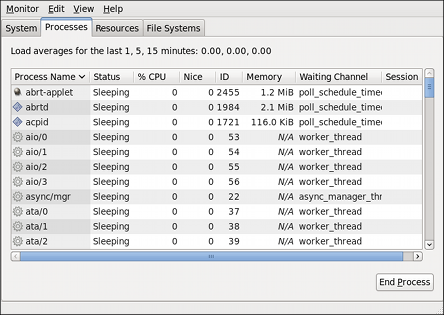
Figure 20.1. GNOME System Monitor - Processes tab
20.2. Memory Usage
free command displays the total
amount of physical memory and swap space for the system as well as the
amount of memory that is used, free, shared, in kernel buffers, and
cached.
total used free shared buffers cached Mem: 4017660 1619044 2398616 0 59864 637968 -/+ buffers/cache: 921212 3096448 Swap: 3071996 0 3071996
free -m shows the same information in megabytes, which are easier to read.
total used free shared buffers cached Mem: 3923 1569 2353 0 58 626 -/+ buffers/cache: 884 3038 Swap: 2999 0 2999
free, you can use the GNOME System Monitor. To start it from the desktop, select → → or execute gnome-system-monitor at a shell prompt. Click on the Resources tab.
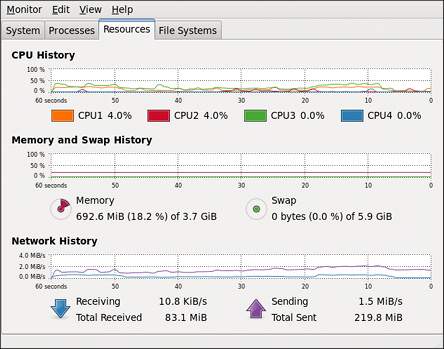
Figure 20.2. GNOME System Monitor - Resources tab
20.3. File Systems
df command reports the system's disk space usage. If you Execute the command df at a shell prompt, the output looks similar to the following:
Filesystem 1K-blocks Used Available Use% Mounted on
/dev/mapper/volgrp1-lvroot
14127024 6868092 6541316 52% /
tmpfs 2008828 592 2008236 1% /dev/shm
/dev/sda1 495844 65047 405197 14% /boot
/dev/mapper/luks-b20f8f7a-7f0f-4497-8de4-81bfa3e541cf
122046576 12111420 103735552 11% /home
df -h. The -h argument stands for human-readable format. The output looks similar to the following:
Filesystem Size Used Avail Use% Mounted on
/dev/mapper/volgrp1-lvroot
14G 6.6G 6.3G 52% /
tmpfs 2.0G 592K 2.0G 1% /dev/shm
/dev/sda1 485M 64M 396M 14% /boot
/dev/mapper/luks-b20f8f7a-7f0f-4497-8de4-81bfa3e541cf
117G 12G 99G 11% /home
/dev/shm. This entry represents the system's virtual memory file system.
du command displays the estimated amount of space being used by files in a directory. If you execute du
at a shell prompt, the disk usage for each of the subdirectories is
displayed in a list. The grand total for the current directory and
subdirectories are also shown as the last line in the list. If you do
not want to see the totals for all the subdirectories, use the command du -hs to see only the grand total for the directory in human-readable format. Use the du --help command to see more options.
gnome-system-monitor
command at a shell prompt. Select the File Systems tab to view the
system's partitions. The figure below illustrates the File Systems tab.
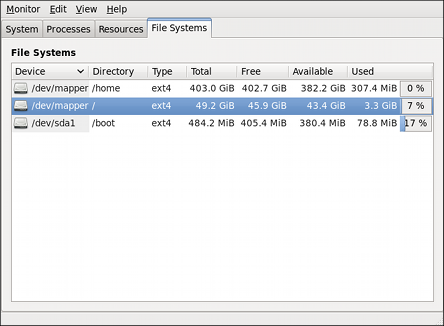
Figure 20.3. GNOME System Monitor - File Systems tab
20.4. Hardware
hwbrowser at a shell prompt. As shown in Figure 20.4, “ Hardware Browser ”,
it displays your CD-ROM devices, diskette drives, hard drives and their
partitions, network devices, pointing devices, system devices, and
video cards. Click on the category name in the left menu, and the
information is displayed.
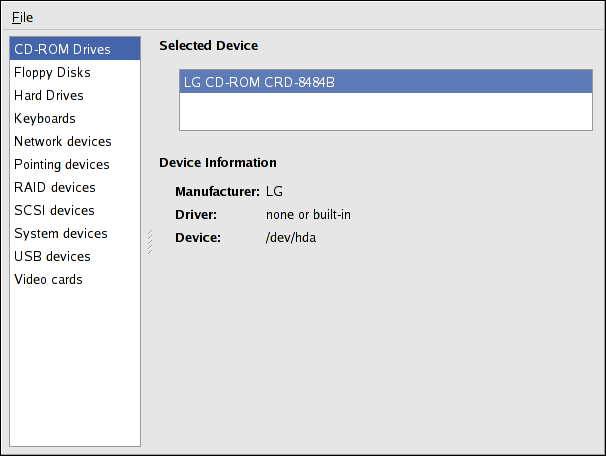
Figure 20.4. Hardware Browser
hal-device-manager. Depending on your installation preferences, the graphical menu above may start this application or the Hardware Browser when clicked. The figure below illustrates the Device Manager window.
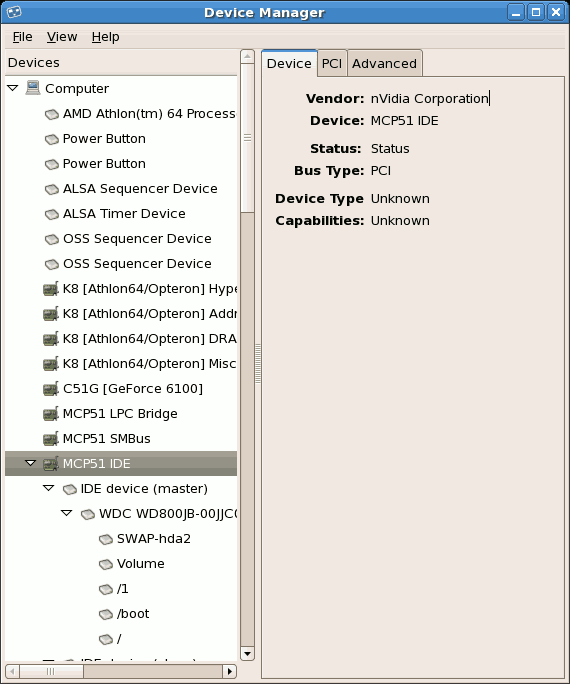
Figure 20.5. Device Manager
lspci command to list all PCI devices. Use the command lspci -v for more verbose information or lspci -vv for very verbose output.
lspci can be used to determine the manufacturer, model, and memory size of a system's video card:
00:02.1 Display controller: Intel Corporation Mobile 4 Series Chipset Integrated Graphics Controller (rev 07)
Subsystem: Lenovo Device 20e4
Flags: bus master, fast devsel, latency 0
Memory at f4200000 (64-bit, non-prefetchable) [size=1M]
Capabilities: [d0] Power Management version 3lspci is also useful to determine the network card in your system if you do not know the manufacturer or model number.
20.5. Additional Resources
20.5.1. Installed Documentation
ps --help— Displays a list of options that can be used withps.topmanual page — Executeman topto learn more abouttopand its many options.freemanual page — Executeman freeto learn more aboutfreeand its many options.dfmanual page — Executeman dfto learn more about thedfcommand and its many options.dumanual page — Executeman duto learn more about theducommand and its many options.lspcimanual page — Executeman lspcito learn more about thelspcicommand and its many options.
Chapter 21. ABRT
21.1. Overview
abrtd, the system service- abrt-applet, which runs in the user's Notification Area
- abrt-gui, the GUI application that shows collected crash dumps and allows you to edit, report, and delete them
- abrt-cli, the command line interface with functionality similar to abrt-gui.
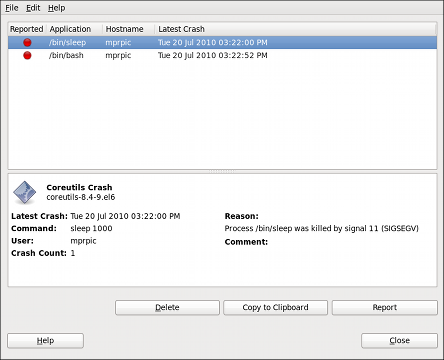
~]$ yum list all | grep abrt21.2. Installing and Running ABRT
abrtd daemon configured to run at boot time, and abrt-applet to run in the Notification Area of your desktop session.
Note: Installing the ABRT packages
abrt-desktop package is installed on your system by running, as root:
~]# yum install abrt-desktopabrtd daemon is running by running the following command, as root:
~]# service abrtd status
abrt (pid 1559) is running...abrt is stopped, you can start the abrtd service by running, as root:
~]# service abrtd start
Starting abrt daemon: [ OK ]abrtd service initializes at startup time by running the following command, as root:
~]# chkconfig abrtd onabrt-applet
program as a normal user when logged into your desktop session, or by
arranging for it to be started when the GUI session is initialized. For
example, on the GNOME desktop, this can be configured in → → .
D-Bus message is sent about this crash. If abrt-applet
is running, it receives this message and displays a red alarm icon in
the Notification Area. You can open the GUI application by clicking on
this icon.
21.3. ABRT Plugins
]$ yum list all | grep abrt-plugin-*21.3.1. Analyzer Plugins
/etc/abrt/plugins/ directory. The following is a list of all analyzer plugins.
- Kerneloops
- — Checks for crashes in the kernel and consequently collects kernel crash information. It can be enabled/disabled from loading at start-up in the
/etc/abrt/plugins/Kerneloops.conffile. - Python
- — Checks for crashes in Python programs and consequently collects the crash information. It can be enabled/disabled from loading at start-up in the
/etc/abrt/plugins/Python.conffile. - CCpp
- — Checks for crashes in C and C++ programs and consequently collects the crash information. It can be enabled/disabled from loading at start-up in the
/etc/abrt/plugins/CCpp.conffile.
21.3.2. Reporter Plugins
/etc/abrt/plugins/ directory or in the ABRT GUI application (for more information on reporter plugin configuration in the ABRT GUI application, refer to Section 21.3.3, “Plugin Configuration in the GUI”).
- RHTSupport
- — Reports crashes into the Red Hat Technical Support system. Intended for users of Red Hat Enterprise Linux.
- MailX
- — Sends a crash report via the mailx utility to a specified email address.
- Report Uploader
- — Uploads a tarball with crash data into a
FTP/SCPserver - Bugzilla
- — Reports crashes into Bugzilla in the form of Bugzilla database entries.
Note
The use of the Bugzilla plugin to report crashes into Bugzilla in the form of Bugzilla database entries is strongly discouraged. Please use the RHTSupport plugin to report crashes into the Red Hat Ticketing System instead. - Logger
- — Creates a crash report and saves it to a specified local file.
21.3.3. Plugin Configuration in the GUI
/etc/abrt/plugins/*.conf configuration files on a per-user basis. Each of the plugins specified in section Section 21.3.2, “Reporter Plugins” can be configured in the ABRT GUI application. Open the plugins window by clicking → .
This window shows a list of all installed plugins. You can also view
each of the plugins' details by selecting one and expanding . When you select one of the configurable plugins, you can click the
button and you will be able to configure your desired plugin. If you
change any of the plugins' parameters, they are saved in the Gnome
keyring and will be used in the future GUI sessions.
Note
/etc/abrt/plugins/*.conf
configuration files are world readable and are meant to be used as
global settings. Thus, it is not advisable to store usernames, passwords
or any other sensitive data in them. The per-user settings (set in the
GUI application and readable by the owner of $HOME only) are stored in
the Gnome keyring or can be stored in a text file in $HOME/.abrt/*.conf for use in abrt-cli.

- RHTSupport
- In the RHTSupport plugin configuration, you can configure the following parameters:
- RHTSupport URL — Specifies the RHTSupport URL where crash dumps are sent (by default, set to https://api.access.redhat.com/rs).
- Login — User login which is used to log into RHTSupport and create a RHTSupport database entry for a reported crash.
- Password — Password used to log into RHTSupport.
When the SSL verify option is checked, theSSLprotocol is used when sending the data over the network. - MailX
- In the MailX plugin configuration, you can configure the following parameters:
- Subject — A string that appears in the
Subjectfield of a crash report email sent by mailx (by default, set to"[abrt] crash report"). - Your Email — A string that appears in the
Fromfield of a crash report email. - Recipient's Email — Email address of the recipient of a crash report email.
When the Send Binary Data option is checked, the crash report email will also contain all binary files associated with the crash in an attachment. The core dump file is also sent as an attachment. - ReportUploader
- In the ReportUploader plugin configuration, you can configure the following parameters:
- Customer — Specifies customer's identification.
- Ticket — Specifies the Ticket ID number in a specific issue tracker that collects crash reports.
- URL — Specifies the URL of the issue tracker used to collect crash reports.
- Retry count — Specifies the number of retries should an upload fail.
- Retry delay — Specifies the number or seconds between two retries.
When the Use encryption option is checked, the crash report sent to the issue tracker is encrypted.When the Upload option is checked, all crash reports are uploaded to the specified issue tracker. If the option is unchecked, all crash reports are saved locally. - Bugzilla
- In the Bugzilla plugin configuration, you can configure the following parameters:
- Bugzilla URL — Specifies the Bugzilla URL where crash dumps are sent (by default, set to https://bugzilla.redhat.com).
- Login (email) — User login which is used to log into Bugzilla and create a Bugzilla database entry for a reported crash.
- Password — Password used to log into Bugzilla.
When the SSL verify option is checked, theSSLprotocol is used when sending the data over the network. - Logger
- In the Logger plugin configuration, you can configure the following parameter:
- Logger file — Specifies a file into which the crash reports are saved (by default, set to
/var/log/abrt.log).
When the Append new logs option is checked, the Logger plugin will append new crash reports to the log file specified in the Logger file option. When unchecked, the new crash report always replaces the previous one.
21.4. Generating Backtraces
CCpp analyzer plugin) occurs.
- It examines the core dump (which consists of the recorded contents of the memory of an application at a specific time), which is saved in the crash dump directory. From this file, ABRT extracts the information about the crashed binary program and information about every loaded dynamic library.
- It queries Yum to determine which debuginfo packages correspond to all the files extracted from the crash dump. This is the first potentially slow operation. Yum may need to refresh the
filelistsof various repositories in order to find the correct package names. This process may take a few minutes. - It downloads the needed debuginfo packages, and extracts and saves the
debuginfofiles. In order to speed up future backtrace generation,debuginfofiles are cached in the/var/cache/abrt-didirectory. - It generates a backtrace using GDB (the GNU Debugger) and saves it into the crash dump directory.
/etc/abrt/plugins/CCpp.conf file:
Backtrace =— Enables/Disables backtrace generation.<yes/no>BacktraceRemotes =— For more information about this parameter, refer to Section 21.7, “Configuring Centralized Crash Collection”.<yes/no>InstallDebugInfo =— Enables/Disables the installation of debuginfo packages (useful if your network is not available or it is firewalled).<yes/no>ReadonlyLocalDebugInfoDirs = /path1:/path2:...— Specifies the paths of local repositories (available, for example, through a network mount) that contain pre-downloaded debuginfo packages.DebugInfoCacheMB =— Specifies the maximum size of the cached debuginfo packages in the4000/var/cache/abrt-didirectory.
21.4.1. Troubleshooting Backtrace Generation
Starting the debuginfo installation Getting list of build IDs 12 missing debuginfos, getting package list from cache 12 missing debuginfos, getting package list from repositories Downloading 7 packages Download 1/7: acl-debuginfo-2.2.49-6.fc13.x86_64 Unpacking: acl-debuginfo-2.2.49-6.fc13.x86_64.rpm Caching debuginfo: usr/lib/debug/.build-id/3d/e20df1db609bd9313b1dc440796004f95911fd.debug Download 2/7: firefox-debuginfo-3.6.7-1.fc13.x86_64 Unpacking: firefox-debuginfo-3.6.7-1.fc13.x86_64.rpm Caching debuginfo: usr/lib/debug/.build-id/3d/b29c9308cb276431ce8854a2d88cf83518afc6.debug Caching debuginfo: usr/lib/debug/.build-id/a3/86884285365c8288e4e761ec034fafaa1daee1.debug ⋮ Download 7/7: zlib-debuginfo-1.2.3-23.fc12.x86_64 Unpacking: zlib-debuginfo-1.2.3-23.fc12.x86_64.rpm Caching debuginfo: usr/lib/debug/.build-id/f7/933750da80f555321576e72b375caf7a3cc075.debug All needed debuginfos are present Generating backtrace
/var/run/abrt/tmp-29177-1283344373) for its operations. Normally, this directory is removed when abrt-debuginfo-install exits.
debug=false keep_tmp=false
debug=true keep_tmp=true
/var/run/abrt/tmp-NNN-NNN directory. You can examine the log files in this directory, they may contain useful error messages.
/tmp directory and run the following commands, as root:
tmp]# yum --enablerepo=*debuginfo* --quiet provides /usr/bin/true tmp]# yumdownloader --enablerepo=*debuginfo* --quiet coreutils
coreutils-*.rpm file. If any error messages appear, check your yum configuration files in the /etc/yum.repos.d/* directory and the /etc/yum/* directory. If any of these commands hang, check that you do not have another instance of yum running, and that your network connection is working properly.
21.5. Using the Command Line Interface
21.5.1. Viewing Crashes
abrt-cli --list or abrt-cli -l:
~]$ abrt-cli --list
0.
UID : 500
UUID : 784b06666020e9f43718d99bf2649f19b4f251a9
Package : bash-4.1.2-3.el6
Executable : /bin/bash
Crash Time : Tue 20 Jul 2010 03:22:52 PM CEST
Crash Count: 2
1.
UID : 500
UUID : 48007b98d65cca4530d99a564379e2609169239d
Package : coreutils-8.4-9.el6
Executable : /bin/sleep
Crash Time : Tue 20 Jul 2010 03:22:00 PM CEST
Crash Count: 1
UID: field shows the ID of the user which ran the program that caused the crash. The Package field shows the name and version of the Red Hat Enterprise Linux package that contains the program, and the Executable field shows the location of the binary or script that crashed. The Crash Count field indicates how many times the same crash happened.
21.5.2. Reporting Crashes
abrt-cli --report <UUID> or abrt-cli --r <UUID>, where UUID is a Universally Unique Identifier of a crash from the list of crashes; to view this list, execute the abrt-cli --list command. You do not need to remember the exact UUID; either use a mouse to copy and paste it, or enter a unique prefix and press <ENTER>.
~]$ abrt-cli --report 480
<ENTER>
>> Starting report creation...
abrt-cli
opens a text editor with the content of the report. You can see what is
being reported, and you can fill in instructions on how to reproduce
the crash and other comments. You should also check the backtrace,
because the backtrace might be sent to a public server and viewed by
anyone, depending on the plugin settings.
Preferred Text Editor
abrt-cli uses the editor defined in the ABRT_EDITOR environment variable. If the variable is not defined, it checks the VISUAL and EDITOR variables. If none of these variables is set, vi is used. You can set the preferred editor in your .bashrc configuration file. For example, if you prefer GNU Emacs, add the following line to the file:
exportVISUAL=emacs
21.5.3. Deleting Crashes
abrt-cli --delete <UUID> .
21.6. Configuring ABRT
/etc/abrt/abrt.conf. ABRT plugins can be configured through their config files, located in the /etc/abrt/plugins/ directory.
abrt.conf configuration file, you must restart the abrtd daemon—as root—for the new settings to take effect:
~]# service abrtd restart/etc/abrt/abrt.conf.
[ Common ] Section Directives
- OpenGPGCheck =
<yes/no> - Setting the
OpenGPGCheckdirective toyes(the default setting) tells ABRT to only analyze and handle crashes in applications provided by packages which are signed by the GPG keys whose locations are listed in the/etc/abrt/gpg_keysfile. SettingOpenGPGChecktonotells ABRT to catch crashes in all programs. - BlackList = nspluginwrapper, valgrind, strace, avant-window-navigator, [
<additional_packages>] - Crashes in packages and binaries listed after the
BlackListdirective will not be handled by ABRT. If you want ABRT to ignore other packages and binaries, list them here separated by commas. - ProcessUnpackaged =
<yes/no> - This directive tells ABRT whether to process crashes in executables that do not belong to any package.
- BlackListedPaths =
/usr/share/doc/*,*/example* - Crashes in executables in these paths will be ignored by ABRT.
- Database = SQLite3
- This directive instructs ABRT to store its crash data in the SQLite3 database. Other databases are not currently supported. However, ABRT's plugin architecture allows for future support for alternative databases.
- #WatchCrashdumpArchiveDir = /var/spool/abrt-upload/
- This directive is commented out by default. Enable (uncomment) it if you want
abrtdto auto-unpack crashdump tarballs which appear in the specified directory — in this case/var/spool/abrt-upload/— (for example, uploaded viaftp,scp, etc.). You must ensure that whatever directory you specify in this directive exists and is writable forabrtd.abrtdwill not create it automatically. - MaxCrashReportsSize =
<size_in_megabytes> - This option sets the amount of storage space, in megabytes, used by ABRT to store all crash information from all users. The default setting is
1000MB. Once the quota specified here has been met, ABRT will continue catching crashes, and in order to make room for the new crash dumps, it will delete the oldest and largest ones. - ActionsAndReporters = SOSreport, [
<additional_plugins>] - This option tells ABRT to run the specified plugin(s) immediately after a crash is detected and saved. For example, the
SOSreportplugin runs thesosreporttool which adds the data collected by it to the created crash dump. You can turn this behavior off by commenting out this line. For further fine-tuning, you can addSOSreport(or any other specified plugin) to either theCCpporPythonoptions to make ABRT runsosreport(or any other specified plugin) after any C and C++ or Python applications crash, respectively. For more information on various Action and Reporter plugins, refer to Section 21.3, “ ABRT Plugins”
[ AnalyzerActionsAndReporters ] Section Directives
abrt-gui or abrt-cli
and report the crash that occurred. If you do not specify any actions
and reporters in these directives, you will not be able to report a
crash via abrt-gui or abrt-cli. The order of actions and reporters is important. Commenting out a directive, will cause ABRT not to catch the crashes associated with that directive. For example, commenting out the Kerneloops line will cause ABRT not to catch kernel oopses.
- Kerneloops = RHTSupport, Logger
- This directive specifies that, for kernel oopses, both the RHTSupport and Logger reporters will be run.
- CCpp = RHTSupport, Logger
- This directive specifies that, when C or C++ program crashes occur, both the RHTSupport and Logger reporters will be run.
- Python = RHTSupport, Logger
- This directive specifies that, when Python program crashes occur, both the RHTSupport and Logger reporters will be run.
plugins/*.conf file. For example, plugins/RHTSupport.conf specifies which RHTSupport URL to use (set to https://api.access.redhat.com/rs
by default), the user's login name, password for logging in to the
RHTSupport site, etc. All these options can also be configured through
the abrt-gui application (for more information on plugin configuration refer to Section 21.3, “ ABRT Plugins”).
[ Cron ] Section Directives
-
<time>=<action_to_run> - The
[ Cron ]section ofabrt.confallows you to specify the exact time, or elapsed amount of time between, when ABRT should run a certain action, such as scanning for kernel oopses or performing file transfers. You can list further actions to run by appending them to the end of this section.Example 21.1. [ Cron ] section of /etc/abrt/abrt.conf
# Which Action plugins to run repeatedly [ Cron ] # h:m - at h:m # s - every s seconds 120 = KerneloopsScanner #02:00 = FileTransfer
The format for an entry is either<time_in_seconds> =or<action_to_run><hh:mm> = <action_to_run>, wherehh(hour) is in the range00-23(all hours less than 10 should be zero-filled, i.e. preceded by a0), andmm(minute) is00-59, zero-filled likewise.
21.7. Configuring Centralized Crash Collection
yum install abrt-plugin-reportuploader).
- Complete the following steps on a dedicated system ("server system"):
- Create a directory to which you want the crash reports to be uploaded to. Usually,
/var/spool/abrt-upload/is used (the rest of the document assumes you are using/var/spool/abrt-upload/). Make sure this directory is writable by theabrtuser.Note
When the abrt-desktop package is installed, it creates a new system user and and a group, both namedabrt. This user is used by theabrtddaemon for various things, for example, as the owner:group of/var/spool/abrt/*directories. - In the
/etc/abrt/abrt.confconfiguration file, set theWatchCrashdumpArchiveDirdirective to the following:WatchCrashdumpArchiveDir = /var/spool/abrt-upload/
- Determine your preferred upload mechanism; for example,
FTPorSCP. For more information on how to configureSCP, refer to Section 9.3.2, “Using thescpUtility”.For security reasons, make sure that uploads can only be performed by a specific user and with a password. The rest of the document assumes that the username used for uploads isUSERNAMEand the password isPASSWORD. If you do not already have a suitable username which can be used to perform uploads under, you may use theabrtuser which already exists on every system where ABRT is installed.It is advisable to check whether your upload method works. For more information, refer to Section 21.7.2, “Testing the Upload Method”. - It is advisable to check and modify the following parameters if needed:
- The
MaxCrashReportsSizedirective (in/etc/abrt/abrt.conf) needs to be set to a larger value if the expected volume of crash data is larger than the default1000MB. - The
ProcessUnpackageddirective (in/etc/abrt/abrt.conf) needs to be set toyesand theBacktraceRemotes(in/etc/abrt/plugins/CCpp.conf) needs to be set tonoif the client system and the server system have significantly different sets of installed packages.
- Complete the following steps on every client system which will use the central management method:
- Modify the
/etc/abrt/plugins/ReportUploader.confconfiguration file so that the ReportUploader plugin knows where to copy the saved crash reports in the following way:Enabled = yes Upload = yes URL = ftp://USERNAME:PASSWORD@SERVERNAME/var/spool/abrt-upload/
- To automatically send the crash reports to the server system immediately after the crash occurs, is detected, and saved, set the
[ ActionsAndReporters ]directive in the/etc/abrt/abrt.confconfiguration file to the following:ActionsAndReporters = ReportUploader
- # Alternatively, if user interaction is required before the crash dump is sent to the server system, set the
ReportUploaderto be a reporter plugin for a specific crash type in the[ AnalyzerActionsAndReporters ]section of the/etc/abrt/abrt.confconfiguration file. The user will be required to run abrt-cli or abrt-gui and instruct theabrtddaemon to report the crash and send it to the server system. For example, if you want all crash types to use this method, edit the[ AnalyzerActionsAndReporters ]section in your/etc/abrt/abrt.confconfiguration file in the following way:Kerneloops = ReportUploader CCpp = ReportUploader Python = ReportUploader
21.7.1. Testing ABRT's Crash Detection
kill -s SEGV PID command to terminate a process on a client system. For example, start a sleep process and terminate it with the kill command in the following way:
~]$ sleep 100 & [1] 2823 ~]$ kill -s SEGV 2823ABRT should detect a crash shortly after executing the
kill command. Check that the crash was detected by ABRT on the client system (this can be checked by examining the appropriate syslog file, by running the abrt-cli --list --full command, or by examining the crash dump created in the /var/spool/abrt directory), copied to the server system, unpacked on the server system and can be seen and acted upon using abrt-cli or abrt-gui on the server system.
21.7.2. Testing the Upload Method
FTP client:
~]$ ftp ftp> open SERVERNAME Name: USERNAME Password: PASSWORD ftp> cd /var/spool/abrt-upload 250 Operation successful ftp> put TESTFILE ftp> quit
TESTFILE appeared in the correct directory on the server system.
Part V. Kernel, Module and Driver Configuration
Table of Contents
- 22. Working with Kernel Modules
- 23. Manually Upgrading the Kernel
- 24. The
kdumpCrash Recovery Service
Chapter 22. Working with Kernel Modules
- a device driver which adds support for new hardware; or,
- support for a file system such as
btrfsorNFS.
- use the user-space module-init-tools package to display, query, load and unload kernel modules and their dependencies;
- set module parameters both dynamically on the command line and permanently so that you can customize the behavior of your kernel modules; and,
- load modules at boot time.
Note: Installing the module-init-tools package
~]# yum install module-init-tools22.1. Listing Currently-Loaded Modules
lsmod command:
~]$ lsmod
Module Size Used by
xfs 803635 1
exportfs 3424 1 xfs
vfat 8216 1
fat 43410 1 vfat
tun 13014 2
fuse 54749 2
ip6table_filter 2743 0
ip6_tables 16558 1 ip6table_filter
ebtable_nat 1895 0
ebtables 15186 1 ebtable_nat
ipt_MASQUERADE 2208 6
iptable_nat 5420 1
nf_nat 19059 2 ipt_MASQUERADE,iptable_nat
rfcomm 65122 4
ipv6 267017 33
sco 16204 2
bridge 45753 0
stp 1887 1 bridge
llc 4557 2 bridge,stp
bnep 15121 2
l2cap 45185 16 rfcomm,bnep
cpufreq_ondemand 8420 2
acpi_cpufreq 7493 1
freq_table 3851 2 cpufreq_ondemand,acpi_cpufreq
usb_storage 44536 1
sha256_generic 10023 2
aes_x86_64 7654 5
aes_generic 27012 1 aes_x86_64
cbc 2793 1
dm_crypt 10930 1
kvm_intel 40311 0
kvm 253162 1 kvm_intel
[output truncated]lsmod output specifies:
- the name of a kernel module currently loaded in memory;
- the amount of memory it uses; and,
- the sum total of processes that are using the module and other modules which depend on it, followed by a list of the names of those modules, if there are any. Using this list, you can first unload all the modules depending the module you want to unload. For more information, refer to Section 22.4, “Unloading a Module”.
lsmod output is less verbose and considerably easier to read than the content of the /proc/modules pseudo-file.
22.2. Displaying Information About a Module
modinfo <module_name> command.
Module names do not end in .ko
.ko extension to the end of the name. Kernel module names do not have extensions: their corresponding files do.
e1000e module, which is the Intel PRO/1000 network driver, run:
Example 22.1. Listing information about a kernel module with lsmod
~]#modinfo e1000efilename: /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/net/e1000e/e1000e.ko version: 1.2.7-k2 license: GPL description: Intel(R) PRO/1000 Network Driver author: Intel Corporation, <linux.nics@intel.com> srcversion: 93CB73D3995B501872B2982 alias: pci:v00008086d00001503sv*sd*bc*sc*i* alias: pci:v00008086d00001502sv*sd*bc*sc*i* [somealiaslines omitted] alias: pci:v00008086d0000105Esv*sd*bc*sc*i* depends: vermagic: 2.6.32-71.el6.x86_64 SMP mod_unload modversions parm: copybreak:Maximum size of packet that is copied to a new buffer on receive (uint) parm: TxIntDelay:Transmit Interrupt Delay (array of int) parm: TxAbsIntDelay:Transmit Absolute Interrupt Delay (array of int) parm: RxIntDelay:Receive Interrupt Delay (array of int) parm: RxAbsIntDelay:Receive Absolute Interrupt Delay (array of int) parm: InterruptThrottleRate:Interrupt Throttling Rate (array of int) parm: IntMode:Interrupt Mode (array of int) parm: SmartPowerDownEnable:Enable PHY smart power down (array of int) parm: KumeranLockLoss:Enable Kumeran lock loss workaround (array of int) parm: WriteProtectNVM:Write-protect NVM [WARNING: disabling this can lead to corrupted NVM] (array of int) parm: CrcStripping:Enable CRC Stripping, disable if your BMC needs the CRC (array of int) parm: EEE:Enable/disable on parts that support the feature (array of int)
modinfo output:
- filename
- The absolute path to the
.kokernel object file. You can usemodinfo -nas a shorcut command for printing only thefilenamefield. - description
- A short description of the module. You can use
modinfo -das a shortcut command for printing only the description field. - alias
- The
aliasfield appears as many times as there are aliases for a module, or is omitted entirely if there are none. - depends
- This field contains a comma-separated list of all the modules this module depends on.
Note
If a module has no dependencies, thedependsfield may be omitted from the output. - parm
- Each
parmfield presents one module parameter in the formparameter_name:descriptionparameter_nameis the exact syntax you should use when using it as a module parameter on the command line, or in an option line in a.conffile in the/etc/modprobe.d/directory; and,descriptionis a brief explanation of what the parameter does, along with an expectation for the type of value the parameter accepts (such as int, unit or array of int) in parentheses.
You can list all parameters that the module supports by using the-poption. However, because useful value type information is omitted frommodinfo -poutput, it is more useful to run:~]#
modinfo e1000e |grep "^parm" |sortparm: copybreak:Maximum size of packet that is copied to a new buffer on receive (uint) parm: CrcStripping:Enable CRC Stripping, disable if your BMC needs the CRC (array of int) parm: EEE:Enable/disable on parts that support the feature (array of int) parm: InterruptThrottleRate:Interrupt Throttling Rate (array of int) parm: IntMode:Interrupt Mode (array of int) parm: KumeranLockLoss:Enable Kumeran lock loss workaround (array of int) parm: RxAbsIntDelay:Receive Absolute Interrupt Delay (array of int) parm: RxIntDelay:Receive Interrupt Delay (array of int) parm: SmartPowerDownEnable:Enable PHY smart power down (array of int) parm: TxAbsIntDelay:Transmit Absolute Interrupt Delay (array of int) parm: TxIntDelay:Transmit Interrupt Delay (array of int) parm: WriteProtectNVM:Write-protect NVM [WARNING: disabling this can lead to corrupted NVM] (array of int)
22.3. Loading a Module
modprobe <module_name> as root. For example, to load the wacom module, run:
~]# modprobe wacommodprobe attempts to load the module from /lib/modules/<kernel_version>/kernel/drivers/. In this directory, each type of module has its own subdirectory, such as net/ and scsi/, for network and SCSI interface drivers respectively.
modprobe command always takes dependencies into account when performing operations. When you ask modprobe
to load a specific kernel module, it first examines the dependencies of
that module, if there are any, and loads them if they are not already
loaded into the kernel. modprobe resolves
dependencies recursively: it will load all dependencies of dependencies,
and so on, if necessary, thus ensuring that all dependencies are always
met.
-v (i.e. --verbose) option to cause modprobe
to display detailed information about what it is doing, which may
include loading module dependencies. Here's an example of loading the Fibre Channel over Ethernet module verbosely:
Example 22.2. modprobe -v shows module dependencies as they are loaded
~]# modprobe -v fcoe
insmod /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/scsi/scsi_tgt.ko
insmod /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/scsi/scsi_transport_fc.ko
insmod /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/scsi/libfc/libfc.ko
insmod /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/scsi/fcoe/libfcoe.ko
insmod /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/scsi/fcoe/fcoe.komodprobe loaded the scsi_tgt, scsi_transport_fc, libfc and libfcoe modules as dependencies before finally loading fcoe. Also note that modprobe used the more “primitive” insmod command to insert the modules into the running kernel.
Always use modprobe instead of insmod!
insmod command can also be used to load kernel modules, it does not resolve dependencies. Because of this, you should always load modules using modprobe instead.
22.4. Unloading a Module
modprobe -r <module_name> as root. For example, assuming that the wacom module is already loaded into the kernel, you can unload it by running:
~]# modprobe -r wacom- the
wacommodule, - a module that
wacomdirectly depends on, or, - any module that
wacom—through the dependency tree—depends on indirectly.
lsmod to obtain the names of the modules which are preventing you from unloading a certain module.
firewire_ohci
module because (because you believe there is a bug in it that is
affecting system stability, for example), your terminal session might
look similar to this:
~]#modinfo -F depends firewire_ohcidepends: firewire-core ~]#modinfo -F depends firewire_coredepends: crc-itu-t ~]#modinfo -F depends crc-itu-tdepends:
firewire_ohci depends on firewire_core, which itself depends on crc-itu-t.
firewire_ohci using the modprobe -v -r <module_name> command, where -r is short for --remove and -v for --verbose:
~]# modprobe -r -v firewire_ohci
rmmod /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/firewire/firewire-ohci.ko
rmmod /lib/modules/2.6.32-71.el6.x86_64/kernel/drivers/firewire/firewire-core.ko
rmmod /lib/modules/2.6.32-71.el6.x86_64/kernel/lib/crc-itu-t.koDo not use rmmod directly!
rmmod command can be used to unload kernel modules, it is recommended to use modprobe -r instead.
22.5. Setting Module Parameters
- You can unload all dependencies of the module you want to set parameters for, unload the module using
modprobe -r, and then load it withmodprobealong with a list of customized parameters. This method is often used when the module does not have many dependencies, or to test different combinations of parameters without making them persistent, and is the method covered in this section. - Alternatively, you can list the new parameters in an existing or newly-created file in the
/etc/modprobe.d/directory. This method makes the module parameters persistent by ensuring that they are set each time the module is loaded, such as after every reboot ormodprobecommand. This method is covered in Section 22.6, “Persistent Module Loading”, though the following information is a prerequisite.
modprobe to load a kernel module with custom parameters using the following command line format:
Example 22.3. Supplying optional parameters when loading a kernel module
~]# modprobe <module_name> [parameter=value] - You can enter multiple parameters and values by separating them with spaces.
- Some module parameters expect a list of comma-separated values as their argument. When entering the list of values, do not insert a space after each comma, or
modprobewill incorrectly interpret the values following spaces as additional parameters. - The
modprobecommand silently succeeds with an exit status of0if:- it successfully loads the module, or
- the module is already loaded into the kernel.
Thus, you must ensure that the module is not already loaded before attempting to load it with custom parameters. Themodprobecommand does not automatically reload the module, or alert you that it is already loaded.
e1000e module, which is the network driver for Intel PRO/1000 network adapters, as an example:
Procedure 22.1. Loading a Kernel Module with Custom Parameters
- First, ensure the module is not already loaded into the kernel:
~]#
lsmod |grep e1000e~]#Output indicates that the module is already loaded into the kernel, in which case you must first unload it before proceeding. Refer to Section 22.4, “Unloading a Module” for instructions on safely unloading it. - Load the module and list all custom parameters after the module name. For example, if you wanted to load the Intel PRO/1000 network driver with the interrupt throttle rate set to 3000 interrupts per second for the first, second and third instances of the driver, and Energy Efficient Ethernet (EEE) turned on[4] , you would run, as root:
~]#
modprobe e1000e InterruptThrottleRate=3000,3000,3000 EEE=1This example illustrates passing multiple valued to a single parameter by separating them with commas and omitting any spaces between them.
22.6. Persistent Module Loading
<file_name>.modules/etc/sysconfig/modules/ directory, where <file_name> is any descriptive name of your choice. Your <file_name>.modulesExample 22.4. First line of a file_name.modules file
#!/bin/sh
<file_name>.modulesmodules]# chmod +x <file_name>.modulesbluez-uinput.modules script loads the uinput module:
Example 22.5. /etc/sysconfig/modules/bluez-uinput.modules
#!/bin/sh if [ ! -c /dev/input/uinput ] ; then exec /sbin/modprobe uinput >/dev/null 2>&1 fi
if-conditional statement on the third line ensures that the /dev/input/uinput file does not already exist (the ! symbol negates the condition), and, if that is the case, loads the uinput module by calling exec /sbin/modprobe uinput. Note that the uinput module creates the /dev/input/uinput file, so testing to see if that file exists serves as verification of whether the uinput module is loaded into the kernel.
>/dev/null 2>&1 clause at the end of that line simply redirects any output to /dev/null so that the modprobe command remains quiet.
22.7. Specific Kernel Module Capabilities
22.7.1. Using Multiple Ethernet Cards
alias and, possibly, options lines for each card in a user-created <module_name>.conf/etc/modprobe.d/ directory.
22.7.2. Using Channel Bonding
bonding kernel module and a special network interface, called a channel bonding interface.
Channel bonding enables two or more network interfaces to act as one,
simultaneously increasing the bandwidth and providing redundancy.
- As root, create a new file named
<bonding>.conf/etc/modprobe.d/directory. Note that you can name this file anything you like as long as it ends with a.confextension. Insert the following line in this new file:alias bond
<N>bondingReplace<N>with the interface number, such as0. For each configured channel bonding interface, there must be a corresponding entry in your new/etc/modprobe.d/file.<bonding>.conf - Configure a channel bonding interface as outlined in Section 4.2.2, “Channel Bonding Interfaces”.
- To enhance performance, adjust available module options to ascertain what combination works best. Pay particular attention to the
miimonorarp_intervaland thearp_ip_targetparameters. Refer to Section 22.7.2.1, “Bonding Module Directives” for a list of available options and how to quickly determine the best ones for your bonded interface.
22.7.2.1. Bonding Module Directives
BONDING_OPTS="<bonding parameters>" directive in your bonding interface configuration file (ifcfg-bond0
for example). Parameters to bonded interfaces can be configured without
unloading (and reloading) the bonding module by manipulating files in
the sysfs file system.
sysfs is a virtual file system that represents kernel objects as directories, files and symbolic links. sysfs
can be used to query for information about kernel objects, and can also
manipulate those objects through the use of normal file system
commands. The sysfs virtual file system has a line in /etc/fstab, and is mounted under the /sys/ directory. All bonding interfaces can be configured dynamically by interacting with and manipulating files under the /sys/class/net/ directory.
ifcfg-bond0 and inserted SLAVE=yes and MASTER=bond0 directives in the configuration files for each interface bonded to bond0 following the instructions in Section 4.2.2, “Channel Bonding Interfaces”, you can proceed to testing and determining the best parameters for your bonding interface.
ifconfig bond<N> up as root:
~]# ifconfig bond0 upifcfg-bond0 bonding interface file, you will be able to see bond0 listed in the output of running ifconfig (without any options):
~]# ifconfig
bond0 Link encap:Ethernet HWaddr 00:00:00:00:00:00
UP BROADCAST RUNNING MASTER MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 b) TX bytes:0 (0.0 b)
eth0 Link encap:Ethernet HWaddr 52:54:00:26:9E:F1
inet addr:192.168.122.251 Bcast:192.168.122.255 Mask:255.255.255.0
inet6 addr: fe80::5054:ff:fe26:9ef1/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:207 errors:0 dropped:0 overruns:0 frame:0
TX packets:205 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:70374 (68.7 KiB) TX bytes:25298 (24.7 KiB)
[output truncated]~]# cat /sys/class/net/bonding_masters
bond0/sys/class/net/bond<N>/bonding/ directory. First, the bond you are configuring must be taken down:
~]# ifconfig bond0 down~]# echo 1000 > /sys/class/net/bond0/bonding/miimonbalance-alb mode, you could run either:
~]# echo 6 > /sys/class/net/bond0/bonding/mode~]# echo balance-alb > /sys/class/net/bond0/bonding/modeifconfig bond<N> up . If you decide to change the options, take the interface down, modify its parameters using sysfs, bring it back up, and re-test.
BONDING_OPTS= directive of the /etc/sysconfig/network-scripts/ifcfg-bond<N>
file for the bonding interface you are configuring. Whenever that bond
is brought up (for example, by the system during the boot sequence if
the ONBOOT=yes directive is set), the bonding options specified in the BONDING_OPTS will take effect for that bond. For more information on configuring bonding interfaces (and BONDING_OPTS), refer to Section 4.2.2, “Channel Bonding Interfaces”.
parm in modinfo bonding output, or the exhaustive descriptions in the bonding.txt file in the kernel-doc package (see Section 22.8, “Additional Resources”).
Bonding Interface Parameters
-
arp_interval=<time_in_milliseconds> - Specifies (in milliseconds) how often ARP monitoring occurs.
Important
It is essential that botharp_intervalandarp_ip_targetparameters are specified, or, alternatively, themiimonparameter is specified. Failure to do so can cause degradation of network performance in the event that a link fails.If using this setting while inmode=0ormode=1(the two load-balancing modes), the network switch must be configured to distribute packets evenly across the NICs. For more information on how to accomplish this, refer to/usr/share/doc/kernel-doc-<kernel_version>/Documentation/networking/bonding.txtThe value is set to0by default, which disables it. -
arp_ip_target=<ip_address>[,<ip_address_2>,…<ip_address_16>] - Specifies the target IP address of ARP requests when the
arp_intervalparameter is enabled. Up to 16 IP addresses can be specified in a comma separated list. -
arp_validate=<value> - Validate source/distribution of ARP probes; default is
none. Other valid values areactive,backup, andall. -
debug=<number> - Enables debug messages. Possible values are:
0— Debug messages are disabled. This is the default.1— Debug messages are enabled.
-
downdelay=<time_in_milliseconds> - Specifies (in milliseconds) how long to wait after link failure before disabling the link. The value must be a multiple of the value specified in the
miimonparameter. The value is set to0by default, which disables it. - lacp_rate=
<value> - Specifies the rate at which link partners should transmit LACPDU packets in 802.3ad mode. Possible values are:
slowor0— Default setting. This specifies that partners should transmit LACPDUs every 30 seconds.fastor1— Specifies that partners should transmit LACPDUs every 1 second.
-
miimon=<time_in_milliseconds> - Specifies (in milliseconds) how often MII link monitoring occurs. This is useful if high availability is required because MII is used to verify that the NIC is active. To verify that the driver for a particular NIC supports the MII tool, type the following command as root:
~]#
ethtool<interface_name>| grep "Link detected:"In this command, replace<interface_name> with the name of the device interface, such aseth0, not the bond interface. If MII is supported, the command returns:Link detected: yes
If using a bonded interface for high availability, the module for each NIC must support MII. Setting the value to0(the default), turns this feature off. When configuring this setting, a good starting point for this parameter is100.Important
It is essential that botharp_intervalandarp_ip_targetparameters are specified, or, alternatively, themiimonparameter is specified. Failure to do so can cause degradation of network performance in the event that a link fails. -
mode=<value> - ...where
<value>is one of:balance-rror0— Sets a round-robin policy for fault tolerance and load balancing. Transmissions are received and sent out sequentially on each bonded slave interface beginning with the first one available.active-backupor1— Sets an active-backup policy for fault tolerance. Transmissions are received and sent out via the first available bonded slave interface. Another bonded slave interface is only used if the active bonded slave interface fails.balance-xoror2— Sets an XOR (exclusive-or) policy for fault tolerance and load balancing. Using this method, the interface matches up the incoming request's MAC address with the MAC address for one of the slave NICs. Once this link is established, transmissions are sent out sequentially beginning with the first available interface.broadcastor3— Sets a broadcast policy for fault tolerance. All transmissions are sent on all slave interfaces.802.3ador4— Sets an IEEE 802.3ad dynamic link aggregation policy. Creates aggregation groups that share the same speed and duplex settings. Transmits and receives on all slaves in the active aggregator. Requires a switch that is 802.3ad compliant.balance-tlbor5— Sets a Transmit Load Balancing (TLB) policy for fault tolerance and load balancing. The outgoing traffic is distributed according to the current load on each slave interface. Incoming traffic is received by the current slave. If the receiving slave fails, another slave takes over the MAC address of the failed slave.balance-albor6— Sets an Active Load Balancing (ALB) policy for fault tolerance and load balancing. Includes transmit and receive load balancing for IPV4 traffic. Receive load balancing is achieved through ARP negotiation.
-
num_unsol_na=<number> - Specifies the number of unsolicited IPv6 Neighbor Advertisements to be issued after a failover event. One unsolicited NA is issued immediately after the failover.The valid range is
0 - 255; the default value is1. This parameter affects only the active-backup mode. -
primary=<interface_name> - Specifies the interface name, such as
eth0, of the primary device. Theprimarydevice is the first of the bonding interfaces to be used and is not abandoned unless it fails. This setting is particularly useful when one NIC in the bonding interface is faster and, therefore, able to handle a bigger load.This setting is only valid when the bonding interface is inactive-backupmode. Refer to/usr/share/doc/kernel-doc-for more information.<kernel-version>/Documentation/networking/bonding.txt -
primary_reselect=<value> - Specifies the reselection policy for the primary slave. This affects how the primary slave is chosen to become the active slave when failure of the active slave or recovery of the primary slave occurs. This parameter is designed to prevent flip-flopping between the primary slave and other slaves. Possible values are:
alwaysor0(default) — The primary slave becomes the active slave whenever it comes back up.betteror1— The primary slave becomes the active slave when it comes back up, if the speed and duplex of the primary slave is better than the speed and duplex of the current active slave.failureor2— The primary slave becomes the active slave only if the current active slave fails and the primary slave is up.
Theprimary_reselectsetting is ignored in two cases:- If no slaves are active, the first slave to recover is made the active slave.
- When initially enslaved, the primary slave is always made the active slave.
Changing theprimary_reselectpolicy viasysfswill cause an immediate selection of the best active slave according to the new policy. This may or may not result in a change of the active slave, depending upon the circumstances -
updelay=<time_in_milliseconds> - Specifies (in milliseconds) how long to wait before enabling a link. The value must be a multiple of the value specified in the
miimonparameter. The value is set to0by default, which disables it. -
use_carrier=<number> - Specifies whether or not
miimonshould use MII/ETHTOOL ioctls ornetif_carrier_ok()to determine the link state. Thenetif_carrier_ok()function relies on the device driver to maintains its state withnetif_carrier_; most device drivers support this function.on/offThe MII/ETHROOL ioctls tools utilize a deprecated calling sequence within the kernel. However, this is still configurable in case your device driver does not supportnetif_carrier_.on/offValid values are:1— Default setting. Enables the use ofnetif_carrier_ok().0— Enables the use of MII/ETHTOOL ioctls.
Tip
If the bonding interface insists that the link is up when it should not be, it is possible that your network device driver does not supportnetif_carrier_.on/off -
xmit_hash_policy=<value> - Selects the transmit hash policy used for slave selection in
balance-xorand802.3admodes. Possible values are:0orlayer2— Default setting. This parameter uses the XOR of hardware MAC addresses to generate the hash. The formula used is:(
<source_MAC_address>XOR<destination_MAC>) MODULO<slave_count>This algorithhm will place all traffic to a particular network peer on the same slave, and is 802.3ad compliant.1orlayer3+4— Uses upper layer protocol information (when available) to generate the hash. This allows for traffic to a particular network peer to span multiple slaves, although a single connection will not span multiple slaves.The formula for unfragmented TCP and UDP packets used is:((
<source_port>XOR<dest_port>) XOR ((<source_IP>XOR<dest_IP>) AND0xffff) MODULO<slave_count>For fragmented TCP or UDP packets and all other IP protocol traffic, the source and destination port information is omitted. For non-IP traffic, the formula is the same as thelayer2transmit hash policy.This policy intends to mimic the behavior of certain switches; particularly, Cisco switches with PFC2 as well as some Foundry and IBM products.The algorithm used by this policy is not 802.3ad compliant.2orlayer2+3— Uses a combination of layer2 and layer3 protocol information to generate the hash.Uses XOR of hardware MAC addresses and IP addresses to generate the hash. The formula is:(((
<source_IP>XOR<dest_IP>) AND0xffff) XOR (<source_MAC>XOR<destination_MAC>)) MODULO<slave_count>This algorithm will place all traffic to a particular network peer on the same slave. For non-IP traffic, the formula is the same as for the layer2 transmit hash policy.This policy is intended to provide a more balanced distribution of traffic than layer2 alone, especially in environments where a layer3 gateway device is required to reach most destinations.This algorithm is 802.3ad compliant.
22.8. Additional Resources
Manual Page Documentation
man lsmod— Thelsmodmanual page contains usage information and explanation of all options.man modinfo— Themodinfomanual page contains usage information and explanation of all options.man modprobe— Themodprobemanual page contains usage information and explanation of all options.man rmmod— Thermmodmanual page contains usage information and explanation of all options.man ethtool— Theethtoolmanual page contains usage information and explanation of all options.man mii-tool— Themii-toolmanual page contains usage information and explanation of all options.
Installable and External Documentation
/usr/share/doc/kernel-doc-— This directory, which is provided by the kernel-doc package, contains information on the kernel, kernel modules, and their respective parameters. Before accessing the kernel documentation, you must run the following command as root:<kernel_version>/Documentation/~]#
yum install kernel-doc- Linux Loadable Kernel Module HOWTO — The Linux Loadable Kernel Module HOWTO from the Linux Documentation Project contains further information on working with kernel modules.
[4]
Despite what the example might imply, Energy Efficient Ethernet is turned on by default in the e1000e driver.
Chapter 23. Manually Upgrading the Kernel
rpm command instead of yum.
Use Yum to Install Kernels Whenever Possible
Important
23.1. Overview of Kernel Packages
- kernel — Contains the kernel for single, multicore and multiprocessor systems.
- kernel-debug — Contains a kernel with numerous debugging options enabled for kernel diagnosis, at the expense of reduced performance.
- kernel-devel — Contains the kernel headers and makefiles sufficient to build modules against the kernel package.
- kernel-debug-devel — Contains the development version of the kernel with numerous debugging options enabled for kernel diagnosis, at the expense of reduced performance.
- kernel-doc — Documentation files from the kernel source. Various portions of the Linux kernel and the device drivers shipped with it are documented in these files. Installation of this package provides a reference to the options that can be passed to Linux kernel modules at load time.By default, these files are placed in the
/usr/share/doc/kernel-doc-directory.<kernel_version>/ - kernel-headers — Includes the C header files that specify the interface between the Linux kernel and user-space libraries and programs. The header files define structures and constants that are needed for building most standard programs.
- kernel-firmware — Contains all of the firmware files that are required by various devices to operate.
- perf — This package contains supporting scripts and documentation for the perf tool shipped in each kernel image subpackage.
23.2. Preparing to Upgrade
VFAT file system. You can create bootable USB media on media formatted as ext2, ext3, or VFAT.
4 GB is required for a distribution DVD image, around 700 MB for a distribution CD image, or around 10 MB for a minimal boot media image.
boot.iso
file from a Red Hat Enterprise Linux installation DVD, or installation
CD-ROM#1, and you need a USB storage device formatted with the VFAT file system and around 16 MB
of free space. The following procedure will not affect existing files
on the USB storage device unless they have the same path names as the
files that you copy onto it. To create USB boot media, perform the
following commands as the root user:
- Install the SYSLINUX bootloader on the USB storage device:
~]#
syslinux /dev/sdX1...wheresdXis the device name. - Create mount points for
boot.isoand the USB storage device:~]#
mkdir /mnt/isoboot /mnt/diskboot - Mount
boot.iso:~]#
mount -o loop boot.iso /mnt/isoboot - Mount the USB storage device:
~]#
mount /dev/<sdX1>/mnt/diskboot - Copy the ISOLINUX files from the
boot.isoto the USB storage device:~]#
cp /mnt/isoboot/isolinux/* /mnt/diskboot - Use the
isolinux.cfgfile fromboot.isoas thesyslinux.cfgfile for the USB device:~]#
grep -v local /mnt/isoboot/isolinux/isolinux.cfg > /mnt/diskboot/syslinux.cfg - Unmount
boot.isoand the USB storage device:~]#
umount /mnt/isoboot /mnt/diskboot - You should reboot the machine with the boot media and verify that you are able to boot with it before continuing.
mkbootdisk command as root. Refer to man mkbootdisk man page after installing the package for usage information.
yum list installed "kernel-*"
at a shell prompt. The output will comprise some or all of the
following packages, depending on the system's architecture, and the
version numbers may differ:
~]# yum list installed "kernel-*"
kernel.x86_64 2.6.32-17.el6 installed
kernel-doc.noarch 2.6.32-17.el6 installed
kernel-firmware.noarch 2.6.32-17.el6 installed
kernel-headers.x86_64 2.6.32-17.el6 installed
23.3. Downloading the Upgraded Kernel
- Security Errata — Refer to http://www.redhat.com/security/updates/ for information on security errata, including kernel upgrades that fix security issues.
- Via Red Hat Network — Download and install the kernel RPM packages. Red Hat Network can download the latest kernel, upgrade the kernel on the system, create an initial RAM disk image if needed, and configure the boot loader to boot the new kernel. For more information, refer to http://www.redhat.com/docs/manuals/RHNetwork/.
23.4. Performing the Upgrade
Important
-i argument with the rpm command to keep the old kernel. Do not use the -U option, since it overwrites the currently installed kernel, which creates boot loader problems. For example:
~]# rpm -ivh kernel-<kernel_version>.<arch>.rpm 23.5. Verifying the Initial RAM Disk Image
initramfs by running the dracut command. However, you usually don't need to create an initramfs
manually: this step is automatically performed if the kernel and its
associated packages are installed or upgraded from RPM packages
distributed by Red Hat.
initramfs corresponding to your current kernel version exists and is specified correctly in the grub.conf configuration file by following this procedure:
Procedure 23.1. Verifying the Initial RAM Disk Image
- As root, list the contents in the
/boot/directory and find the kernel (vmlinuz-) and<kernel_version>initramfs-with the latest (most recent) version number:<kernel_version>Example 23.1. Ensuring that the kernel and initramfs versions match
~]#
ls /boot/config-2.6.32-17.el6.x86_64 lost+found config-2.6.32-19.el6.x86_64 symvers-2.6.32-17.el6.x86_64.gz config-2.6.32-22.el6.x86_64 symvers-2.6.32-19.el6.x86_64.gz efi symvers-2.6.32-22.el6.x86_64.gz grub System.map-2.6.32-17.el6.x86_64 initramfs-2.6.32-17.el6.x86_64.img System.map-2.6.32-19.el6.x86_64 initramfs-2.6.32-19.el6.x86_64.img System.map-2.6.32-22.el6.x86_64 initramfs-2.6.32-22.el6.x86_64.img vmlinuz-2.6.32-17.el6.x86_64 initrd-2.6.32-17.el6.x86_64kdump.img vmlinuz-2.6.32-19.el6.x86_64 initrd-2.6.32-19.el6.x86_64kdump.img vmlinuz-2.6.32-22.el6.x86_64 initrd-2.6.32-22.el6.x86_64kdump.img- we have three kernels installed (or, more correctly, three kernel files are present in
/boot/), - the latest kernel is
vmlinuz-2.6.32-22.el6.x86_64, and - an
initramfsfile matching our kernel version,initramfs-2.6.32-22.el6.x86_64kdump.img, also exists.
initrd files in the /boot directory are not the same as initramfs files
In the/boot/directory you may find severalinitrd-files. These are special files created by the Kdump mechanism for kernel debugging purposes, are not used to boot the system, and can safely be ignored.<version>kdump.img - (Optional) If your
initramfs-file does not match the version of the latest kernel in<kernel_version>/boot/, or, in certain other situations, you may need to generate aninitramfsfile with the Dracut utility. Simply invokingdracutas root without options causes it to generate aninitramfsfile in the/boot/directory for the latest kernel present in that directory:~]#
dracutYou must use the--forceoption if you wantdracutto overwrite an existinginitramfs(for example, if yourinitramfshas become corrupt). Otherwisedracutwill refuse to overwrite the existinginitramfsfile:~]#
dracutWill not override existing initramfs (/boot/initramfs-2.6.32-22.el6.x86_64.img) without --forceYou can create an initramfs in the current directory by callingdracut:<initramfs_name><kernel_version>~]#
dracut "initramfs-$(uname -r).img" $(uname -r)If you need to specify specific kernel modules to be preloaded, add the names of those modules (minus any file name suffixes such as.ko) inside the parentheses of theadd_dracutmodules="directive of the<module>[<more_modules>]"/etc/dracut.confconfiguration file. You can list the file contents of aninitramfsimage file created by dracut by using thelsinitrdcommand:<initramfs_file>~]#
lsinitrd initramfs-2.6.32-22.el6.x86_64.imginitramfs-2.6.32-22.el6.x86_64.img: ======================================================================== dracut-004-17.el6 ======================================================================== drwxr-xr-x 23 root root 0 May 3 22:34 . drwxr-xr-x 2 root root 0 May 3 22:33 proc -rwxr-xr-x 1 root root 7575 Mar 25 19:53 init drwxr-xr-x 7 root root 0 May 3 22:34 etc drwxr-xr-x 2 root root 0 May 3 22:34 etc/modprobe.d [output truncated]Refer toman dracutandman dracut.conffor more information on options and usage. - Examine the
grub.confconfiguration file in the/boot/grub/directory to ensure that aninitrdexists for the kernel version you are booting. Refer to Section 23.6, “Verifying the Boot Loader” for more information.initramfs-<kernel_version>.img
Verifying the Initial RAM Disk Image and Kernel on IBM eServer System i
addRamDisk
command. This step is performed automatically if the kernel and its
associated packages are installed or upgraded from the RPM packages
distributed by Red Hat; thus, it does not need to be executed manually.
To verify that it was created, use the command ls -l /boot/ to make sure the /boot/vmlinitrd-<kernel_version> file already exists (the <kernel_version> 23.6. Verifying the Boot Loader
rpm, the kernel package creates an entry in the boot loader configuration file for that new kernel. However, rpm does not configure the new kernel to boot as the default kernel. You must do this manually when installing a new kernel with rpm.
rpm
to ensure that the configuration is correct. Otherwise, the system may
not be able to boot into Red Hat Enterprise Linux properly. If this
happens, boot the system with the boot media created earlier and
re-configure the boot loader.
Table 23.1. Boot Loaders by Architecture
| Architecture | Boot Loader | Refer to |
|---|---|---|
| x86 | GRUB | Section 23.6.1, “Configuring the GRUB Boot Loader” |
| AMD® AMD64 or Intel 64® | GRUB | Section 23.6.1, “Configuring the GRUB Boot Loader” |
| IBM® eServer™ System i™ | OS/400® | Section 23.6.2, “Configuring the OS/400® Boot Loader” |
| IBM® eServer™ System p™ | YABOOT | Section 23.6.3, “Configuring the YABOOT Boot Loader” |
| IBM® System z® | z/IPL |
23.6.1. Configuring the GRUB Boot Loader
/boot/grub/grub.conf, contains a few lines with directives, such as default, timeout, splashimage and hiddenmenu (the last directive has no argument). The remainder of the file contains 4-line stanzas that each refer to an installed kernel. These stanzas always start with a title entry, after which the associated root, kernel and initrd directives should always be indented. Ensure that each stanza starts with a title that contains a version number (in parentheses) that matches the version number in the kernel /vmlinuz-<version_number> line of the same stanza.
Example 23.2. /boot/grub/grub.conf
# grub.conf generated by anaconda
[comments omitted]
default=1
timeout=0
splashimage=(hd0,0)/grub/splash.xpm.gz
hiddenmenu
title Red Hat Enterprise Linux (2.6.32-22.el6.x86_64)
root (hd0,0)
kernel /vmlinuz-2.6.32-22.el6.x86_64 ro root=/dev/mapper/vg_vm6b-lv_root rd_LVM_LV=vg_vm6b/lv_root rd_NO_LUKS rd_NO_MD rd_NO_DM LANG=en_US.UTF-8 SYSFONT=latarcyrheb-sun16 KEYBOARDTYPE=pc KEYTABLE=us rhgb quiet crashkernel=auto
initrd /initramfs-2.6.32-22.el6.x86_64.img
title Red Hat Enterprise Linux (2.6.32-19.el6.x86_64)
root (hd0,0)
kernel /vmlinuz-2.6.32-19.el6.x86_64 ro root=/dev/mapper/vg_vm6b-lv_root rd_LVM_LV=vg_vm6b/lv_root rd_NO_LUKS rd_NO_MD rd_NO_DM LANG=en_US.UTF-8 SYSFONT=latarcyrheb-sun16 KEYBOARDTYPE=pc KEYTABLE=us rhgb quiet crashkernel=auto
initrd /initramfs-2.6.32-19.el6.x86_64.img
title Red Hat Enterprise Linux 6 (2.6.32-17.el6.x86_64)
root (hd0,0)
kernel /vmlinuz-2.6.32-17.el6.x86_64 ro root=/dev/mapper/vg_vm6b-lv_root rd_LVM_LV=vg_vm6b/lv_root rd_NO_LUKS rd_NO_MD rd_NO_DM LANG=en_US.UTF-8 SYSFONT=latarcyrheb-sun16 KEYBOARDTYPE=pc KEYTABLE=us rhgb quiet
initrd /initramfs-2.6.32-17.el6.x86_64.img/boot/ partition was created, the paths to the kernel and the initramfs image are relative to /boot/. This is the case in Example 23.2, “/boot/grub/grub.conf”, above. Therefore the initrd /initramfs-2.6.32-22.el6.x86_64.img line in the first kernel stanza means that the initramfs image is actually located at /boot/initramfs-2.6.32-22.el6.x86_64.img when the root file system is mounted, and likewise for the kernel path (for example: kernel /vmlinuz-2.6.32-22.el6.x86_64) in each stanza of grub.conf.
The initrd directive in grub.conf refers to an initramfs image
grub.conf, the initrd directive must point to the location (relative to the /boot/ directory if it is on a separate partition), of the initramfs file corresponding to the same kernel version. This directive is called initrd because the previous tool which created initial RAM disk images, mkinitrd, created what were known as initrd files. Thus the grub.conf directive remains initrd to maintain compatibility with other tools. The file-naming convention of systems using the dracut utility to create the initial RAM disk image is: initramfs-<kernel_version>.img
mkinitrd. For information on using Dracut, refer to Section 23.5, “Verifying the Initial RAM Disk Image”.
kernel /vmlinuz-<kernel_version> line matches the version number of the initramfs image given on the initrd /initramfs-<kernel_version>.img line of each stanza. Refer to Procedure 23.1, “Verifying the Initial RAM Disk Image” for more information.
default= directive tells GRUB which kernel to boot by default. Each title in grub.conf represents a bootable kernel. GRUB counts the titled stanzas representing bootable kernels starting with 0. In Example 23.2, “/boot/grub/grub.conf”, the line default=1 indicates that GRUB will boot, by default, the second kernel entry, i.e. title Red Hat Enterprise Linux (2.6.32-19.el6.x86_64).
title entry in grub.conf, we would need to change the default value to 0.
rpm, verify that /boot/grub/grub.conf is correct, change the default= value to the new kernel (while remembering to count from 0), and reboot the computer into the new kernel. Ensure your hardware is detected by watching the boot process output.
Important: Causing the GRUB boot menu to display
timeout directive in grub.conf to 0,
GRUB will not display its list of bootable kernels when the system
starts up. In order to display this list when booting, press and hold
any alphanumeric key while and immediately after BIOS information is
displayed, and GRUB will present you with the GRUB menu.
23.6.2. Configuring the OS/400® Boot Loader
/boot/vmlinitrd-<kernel-version> file is installed when you upgrade the kernel. However, you must use the dd command to configure the system to boot the new kernel.
- As root, issue the command
cat /proc/iSeries/mf/sideto determine the default side (either A, B, or C). - As root, issue the following command, where
<kernel-version>is the version of the new kernel and<side>is the side from the previous command:dd if=/boot/vmlinitrd-<kernel-version>of=/proc/iSeries/mf/<side>/vmlinux bs=8k
23.6.3. Configuring the YABOOT Boot Loader
/etc/aboot.conf as its configuration file. Confirm that the file contains an image section with the same version as the kernel package just installed, and likewise for the initramfs image:
boot=/dev/sda1 init-message=Welcome to Red Hat Enterprise Linux! Hit <TAB> for boot options partition=2 timeout=30 install=/usr/lib/yaboot/yaboot delay=10 nonvram image=/vmlinuz-2.6.32-17.EL label=old read-only initrd=/initramfs-2.6.32-17.EL.img append="root=LABEL=/" image=/vmlinuz-2.6.32-19.EL label=linux read-only initrd=/initramfs-2.6.32-19.EL.img append="root=LABEL=/"
default and set it to the label of the image stanza that contains the new kernel.
Chapter 24. The kdump Crash Recovery Service
kdump is an advanced crash dumping
mechanism. When enabled, the system is booted from the context of
another kernel. This second kernel reserves a small amount of memory,
and its only purpose is to capture the core dump image in case the
system crashes. Since being able to analyze the core dump helps
significantly to determine the exact cause of the system failure, it is
strongly recommended to have this feature enabled.
kdump service in Red Hat Enterprise Linux, and provides a brief overview of how to analyze the resulting core dump using the crash debugging utility.
24.1. Configuring the kdump Service
kdump service: at the first boot, using the Kernel Dump Configuration
graphical utility, and doing so manually on the command line. It also
describes how to test the configuration to verify that everything works
as expected.
Note: Make Sure You Have kexec-tools Installed
kdump service, you must have the kexec-tools package installed. Refer to Section 1.2.2, “Installing” for more information on how to install new packages in Red Hat Enterprise Linux.
24.1.1. Configuring the kdump at First Boot
kdump, navigate to the Kdump section, and follow the instructions below.
Important: Make Sure the System Has Enough Memory
kdump
crash recovery is enabled, the minimum memory requirements increase by
the amount of memory reserved for it. This value is determined by a
user, and defaults to 128 MB.
24.1.1.1. Enabling the Service
kdump daemon at boot time, select the Enable kdump? check box. This will enable the service for runlevels 2, 3, 4, and 5,
and start it for the current session. Similarly, unselecting the check
box will disable it for all runlevels and stop the service immediately.
24.1.1.2. Configuring the Memory Usage
kdump kernel, click the up and down arrow buttons next to the Kdump Memory field to increase or decrease the value. Notice that the Usable System Memory field changes accordingly showing you the remaining memory that will be available to the system.
24.1.2. Using the Kernel Dump Configuration Utility
system-config-kdump at a shell prompt (for example, xterm or GNOME Terminal). You will be presented with a window as shown in Figure 24.1, “Basic Settings”.
kdump as well as to enable or disable starting the service at boot time. When you are done, click
to save the changes. The system reboot will be requested, and unless
you are already authenticated, you will be prompted to enter the
superuser password.
Important: Make Sure the System Has Enough Memory
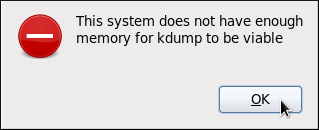
kdump
crash recovery is enabled, the minimum memory requirements increase by
the amount of memory reserved for it. This value is determined by a
user, and defaults to 128 MB.
24.1.2.1. Enabling the Service
kdump daemon at boot time, click the button on the toolbar. This will enable the service for runlevels 2, 3, 4, and 5, and start it for the current session. Similarly, clicking the button will disable it for all runlevels and stop the service immediately.
24.1.2.2. The Basic Settings Tab
kdump kernel. To do so, select the Manual kdump memory settings radio button, and click the up and down arrow buttons next to the New kdump Memory field to increase or decrease the value. Notice that the Usable Memory field changes accordingly showing you the remaining memory that will be available to the system.
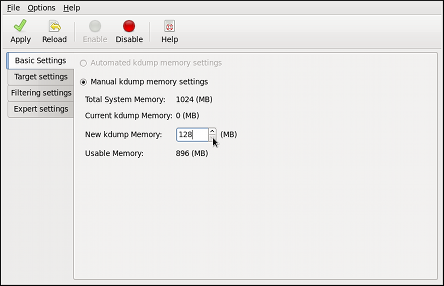
Figure 24.1. Basic Settings
24.1.2.3. The Target Settings Tab
vmcore
dump. It can be either stored as a file in a local file system, written
directly to a device, or sent over a network using the NFS (Network
File System) or SSH (Secure Shell) protocol.
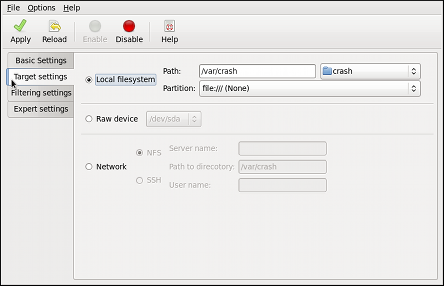
Figure 24.2. Target Settings
Important: Using the hpsa Driver for a Storage
hpsa driver, kdump
is unable to save the dump to a storage that uses this driver for HP
Smart Array Controllers. If this applies to your machine, it is advised
that you save the dump to a remote system using the NFS or SSH protocol
instead.
24.1.2.4. The Filtering Settings Tab
vmcore dump.
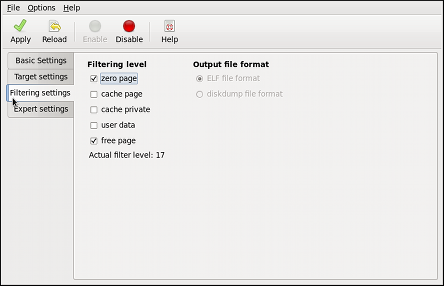
Figure 24.3. Filtering Settings
24.1.2.5. The Expert Settings Tab
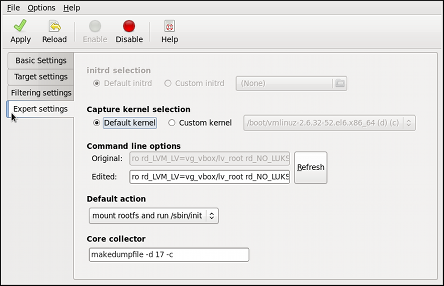
Figure 24.4. Expert Settings
makedumpfile core collector, edit the Core collector text field; see Section 24.1.3.3, “Configuring the Core Collector” for more information.
24.1.3. Configuring kdump on the Command Line
~]$ su -
Password:24.1.3.1. Configuring the Memory Usage
kdump kernel, open the /boot/grub/grub.conf file in a text editor such as vi or nano, and add the crashkernel=<size>M parameter to the list of kernel options as shown in Example 24.1, “A sample /boot/grub/grub.conf file”.
Example 24.1. A sample /boot/grub/grub.conf file
# grub.conf generated by anaconda
#
# Note that you do not have to rerun grub after making changes to this file
# NOTICE: You have a /boot partition. This means that
# all kernel and initrd paths are relative to /boot/, eg.
# root (hd0,0)
# kernel /vmlinuz-version ro root=/dev/sda3
# initrd /initrd
#boot=/dev/sda
default=0
timeout=5
splashimage=(hd0,0)/grub/splash.xpm.gz
hiddenmenu
title Red Hat Enterprise Linux (2.6.32-54.el6.i686)
root (hd0,0)
kernel /boot/vmlinuz-2.6.32-54.el6.i686 root=/dev/sda3 ro crashkernel=128M
initrd /initramfs-2.6.32-54.el6.i686.img
Important: Make Sure the System Has Enough Memory
kdump crash recovery is
enabled, the minimum memory requirements increase by the amount of
memory reserved for it. This value is determined by a user, and defaults
to 128 MB, as lower values proved to be unreliable. For more
information on minimum memory requirements for Red Hat Enterprise Linux
6, refer to the Required minimums section of the Red Hat Enterprise Linux comparison chart.
24.1.3.2. Configuring the Target Type
vmcore file in the /var/crash/ directory of the local file system. To change this, open the /etc/kdump.conf configuration file in a text editor such as vi or nano, and edit the options as described below.
#path /var/crash
line, and replace the value with a desired directory path. Optionally,
if you wish to write the file to a different partition, follow the same
procedure with the #ext4 /dev/sda3 line as
well, and change both the file system type and the device (a device
name, a file system label, and UUID are all supported) accordingly. For
example:
ext3 /dev/sda4 path /usr/local/cores
#raw /dev/sda5 line, and replace the value with a desired device name. For example:
raw /dev/sdb1
#net my.server.com:/export/tmp line, and replace the value with a valid hostname and directory path. For example:
net penguin.example.com:/export/cores
#net user@my.server.com line, and replace the value with a valid username and hostname. For example:
net john@penguin.example.com
Important: Using the hpsa Driver for a Storage
hpsa driver, kdump
is unable to save the dump to a storage that uses this driver for HP
Smart Array Controllers. If this applies to your machine, it is advised
that you save the dump to a remote system using the NFS or SSH protocol
instead.
24.1.3.3. Configuring the Core Collector
vmcore dump file, kdump
allows you to specify an external application (that is, a core
collector) to compress the data, and optionally leave out all irrelevant
information. Currently, the only fully supported core collector is makedumpfile.
/etc/kdump.conf configuration file in a text editor such as vi or nano, remove the hash sign (“#”) from the beginning of the #core_collector makedumpfile -c --message-level 1 -d 31 line, and edit the command line options as described below.
-c parameter. For example:
core_collector makedumpfile -c
-d value parameter, where value is a sum of values of pages you want to omit as described in Table 24.1, “Supported filtering levels”. For example, to remove both zero and free pages, use the following:
core_collector makedumpfile -d 17 -c
makedumpfile for a complete list of available options.
Table 24.1. Supported filtering levels
| Option | Description |
|---|---|
1
| Zero pages |
2
| Cache pages |
4
| Cache private |
8
| User pages |
16
| Free pages |
24.1.3.4. Changing the Default Action
/sbin/init is run. To change this behavior, open the /etc/kdump.conf configuration file in a text editor such as vi or nano, remove the hash sign (“#”) from the beginning of the #default shell line, and replace the value with a desired action as described in Table 24.2, “Supported actions”. For example:
default halt
Table 24.2. Supported actions
| Option | Description |
|---|---|
reboot
| Reboot the system, losing the core in the process. |
halt
| After attempting to capture a core, halt the system no matter if it succeeded. |
poweroff
| Power off the system. |
shell
| Run the msh session from within the initramfs, allowing a user to record the core manually. |
24.1.3.5. Enabling the Service
kdump daemon at boot time, type the following at a shell prompt:
~]# chkconfig kdump on2, 3, 4, and 5. Similarly, typing chkconfig kdump off will disable it for all runlevels. To start the service in the current session, use the following command:
~]# service kdump start
No kdump initial ramdisk found. [WARNING]
Rebuilding /boot/initrd-2.6.32-54.el6.i686kdump.img
Starting kdump: [ OK ]24.1.4. Testing the Configuration
Caution: Be Careful When Using These Commands
kdump enabled, and make sure that the service is running (refer to Section 7.3, “Running the Services” for more information on how to run a service in Red Hat Enterprise Linux):
~]# service kdump status
Kdump is operational~]#echo 1 > /proc/sys/kernel/sysrq~]#echo c > /proc/sysrq-trigger
address-YYYY-MM-DD-HH:MM:SS/vmcore/var/crash/ by default).
Example 24.2. Listing a content of /var/crash/ after a crash
~]# tree --charset=ascii /var/crash
/var/crash
`-- 127.0.0.1-2010-08-25-08:45:02
`-- vmcore
1 directory, 1 file24.2. Analyzing the Core Dump
netdump, diskdump, xendump, or kdump. When started, it presents you with an interactive prompt very similar to the GNU Debugger (GDB).
Note: Make Sure You Have Relevant Packages Installed
vmcore dump file, you must have the crash and kernel-debuginfo packages installed. To do so, type the following at a shell prompt:
~]# yum install --enablerepo=rhel-debuginfo crash kernel-debuginfocrash /var/crash/timestamp/vmcore /usr/lib/debug/lib/modules/kernel/vmlinuxkernel version should be the same that was captured by kdump. To find out which kernel you are currently running, use the uname -r command.
Example 24.3. Running the crash utility
~]#crash /usr/lib/debug/lib/modules/2.6.32-69.el6.i686/vmlinux \/var/crash/127.0.0.1-2010-08-25-08:45:02/vmcorecrash 5.0.0-23.el6 Copyright (C) 2002-2010 Red Hat, Inc. Copyright (C) 2004, 2005, 2006 IBM Corporation Copyright (C) 1999-2006 Hewlett-Packard Co Copyright (C) 2005, 2006 Fujitsu Limited Copyright (C) 2006, 2007 VA Linux Systems Japan K.K. Copyright (C) 2005 NEC Corporation Copyright (C) 1999, 2002, 2007 Silicon Graphics, Inc. Copyright (C) 1999, 2000, 2001, 2002 Mission Critical Linux, Inc. This program is free software, covered by the GNU General Public License, and you are welcome to change it and/or distribute copies of it under certain conditions. Enter "help copying" to see the conditions. This program has absolutely no warranty. Enter "help warranty" for details. GNU gdb (GDB) 7.0 Copyright (C) 2009 Free Software Foundation, Inc. License GPLv3+: GNU GPL version 3 or later <http://gnu.org/licenses/gpl.html> This is free software: you are free to change and redistribute it. There is NO WARRANTY, to the extent permitted by law. Type "show copying" and "show warranty" for details. This GDB was configured as "i686-pc-linux-gnu"... KERNEL: /usr/lib/debug/lib/modules/2.6.32-69.el6.i686/vmlinux DUMPFILE: /var/crash/127.0.0.1-2010-08-25-08:45:02/vmcore [PARTIAL DUMP] CPUS: 4 DATE: Wed Aug 25 08:44:47 2010 UPTIME: 00:09:02 LOAD AVERAGE: 0.00, 0.01, 0.00 TASKS: 140 NODENAME: hp-dl320g5-02.lab.bos.redhat.com RELEASE: 2.6.32-69.el6.i686 VERSION: #1 SMP Tue Aug 24 10:31:45 EDT 2010 MACHINE: i686 (2394 Mhz) MEMORY: 8 GB PANIC: "Oops: 0002 [#1] SMP " (check log for details) PID: 5591 COMMAND: "bash" TASK: f196d560 [THREAD_INFO: ef4da000] CPU: 2 STATE: TASK_RUNNING (PANIC) crash>
exit.
24.2.1. Displaying the Message Buffer
log command at the interactive prompt.
Example 24.4. Displaying the kernel message buffer
crash> log
... several lines omitted ...
EIP: 0060:[<c068124f>] EFLAGS: 00010096 CPU: 2
EIP is at sysrq_handle_crash+0xf/0x20
EAX: 00000063 EBX: 00000063 ECX: c09e1c8c EDX: 00000000
ESI: c0a09ca0 EDI: 00000286 EBP: 00000000 ESP: ef4dbf24
DS: 007b ES: 007b FS: 00d8 GS: 00e0 SS: 0068
Process bash (pid: 5591, ti=ef4da000 task=f196d560 task.ti=ef4da000)
Stack:
c068146b c0960891 c0968653 00000003 00000000 00000002 efade5c0 c06814d0
<0> fffffffb c068150f b7776000 f2600c40 c0569ec4 ef4dbf9c 00000002 b7776000
<0> efade5c0 00000002 b7776000 c0569e60 c051de50 ef4dbf9c f196d560 ef4dbfb4
Call Trace:
[<c068146b>] ? __handle_sysrq+0xfb/0x160
[<c06814d0>] ? write_sysrq_trigger+0x0/0x50
[<c068150f>] ? write_sysrq_trigger+0x3f/0x50
[<c0569ec4>] ? proc_reg_write+0x64/0xa0
[<c0569e60>] ? proc_reg_write+0x0/0xa0
[<c051de50>] ? vfs_write+0xa0/0x190
[<c051e8d1>] ? sys_write+0x41/0x70
[<c0409adc>] ? syscall_call+0x7/0xb
Code: a0 c0 01 0f b6 41 03 19 d2 f7 d2 83 e2 03 83 e0 cf c1 e2 04 09 d0 88 41 03 f3 c3 90 c7 05 c8 1b 9e c0 01 00 00 00 0f ae f8 89 f6 <c6> 05 00 00 00 00 01 c3 89 f6 8d bc 27 00 00 00 00 8d 50 d0 83
EIP: [<c068124f>] sysrq_handle_crash+0xf/0x20 SS:ESP 0068:ef4dbf24
CR2: 0000000000000000help log for more information on the command usage.
24.2.2. Displaying a Backtrace
bt command at the interactive prompt. You can use bt pid to display the backtrace of the selected process.
Example 24.5. Displaying the kernel stack trace
crash> bt
PID: 5591 TASK: f196d560 CPU: 2 COMMAND: "bash"
#0 [ef4dbdcc] crash_kexec at c0494922
#1 [ef4dbe20] oops_end at c080e402
#2 [ef4dbe34] no_context at c043089d
#3 [ef4dbe58] bad_area at c0430b26
#4 [ef4dbe6c] do_page_fault at c080fb9b
#5 [ef4dbee4] error_code (via page_fault) at c080d809
EAX: 00000063 EBX: 00000063 ECX: c09e1c8c EDX: 00000000 EBP: 00000000
DS: 007b ESI: c0a09ca0 ES: 007b EDI: 00000286 GS: 00e0
CS: 0060 EIP: c068124f ERR: ffffffff EFLAGS: 00010096
#6 [ef4dbf18] sysrq_handle_crash at c068124f
#7 [ef4dbf24] __handle_sysrq at c0681469
#8 [ef4dbf48] write_sysrq_trigger at c068150a
#9 [ef4dbf54] proc_reg_write at c0569ec2
#10 [ef4dbf74] vfs_write at c051de4e
#11 [ef4dbf94] sys_write at c051e8cc
#12 [ef4dbfb0] system_call at c0409ad5
EAX: ffffffda EBX: 00000001 ECX: b7776000 EDX: 00000002
DS: 007b ESI: 00000002 ES: 007b EDI: b7776000
SS: 007b ESP: bfcb2088 EBP: bfcb20b4 GS: 0033
CS: 0073 EIP: 00edc416 ERR: 00000004 EFLAGS: 00000246help bt for more information on the command usage.
24.2.3. Displaying a Process Status
ps command at the interactive prompt. You can use ps pid to display the status of the selected process.
Example 24.6. Displaying status of processes in the system
crash> ps
PID PPID CPU TASK ST %MEM VSZ RSS COMM
> 0 0 0 c09dc560 RU 0.0 0 0 [swapper]
> 0 0 1 f7072030 RU 0.0 0 0 [swapper]
0 0 2 f70a3a90 RU 0.0 0 0 [swapper]
> 0 0 3 f70ac560 RU 0.0 0 0 [swapper]
1 0 1 f705ba90 IN 0.0 2828 1424 init
... several lines omitted ...
5566 1 1 f2592560 IN 0.0 12876 784 auditd
5567 1 2 ef427560 IN 0.0 12876 784 auditd
5587 5132 0 f196d030 IN 0.0 11064 3184 sshd
> 5591 5587 2 f196d560 RU 0.0 5084 1648 bashhelp ps for more information on the command usage.
24.2.4. Displaying Virtual Memory Information
vm command at the interactive prompt. You can use vm pid to display information on the selected process.
Example 24.7. Displaying virtual memory information of the current context
crash> vm
PID: 5591 TASK: f196d560 CPU: 2 COMMAND: "bash"
MM PGD RSS TOTAL_VM
f19b5900 ef9c6000 1648k 5084k
VMA START END FLAGS FILE
f1bb0310 242000 260000 8000875 /lib/ld-2.12.so
f26af0b8 260000 261000 8100871 /lib/ld-2.12.so
efbc275c 261000 262000 8100873 /lib/ld-2.12.so
efbc2a18 268000 3ed000 8000075 /lib/libc-2.12.so
efbc23d8 3ed000 3ee000 8000070 /lib/libc-2.12.so
efbc2888 3ee000 3f0000 8100071 /lib/libc-2.12.so
efbc2cd4 3f0000 3f1000 8100073 /lib/libc-2.12.so
efbc243c 3f1000 3f4000 100073
efbc28ec 3f6000 3f9000 8000075 /lib/libdl-2.12.so
efbc2568 3f9000 3fa000 8100071 /lib/libdl-2.12.so
efbc2f2c 3fa000 3fb000 8100073 /lib/libdl-2.12.so
f26af888 7e6000 7fc000 8000075 /lib/libtinfo.so.5.7
f26aff2c 7fc000 7ff000 8100073 /lib/libtinfo.so.5.7
efbc211c d83000 d8f000 8000075 /lib/libnss_files-2.12.so
efbc2504 d8f000 d90000 8100071 /lib/libnss_files-2.12.so
efbc2950 d90000 d91000 8100073 /lib/libnss_files-2.12.so
f26afe00 edc000 edd000 4040075
f1bb0a18 8047000 8118000 8001875 /bin/bash
f1bb01e4 8118000 811d000 8101873 /bin/bash
f1bb0c70 811d000 8122000 100073
f26afae0 9fd9000 9ffa000 100073
... several lines omitted ...help vm for more information on the command usage.
24.2.5. Displaying Open Files
files command at the interactive prompt. You can use files pid to display files opened by the selected process.
Example 24.8. Displaying information about open files of the current context
crash> files
PID: 5591 TASK: f196d560 CPU: 2 COMMAND: "bash"
ROOT: / CWD: /root
FD FILE DENTRY INODE TYPE PATH
0 f734f640 eedc2c6c eecd6048 CHR /pts/0
1 efade5c0 eee14090 f00431d4 REG /proc/sysrq-trigger
2 f734f640 eedc2c6c eecd6048 CHR /pts/0
10 f734f640 eedc2c6c eecd6048 CHR /pts/0
255 f734f640 eedc2c6c eecd6048 CHR /pts/0help files for more information on the command usage.
24.3. Additional Resources
24.3.1. Installed Documentation
man kdump.conf- The manual page for the
/etc/kdump.confconfiguration file containing the full documentation of available options. man makedumpfile- The manual page for the
makedumpfilecore collector containing the full documentation on its usage. man kexec- The manual page for
kexeccontaining the full documentation on its usage. man crash- The manual page for the crash utility containing the full documentation on its usage.
/usr/share/doc/kexec-tools-version/kexec-kdump-howto.txt- An overview of the
kdumpandkexecinstallation and usage.
24.3.2. Useful Websites
- https://access.redhat.com/kb/docs/DOC-6039
- The Red Hat Knowledgebase article about the
kexecandkdumpconfiguration. - http://people.redhat.com/anderson/
- The crash utility homepage.
Revision History
| Revision History | |||
|---|---|---|---|
| Revision 2 | Tue Nov 09 2010 | ||
| |||
| Revision 1 | Mon Nov 16 2009 | ||
| |||
Index
Symbols
- .fetchmailrc , Fetchmail Configuration Options
- server options, Server Options
- user options, User Options
- .htaccess, Common httpd.conf Directives
- (see also Apache HTTP Server)
- .htpasswd, Common httpd.conf Directives
- (see also Apache HTTP Server)
- .procmailrc , Procmail Configuration
- /dev/shm , File Systems
- /etc/named.conf (see BIND)
- /etc/sysconfig/ directory (see sysconfig directory)
- /etc/sysconfig/dhcpd , Starting and Stopping the Server
- /proc/ directory, Installed Documentation (see proc file system)
- /var/spool/anacron , Configuring Anacron Jobs
- /var/spool/cron , Configuring Cron Jobs
A
- Access Control
- configuring in SSSD, Configuring Access Control
- in SSSD, rules, The Simple Access Provider
- adding
- group, Command Line Configuration
- user, Command Line Configuration
- anacron, Cron and Anacron
- anacron configuration file, Configuring Anacron Jobs
- user-defined tasks, Configuring Anacron Jobs
- anacrontab , Configuring Anacron Jobs
- Apache HTTP Server
- additional resources
- installed documentation, Installed Documentation
- useful websites, Useful Websites
- checking configuration, Editing the Configuration Files
- checking status, Checking the Service Status
- directives
- <Directory>, Common httpd.conf Directives
- <IfDefine>, Common httpd.conf Directives
- <IfModule>, Common httpd.conf Directives
- <Location>, Common httpd.conf Directives
- <Proxy>, Common httpd.conf Directives
- <VirtualHost>, Common httpd.conf Directives
- AccessFileName, Common httpd.conf Directives
- Action, Common httpd.conf Directives
- AddDescription, Common httpd.conf Directives
- AddEncoding, Common httpd.conf Directives
- AddHandler, Common httpd.conf Directives
- AddIcon, Common httpd.conf Directives
- AddIconByEncoding, Common httpd.conf Directives
- AddIconByType, Common httpd.conf Directives
- AddLanguage, Common httpd.conf Directives
- AddType, Common httpd.conf Directives
- Alias, Common httpd.conf Directives
- Allow, Common httpd.conf Directives
- AllowOverride, Common httpd.conf Directives
- BrowserMatch, Common httpd.conf Directives
- CacheDefaultExpire, Common httpd.conf Directives
- CacheDisable, Common httpd.conf Directives
- CacheEnable, Common httpd.conf Directives
- CacheLastModifiedFactor, Common httpd.conf Directives
- CacheMaxExpire, Common httpd.conf Directives
- CacheNegotiatedDocs, Common httpd.conf Directives
- CacheRoot, Common httpd.conf Directives
- CustomLog, Common httpd.conf Directives
- DefaultIcon, Common httpd.conf Directives
- DefaultType, Common httpd.conf Directives
- Deny, Common httpd.conf Directives
- DirectoryIndex, Common httpd.conf Directives
- DocumentRoot, Common httpd.conf Directives
- ErrorDocument, Common httpd.conf Directives
- ErrorLog, Common httpd.conf Directives
- ExtendedStatus, Common httpd.conf Directives
- Group, Common httpd.conf Directives
- HeaderName, Common httpd.conf Directives
- HostnameLookups, Common httpd.conf Directives
- Include, Common httpd.conf Directives
- IndexIgnore, Common httpd.conf Directives
- IndexOptions, Common httpd.conf Directives
- KeepAlive, Common httpd.conf Directives
- KeepAliveTimeout, Common httpd.conf Directives
- LanguagePriority, Common httpd.conf Directives
- Listen, Common httpd.conf Directives
- LoadModule, Common httpd.conf Directives
- LogFormat, Common httpd.conf Directives
- LogLevel, Common httpd.conf Directives
- MaxClients, Common Multi-Processing Module Directives
- MaxKeepAliveRequests, Common httpd.conf Directives
- MaxSpareServers, Common Multi-Processing Module Directives
- MaxSpareThreads, Common Multi-Processing Module Directives
- MinSpareServers, Common Multi-Processing Module Directives
- MinSpareThreads, Common Multi-Processing Module Directives
- NameVirtualHost, Common httpd.conf Directives
- Options, Common httpd.conf Directives
- Order, Common httpd.conf Directives
- PidFile, Common httpd.conf Directives
- ProxyRequests, Common httpd.conf Directives
- ReadmeName, Common httpd.conf Directives
- Redirect, Common httpd.conf Directives
- ScriptAlias, Common httpd.conf Directives
- ServerAdmin, Common httpd.conf Directives
- ServerName, Common httpd.conf Directives
- ServerRoot, Common httpd.conf Directives
- ServerSignature, Common httpd.conf Directives
- ServerTokens, Common httpd.conf Directives
- SetEnvIf, Common ssl.conf Directives
- StartServers, Common Multi-Processing Module Directives
- SuexecUserGroup, Common httpd.conf Directives
- ThreadsPerChild, Common Multi-Processing Module Directives
- Timeout, Common httpd.conf Directives
- TypesConfig, Common httpd.conf Directives
- UseCanonicalName, Common httpd.conf Directives
- User, Common httpd.conf Directives
- UserDir, Common httpd.conf Directives
- directories
- /etc/httpd/, Common httpd.conf Directives
- /etc/httpd/conf.d/, Editing the Configuration Files, Common httpd.conf Directives
- /usr/lib/httpd/modules/, Common httpd.conf Directives, Working with Modules
- /usr/lib64/httpd/modules/, Common httpd.conf Directives, Working with Modules
- /var/cache/mod_proxy/, Common httpd.conf Directives
- /var/www/cgi-bin/, Common httpd.conf Directives
- /var/www/html/, Common httpd.conf Directives
- /var/www/icons/, Common httpd.conf Directives
- ~/public_html/, Common httpd.conf Directives
- files
- .htaccess, Common httpd.conf Directives
- .htpasswd, Common httpd.conf Directives
- /etc/httpd/conf.d/ssl.conf, Common ssl.conf Directives, Enabling the mod_ssl Module
- /etc/httpd/conf/httpd.conf, Editing the Configuration Files, Common httpd.conf Directives, Common Multi-Processing Module Directives
- /etc/httpd/logs/access_log, Common httpd.conf Directives
- /etc/httpd/logs/error_log, Common httpd.conf Directives
- /etc/httpd/run/httpd.pid, Common httpd.conf Directives
- /etc/mime.types, Common httpd.conf Directives
- modules
- developing, Writing a Module
- loading, Loading a Module
- mod_asis, Notable Changes
- mod_cache, New Features
- mod_cern_meta, Notable Changes
- mod_disk_cache, New Features
- mod_ext_filter, Notable Changes
- mod_proxy_balancer, New Features
- mod_rewrite, Common httpd.conf Directives
- mod_ssl, Setting Up an SSL Server
- mod_userdir, Updating the Configuration
- restarting, Restarting the Service
- SSL server
- certificate, An Overview of Certificates and Security, Using an Existing Key and Certificate, Generating a New Key and Certificate
- certificate authority, An Overview of Certificates and Security
- private key, An Overview of Certificates and Security, Using an Existing Key and Certificate, Generating a New Key and Certificate
- public key, An Overview of Certificates and Security
- starting, Starting the Service
- stopping, Stopping the Service
- version 2.2
- changes, Notable Changes
- features, New Features
- updating from version 2.0, Updating the Configuration
- virtual host, Setting Up Virtual Hosts
- at , At and Batch
- additional resources, Additional Resources
- authconfig (see Authentication Configuration Tool )
- commands , Command Line Version
- authentication
- Authentication Configuration Tool , The Authentication Configuration Tool
- using fingerprint support , Advanced Options
- using smart card authentication , Advanced Options
- Authentication Configuration Tool
- and Kerberos authentication , Identity & Authentication
- and LDAP , Identity & Authentication
- and NIS , Identity & Authentication
- and NIS authentication , Identity & Authentication
- and Winbind , Identity & Authentication
- and Winbind authentication , Identity & Authentication
- authoritative nameserver (see BIND)
- Automated Tasks, Automated Tasks
B
- batch , At and Batch
- additional resources, Additional Resources
- Berkeley Internet Name Domain (see BIND)
- BIND
- additional resources
- installed documentation, Installed Documentation
- related books, Related Books
- useful websites, Useful Websites
- common mistakes, Common Mistakes to Avoid
- configuration
- acl statement, Common Statement Types
- comment tags, Comment Tags
- controls statement, Other Statement Types
- include statement, Common Statement Types
- key statement, Other Statement Types
- logging statement, Other Statement Types
- options statement, Common Statement Types
- server statement, Other Statement Types
- trusted-keys statement, Other Statement Types
- view statement, Other Statement Types
- zone statement, Common Statement Types
- directories
- /etc/named/, Configuring the named Service
- /var/named/, Editing Zone Files
- /var/named/data/, Editing Zone Files
- /var/named/dynamic/, Editing Zone Files
- /var/named/slaves/, Editing Zone Files
- features
- Automatic Zone Transfer (AXFR), Incremental Zone Transfers (IXFR)
- DNS Security Extensions (DNSSEC), DNS Security Extensions (DNSSEC)
- Incremental Zone Transfer (IXFR), Incremental Zone Transfers (IXFR)
- Internet Protocol version 6 (IPv6), Internet Protocol version 6 (IPv6)
- multiple views, Multiple Views
- Transaction SIGnature (TSIG), Transaction SIGnatures (TSIG)
- files
- /etc/named.conf, Configuring the named Service, Configuring the Utility
- /etc/rndc.conf, Configuring the Utility
- /etc/rndc.key, Configuring the Utility
- resource record, Nameserver Zones
- types
- authoritative nameserver, Nameserver Types
- primary (master) nameserver, Nameserver Zones, Nameserver Types
- recursive nameserver, Nameserver Types
- secondary (slave) nameserver, Nameserver Zones, Nameserver Types
- utilities
- zones
- $INCLUDE directive, Common Directives
- $ORIGIN directive, Common Directives
- $TTL directive, Common Directives
- A (Address) resource record, Common Resource Records
- CNAME (Canonical Name) resource record, Common Resource Records
- comment tags, Comment Tags
- description, Nameserver Zones
- example usage, A Simple Zone File, A Reverse Name Resolution Zone File
- MX (Mail Exchange) resource record, Common Resource Records
- NS (Nameserver) resource record, Common Resource Records
- PTR (Pointer) resource record, Common Resource Records
- SOA (Start of Authority) resource record, Common Resource Records
- block devices, /proc/devices
- (see also /proc/devices )
- definition of, /proc/devices
- bonding (see channel bonding)
- boot loader
- verifying, Verifying the Boot Loader
- boot media, Preparing to Upgrade
C
- ch-email .fetchmailrc
- global options, Global Options
- chage command
- forcing password expiration with, Command Line Configuration
- channel bonding
- configuration, Using Channel Bonding
- description, Using Channel Bonding
- interface
- configuration of, Channel Bonding Interfaces
- parameters to bonded interfaces, Bonding Module Directives
- channel bonding interface (see kernel module)
- character devices, /proc/devices
- (see also /proc/devices )
- definition of, /proc/devices
- chkconfig (see services configuration)
- Configuration File Changes, Preserving Configuration File Changes
- crash
- analyzing the dump
- message buffer, Displaying the Message Buffer
- open files, Displaying Open Files
- processes, Displaying a Process Status
- stack trace, Displaying a Backtrace
- virtual memory, Displaying Virtual Memory Information
- opening the dump image, Analyzing the Core Dump
- system requirements, Analyzing the Core Dump
- Cron, Automated Tasks
- cron , Cron and Anacron
- additional resources, Additional Resources
- cron configuration file, Configuring Cron Jobs
- user-defined tasks, Configuring Cron Jobs
- crontab , Configuring Cron Jobs
D
- date (see date configuration)
- date configuration
- date , Date and Time Setup
- system-config-date , Date and Time Properties
- deleting cache files
- in SSSD, Support for Multiple Domains
- Denial of Service attack, /proc/sys/net/
- (see also /proc/sys/net/ directory)
- definition of, /proc/sys/net/
- df , File Systems
- DHCP, Dynamic Host Configuration Protocol (DHCP)
- additional resources, Additional Resources
- client configuration, Configuring a DHCP Client
- command line options, Starting and Stopping the Server
- connecting to, Configuring a DHCP Client
- dhcpd.conf, Configuration File
- dhcpd.leases , Starting and Stopping the Server
- dhcpd6.conf, DHCP for IPv6 (DHCPv6)
- DHCPv6, DHCP for IPv6 (DHCPv6)
- dhcrelay , DHCP Relay Agent
- global parameters, Configuration File
- group, Configuration File
- options, Configuration File
- reasons for using, Why Use DHCP?
- Relay Agent, DHCP Relay Agent
- server configuration, Configuring a DHCP Server
- shared-network , Configuration File
- starting the server, Starting and Stopping the Server
- stopping the server, Starting and Stopping the Server
- subnet, Configuration File
- dhcpd.conf, Configuration File
- dhcpd.leases, Starting and Stopping the Server
- dhcrelay , DHCP Relay Agent
- dig (see BIND)
- DNS
- definition, The BIND DNS Server
- (see also BIND)
- documentation
- finding installed, Practical and Common Examples of RPM Usage
- DoS attack (see Denial of Service attack)
- drivers (see kernel module)
- DSA keys
- generating, Generating Key Pairs
- du , File Systems
- Dynamic Host Configuration Protocol (see DHCP)
E
- additional resources, Additional Resources
- installed documentation, Installed Documentation
- related books, Related Books
- useful websites, Useful Websites
- Fetchmail, Fetchmail
- history of, Email
- mail server
- Dovecot, Dovecot
- Postfix, Postfix
- Procmail, Mail Delivery Agents
- program classifications, Email Program Classifications
- protocols, Email Protocols
- security, Securing Communication
- clients, Secure Email Clients
- servers, Securing Email Client Communications
- Sendmail, Sendmail
- spam
- filtering out, Spam Filters
- types
- Mail Delivery Agent, Mail Delivery Agent
- Mail Transport Agent, Mail Transport Agent
- Mail User Agent, Mail User Agent
- epoch, /proc/stat
- (see also /proc/stat )
- definition of, /proc/stat
- Ethernet (see network)
- exec-shield
- enabling, /proc/sys/kernel/
- introducing, /proc/sys/kernel/
- execution domains, /proc/execdomains
- (see also /proc/execdomains )
- definition of, /proc/execdomains
- expiration of password, forcing, Command Line Configuration
- extra packages for Enterprise Linux (EPEL)
- installable packages, Finding RPM Packages
F
- feedback
- contact information for this manual, We Need Feedback!
- Fetchmail, Fetchmail
- additional resources, Additional Resources
- command options, Fetchmail Command Options
- informational, Informational or Debugging Options
- special, Special Options
- configuration options, Fetchmail Configuration Options
- global options, Global Options
- server options, Server Options
- user options, User Options
- file system
- virtual (see proc file system)
- file systems, File Systems
- files, proc file system
- changing, Changing Virtual Files, Using the sysctl Command
- viewing, Viewing Virtual Files, Using the sysctl Command
- FQDN (see fully qualified domain name)
- frame buffer device, /proc/fb
- (see also /proc/fb )
- free , Memory Usage
- fully qualified domain name, Nameserver Zones
G
- GNOME System Monitor , System Processes
- gnome-system-log (see Log File Viewer )
- gnome-system-monitor , System Processes
- GnuPG
- checking RPM package signatures, Checking a Package's Signature
- group confi/sbin/nologinguration
- adding groups, Adding a New Group
- group configuration
- filtering list of groups, User and Group Configuration
- groupadd , Command Line Configuration
- modify users in groups, Modifying Group Properties
- modifying group properties, Modifying Group Properties
- viewing list of groups, User and Group Configuration
- groups (see group configuration)
- additional resources, Additional Resources
- installed documentation, Installed Documentation
- GID, Users and Groups
- introducing, Users and Groups
- shared directories, Group Directories
- standard, Standard Groups
- tools for management of
- groupadd , User and Group Management Tools, User Private Groups
- system-config-users , User Private Groups
- User Manager , User and Group Management Tools
- user private, User Private Groups
- GRUB boot loader
- configuration file, Configuring the GRUB Boot Loader
- configuring, Configuring the GRUB Boot Loader
H
- hardware
- viewing, Hardware
- Hardware Browser , Hardware
- HTTP server (see Apache HTTP Server)
- httpd (see Apache HTTP Server)
- hugepages
- configuration of, /proc/sys/vm/
- hwbrowser , Hardware
I
- ifdown , Interface Control Scripts
- ifup , Interface Control Scripts
- information
- about your system, Gathering System Information
- initial RAM disk image
- verifying, Verifying the Initial RAM Disk Image
- IBM eServer System i, Verifying the Initial RAM Disk Image
- initial RPM repositories
- installable packages, Finding RPM Packages
- insmod , Loading a Module
- (see also kernel module)
- installing package groups
- installing package groups with PackageKit, Installing and Removing Package Groups
- installing the kernel, Manually Upgrading the Kernel
- introduction, Introduction
K
- kdump
- additional resources
- installed documents, Installed Documentation
- manual pages, Installed Documentation
- websites, Useful Websites
- analyzing the dump (see crash)
- configuring the service
- default action, The Expert Settings Tab, Changing the Default Action
- dump image compression, The Expert Settings Tab, Configuring the Core Collector
- filtering level, The Filtering Settings Tab, Configuring the Core Collector
- initial RAM disk, The Expert Settings Tab, Configuring the Memory Usage
- kernel image, The Expert Settings Tab, Configuring the Memory Usage
- kernel options, The Expert Settings Tab, Configuring the Memory Usage
- memory usage, Configuring the Memory Usage, The Basic Settings Tab, Configuring the Memory Usage
- target location, The Target Settings Tab, Configuring the Target Type
- enabling the service, Enabling the Service, Enabling the Service, Enabling the Service
- known issues
- hpsa driver, The Target Settings Tab, Configuring the Target Type
- running the service, Enabling the Service
- system requirements, Configuring the kdump Service
- testing the configuration, Testing the Configuration
- kernel
- downloading, Downloading the Upgraded Kernel
- installing kernel packages, Manually Upgrading the Kernel
- kernel packages, Overview of Kernel Packages
- package, Manually Upgrading the Kernel
- performing kernel upgrade, Performing the Upgrade
- RPM package, Manually Upgrading the Kernel
- upgrade kernel available, Downloading the Upgraded Kernel
- Security Errata, Downloading the Upgraded Kernel
- via Red Hat network, Downloading the Upgraded Kernel
- upgrading
- preparing, Preparing to Upgrade
- working boot media, Preparing to Upgrade
- upgrading the kernel, Manually Upgrading the Kernel
- Kernel Dump Configuration (see kdump)
- kernel module
- bonding module, Using Channel Bonding
- description, Using Channel Bonding
- parameters to bonded interfaces, Bonding Module Directives
- definition, Working with Kernel Modules
- directories
- /etc/sysconfig/modules/ , Persistent Module Loading
- /lib/modules/<kernel_version>/kernel/drivers/ , Loading a Module
- Ethernet module
- supporting multiple cards, Using Multiple Ethernet Cards
- files
- /proc/modules , Listing Currently-Loaded Modules
- listing
- currently loaded modules, Listing Currently-Loaded Modules
- module information, Displaying Information About a Module
- loading
- at the boot time, Persistent Module Loading
- for the current session, Loading a Module
- module parameters
- bonding module parameters, Bonding Module Directives
- supplying, Setting Module Parameters
- unloading, Unloading a Module
- utilities
- insmod , Loading a Module
- lsmod , Listing Currently-Loaded Modules
- modinfo , Displaying Information About a Module
- modprobe , Loading a Module, Unloading a Module
- rmmod , Unloading a Module
- kernel package
- kernel
- for single,multicore and multiprocessor systems, Overview of Kernel Packages
- kernel-devel
- kernel headers and makefiles, Overview of Kernel Packages
- kernel-doc
- documentation files, Overview of Kernel Packages
- kernel-firmware
- firmware files, Overview of Kernel Packages
- kernel-headers
- C header files files, Overview of Kernel Packages
- perf
- firmware files, Overview of Kernel Packages
- kernel upgrading
- preparing, Preparing to Upgrade
- keyboard configuration, Keyboard Configuration
- Keyboard Indicator applet, Adding the Keyboard Layout Indicator
- Keyboard Preferences utility, Changing the Keyboard Layout
- layout, Changing the Keyboard Layout
- typing break, Setting Up a Typing Break
- Keyboard Indicator (see keyboard configuration)
- Keyboard Preferences (see keyboard configuration)
L
- Log File Viewer
- filtering, Viewing Log Files
- monitoring, Monitoring Log Files
- searching, Viewing Log Files
- log files, Log Files
- (see also Log Viewer )
- additional resources
- installed documentation, Installed Documentation
- useful websites, Useful Websites
- description, Log Files
- locating, Locating Log Files
- monitoring, Monitoring Log Files
- rotating, Locating Log Files
- rsyslod daemon , Log Files
- viewing, Viewing Log Files
- Log Viewer
- refresh rate, Viewing Log Files
- logrotate , Locating Log Files
- lsmod , Listing Currently-Loaded Modules
- (see also kernel module)
- lspci , /proc/bus/pci , Hardware
M
- Mail Delivery Agent (see email)
- Mail Transport Agent (see email) (see MTA)
- Mail Transport Agent Switcher , Mail Transport Agent (MTA) Configuration
- Mail User Agent, Mail Transport Agent (MTA) Configuration (see email)
- MDA (see Mail Delivery Agent)
- memory usage, Memory Usage
- modinfo , Displaying Information About a Module
- (see also kernel module)
- modprobe , Loading a Module, Unloading a Module
- (see also kernel module)
- module (see kernel module)
- module parameters (see kernel module)
- MTA (see Mail Transport Agent)
- setting default, Mail Transport Agent (MTA) Configuration
- switching with Mail Transport Agent Switcher , Mail Transport Agent (MTA) Configuration
- MUA, Mail Transport Agent (MTA) Configuration (see Mail User Agent)
- Multihomed DHCP
- host configuration, Host Configuration
- server configuration, Configuring a Multihomed DHCP Server
- multiple domains
- specifying in SSSD, Support for Multiple Domains
N
- named (see BIND)
- nameserver (see DNS)
- network
- additional resources, Additional Resources
- commands
- /sbin/ifdown , Interface Control Scripts
- /sbin/ifup , Interface Control Scripts
- /sbin/service network , Interface Control Scripts
- configuration, Interface Configuration Files
- configuration files, Network Configuration Files
- functions, Network Function Files
- interface configuration files, Interface Configuration Files
- interfaces
- alias, Alias and Clone Files
- channel bonding, Channel Bonding Interfaces
- clone, Alias and Clone Files
- dialup, Dialup Interfaces
- Ethernet, Ethernet Interfaces
- scripts, Network Interfaces
- Network Time Protocol (see NTP)
- NIC
- binding into single channel, Using Channel Bonding
- NTP
- ntpd (see NTP)
- ntpdate (see NTP)
- ntsysv (see services configuration)
O
- OpenSSH, OpenSSH, Main Features
- (see also SSH)
- additional resources, Additional Resources
- client, OpenSSH Clients
- scp , Using the scp Utility
- sftp , Using the sftp Utility
- ssh , Using the ssh Utility
- DSA keys
- generating, Generating Key Pairs
- RSA keys
- generating, Generating Key Pairs
- RSA Version 1 keys
- generating, Generating Key Pairs
- server, Starting an OpenSSH Server
- starting, Starting an OpenSSH Server
- stopping, Starting an OpenSSH Server
- ssh-add , Configuring ssh-agent
- ssh-agent , Configuring ssh-agent
- ssh-keygen
- DSA, Generating Key Pairs
- RSA, Generating Key Pairs
- RSA Version 1, Generating Key Pairs
- using key-based authentication, Using a Key-Based Authentication
- OpenSSL
- additional resources, Additional Resources
- SSL (see SSL)
- TLS (see TLS)
- OS/400 boot loader
- configuration file, Configuring the OS/400® Boot Loader
- configuring, Configuring the OS/400® Boot Loader
P
- package
- kernel RPM, Manually Upgrading the Kernel
- PackageKit, PackageKit
- adding and removing, Using Add/Remove Software
- architecture, PackageKit Architecture
- installing and removing package groups, Installing and Removing Package Groups
- installing packages , PackageKit
- managing packages , PackageKit
- PolicyKit
- authentication, Updating Packages with Software Update
- uninstalling packages , PackageKit
- updating packages , PackageKit
- viewing packages , PackageKit
- viewing transaction log, Viewing the Transaction Log
- packages
- adding and removing with PackageKit, Using Add/Remove Software
- dependencies, Unresolved Dependency
- determining file ownership with, Practical and Common Examples of RPM Usage
- displaying packages
- displaying packages with Yum, Searching, Listing and Displaying Package Information
- extra packages for Enterprise Linux (EPEL), Finding RPM Packages
- filtering with PackageKit, Finding Packages with Filters
- Development, Finding Packages with Filters
- Free, Finding Packages with Filters
- Graphical, Finding Packages with Filters
- hide subpackages, Finding Packages with Filters
- installed, Finding Packages with Filters
- no filter, Finding Packages with Filters
- only available, Finding Packages with Filters
- only development, Finding Packages with Filters
- only end user files, Finding Packages with Filters
- only installed, Finding Packages with Filters
- only native packages, Finding Packages with Filters
- only newest items, Finding Packages with Filters
- filtering with PackageKit for packages, Finding Packages with Filters
- finding deleted files from, Practical and Common Examples of RPM Usage
- finding RPM packages, Finding RPM Packages
- initial RPM repositories, Finding RPM Packages
- installing a package group with Yum, Installing
- installing and removing package groups, Installing and Removing Package Groups
- installing packages with PackageKit, PackageKit, Installing and Removing Packages (and Dependencies)
- dependencies, Installing and Removing Packages (and Dependencies)
- installing RPM, Installing and Upgrading
- installing with Yum, Installing
- iRed Hat Enterprise Linux installation media, Finding RPM Packages
- kernel
- for single,multicore and multiprocessor systems, Overview of Kernel Packages
- kernel-devel
- kernel headers and makefiles, Overview of Kernel Packages
- kernel-doc
- documentation files, Overview of Kernel Packages
- kernel-firmware
- firmware files, Overview of Kernel Packages
- kernel-headers
- C header files files, Overview of Kernel Packages
- listing packages with Yum, Searching, Listing and Displaying Package Information
- Glob expressions, Searching, Listing and Displaying Package Information
- yum grouplist, Searching, Listing and Displaying Package Information
- yum list all, Searching, Listing and Displaying Package Information
- yum list available, Searching, Listing and Displaying Package Information
- yum list installed, Searching, Listing and Displaying Package Information
- yum repolist, Searching, Listing and Displaying Package Information
- yum search, Searching, Listing and Displaying Package Information
- locating documentation for, Practical and Common Examples of RPM Usage
- managing packages with PackageKit, PackageKit
- obtaining list of files, Practical and Common Examples of RPM Usage
- packages and package groups, Packages and Package Groups
- perf
- firmware files, Overview of Kernel Packages
- querying uninstalled, Practical and Common Examples of RPM Usage
- removing, Uninstalling
- removing package groups with Yum, Removing
- removing packages with PackageKit, Installing and Removing Packages (and Dependencies)
- RPM, RPM
- already installed, Package Already Installed
- configuration file changes, Configuration File Changes
- conflict, Conflicting Files
- failed dependancies, Unresolved Dependency
- freshening, Freshening
- prisitne sources, RPM Design Goals
- querying, Querying
- removing, Uninstalling
- source and binary packages, RPM
- tips, Practical and Common Examples of RPM Usage
- uninstalling, Uninstalling
- verifying, Verifying
- searching for packages with Yum
- searching packages with Yum, Searching, Listing and Displaying Package Information
- setting packages with PackageKit
- checking interval, Updating Packages with Software Update
- uninstalling packages with PackageKit, PackageKit
- uninstalling packages with Yum, Removing
- yum remove package_name, Removing
- updating currently installed packages
- available updates, Updating Packages with Software Update
- updating packages with PackageKit, PackageKit
- PolicyKit, Updating Packages with Software Update
- Software Update, Updating Packages with Software Update
- upgrading RPM, Installing and Upgrading
- viewing packages with PackageKit, PackageKit
- viewing transaction log, Viewing the Transaction Log
- viewing Yum repositories with PackageKit, Refreshing Software Sources (Yum Repositories)
- Yum insead of RPM, RPM
- password
- aging, Command Line Configuration
- expire, Command Line Configuration
- passwords
- shadow, Shadow Passwords
- PCI devices
- listing, Hardware
- PolicyKit, Updating Packages with Software Update
- Postfix, Postfix
- default installation, The Default Postfix Installation
- postfix, Mail Transport Agent (MTA) Configuration
- primary nameserver (see BIND)
- proc file system
- /proc/buddyinfo , /proc/buddyinfo
- /proc/bus/ directory, /proc/bus/
- /proc/bus/pci
- viewing using lspci , /proc/bus/pci
- /proc/cmdline , /proc/cmdline
- /proc/cpuinfo , /proc/cpuinfo
- /proc/crypto , /proc/crypto
- /proc/devices
- block devices, /proc/devices
- character devices, /proc/devices
- /proc/dma , /proc/dma
- /proc/driver/ directory, /proc/driver/
- /proc/execdomains , /proc/execdomains
- /proc/fb , /proc/fb
- /proc/filesystems , /proc/filesystems
- /proc/fs/ directory, /proc/fs
- /proc/interrupts , /proc/interrupts
- /proc/iomem , /proc/iomem
- /proc/ioports , /proc/ioports
- /proc/irq/ directory, /proc/irq/
- /proc/kcore , /proc/kcore
- /proc/kmsg , /proc/kmsg
- /proc/loadavg , /proc/loadavg
- /proc/locks , /proc/locks
- /proc/mdstat , /proc/mdstat
- /proc/meminfo , /proc/meminfo
- /proc/misc , /proc/misc
- /proc/modules , /proc/modules
- /proc/mounts , /proc/mounts
- /proc/mtrr , /proc/mtrr
- /proc/net/ directory, /proc/net/
- /proc/partitions , /proc/partitions
- /proc/PID/ directory, /proc/PID/
- /proc/scsi/ directory, /proc/scsi/
- /proc/self/ directory, /proc/self/
- /proc/slabinfo , /proc/slabinfo
- /proc/stat , /proc/stat
- /proc/swaps , /proc/swaps
- /proc/sys/ directory, /proc/sys/ , Using the sysctl Command
- (see also sysctl )
- /proc/sys/dev/ directory, /proc/sys/dev/
- /proc/sys/fs/ directory, /proc/sys/fs/
- /proc/sys/kernel/ directory, /proc/sys/kernel/
- /proc/sys/kernel/exec-shield , /proc/sys/kernel/
- /proc/sys/kernel/sysrq (see system request key)
- /proc/sys/net/ directory, /proc/sys/net/
- /proc/sys/vm/ directory, /proc/sys/vm/
- /proc/sysrq-trigger , /proc/sysrq-trigger
- /proc/sysvipc/ directory, /proc/sysvipc/
- /proc/tty/ directory, /proc/tty/
- /proc/uptime , /proc/uptime
- /proc/version , /proc/version
- additional resources, References
- installed documentation, Installed Documentation
- useful websites, Useful Websites
- changing files within, Changing Virtual Files, /proc/sys/ , Using the sysctl Command
- files within, top-level, Top-level Files within the proc File System
- introduced, The proc File System
- process directories, Process Directories
- subdirectories within, Directories within /proc/
- viewing files within, Viewing Virtual Files
- processes, System Processes
- Procmail, Mail Delivery Agents
- additional resources, Additional Resources
- configuration, Procmail Configuration
- recipes, Procmail Recipes
- delivering, Delivering vs. Non-Delivering Recipes
- examples, Recipe Examples
- flags, Flags
- local lockfiles, Specifying a Local Lockfile
- non-delivering, Delivering vs. Non-Delivering Recipes
- SpamAssassin, Spam Filters
- special actions, Special Conditions and Actions
- special conditions, Special Conditions and Actions
- ps , System Processes
R
- RAM, Memory Usage
- rcp , Using the scp Utility
- recursive nameserver (see BIND)
- Red Hat Enterprise Linux installation media
- installable packages, Finding RPM Packages
- Red Hat RPM Guide , Related Books
- removing package groups
- removing package groups with PackageKit, Installing and Removing Package Groups
- resource record (see BIND)
- rmmod , Unloading a Module
- (see also kernel module)
- rndc (see BIND)
- root nameserver (see BIND)
- RPM, RPM
- additional resources, Additional Resources
- already installed, Package Already Installed
- basic modes, Using RPM
- book about, Related Books
- checking package signatures, Checking a Package's Signature
- configuration file changes, Configuration File Changes
- conf.rpmsave, Configuration File Changes
- conflicts, Conflicting Files
- dependencies, Unresolved Dependency
- design goals, RPM Design Goals
- powerful querying, RPM Design Goals
- system verification, RPM Design Goals
- upgradability, RPM Design Goals
- determining file ownership with, Practical and Common Examples of RPM Usage
- documentation with, Practical and Common Examples of RPM Usage
- failed dependancies, Unresolved Dependency
- file conflicts
- resolving, Conflicting Files
- file name, Installing and Upgrading
- finding deleted files with, Practical and Common Examples of RPM Usage
- finding RPM packages, Finding RPM Packages
- freshening, Freshening
- GnuPG, Checking a Package's Signature
- installing, Installing and Upgrading
- md5sum, Checking a Package's Signature
- querying, Querying
- querying for file list, Practical and Common Examples of RPM Usage
- querying uninstalled packages, Practical and Common Examples of RPM Usage
- tips, Practical and Common Examples of RPM Usage
- uninstalling, Uninstalling
- upgrading, Installing and Upgrading
- verifying, Verifying
- website, Useful Websites
- RPM Package Manager (see RPM)
- RSA keys
- generating, Generating Key Pairs
- RSA Version 1 keys
- generating, Generating Key Pairs
- rsyslog , Log Files
- runlevel (see services configuration)
S
- scp (see OpenSSH)
- secondary nameserver (see BIND)
- security plugin (see Security )
- Security-Related Packages
- updating security-related packages, Updating Security-Related Packages
- Sendmail, Sendmail
- additional resources, Additional Resources
- aliases, Masquerading
- common configuration changes, Common Sendmail Configuration Changes
- default installation, The Default Sendmail Installation
- LDAP and, Using Sendmail with LDAP
- limitations, Purpose and Limitations
- masquerading, Masquerading
- purpose, Purpose and Limitations
- spam, Stopping Spam
- with UUCP, Common Sendmail Configuration Changes
- sendmail, Mail Transport Agent (MTA) Configuration
- service (see services configuration)
- services configuration, Controlling Access to Services
- chkconfig , Using the chkconfig Utility
- ntsysv , Using the ntsysv Utility
- runlevel , Configuring the Default Runlevel
- service , Using the service Utility
- system-config-services , Using the Service Configuration Utility
- sftp (see OpenSSH)
- shadow passwords
- overview of, Shadow Passwords
- slab pools (see /proc/slabinfo )
- SpamAssassin
- using with Procmail, Spam Filters
- ssh (see OpenSSH)
- SSH protocol
- authentication, Authentication
- configuration files, Configuration Files
- system-wide configuration files, Configuration Files
- user-specific configuration files, Configuration Files
- connection sequence, Event Sequence of an SSH Connection
- features, Main Features
- insecure protocols, Requiring SSH for Remote Connections
- layers
- channels, Channels
- transport layer, Transport Layer
- port forwarding, Port Forwarding
- requiring for remote login, Requiring SSH for Remote Connections
- security risks, Why Use SSH?
- version 1, Protocol Versions
- version 2, Protocol Versions
- X11 forwarding, X11 Forwarding
- ssh-add , Configuring ssh-agent
- ssh-agent , Configuring ssh-agent
- SSL, Setting Up an SSL Server
- (see also Apache HTTP Server)
- SSL server (see Apache HTTP Server)
- SSSD
- Configuring a Microsoft Active Directory Domain for, Configuring a Microsoft Active Directory Domain
- Configuring a proxy domain for, Configuring a Proxy Domain
- Configuring an LDAP domain for, Configuring an LDAP Domain
- Selecting an LDAP schema for, Configuring an LDAP Domain
- Setting Up Kerberos authentication for, Setting Up Kerberos Authentication
- Specifying timeout values for, Configuring an LDAP Domain
- stunnel , Securing Email Client Communications
- sysconfig directory
- /etc/sysconfig/apm-scripts/ directory, Directories in the /etc/sysconfig/ Directory
- /etc/sysconfig/arpwatch , /etc/sysconfig/arpwatch
- /etc/sysconfig/authconfig , /etc/sysconfig/authconfig
- /etc/sysconfig/autofs , /etc/sysconfig/autofs
- /etc/sysconfig/cbq/ directory, Directories in the /etc/sysconfig/ Directory
- /etc/sysconfig/clock , /etc/sysconfig/clock
- /etc/sysconfig/dhcpd , /etc/sysconfig/dhcpd
- /etc/sysconfig/firstboot , /etc/sysconfig/firstboot
- /etc/sysconfig/init , /etc/sysconfig/init
- /etc/sysconfig/ip6tables-config , /etc/sysconfig/ip6tables-config
- /etc/sysconfig/keyboard , /etc/sysconfig/keyboard
- /etc/sysconfig/ldap , /etc/sysconfig/ldap
- /etc/sysconfig/named , /etc/sysconfig/named
- /etc/sysconfig/network , /etc/sysconfig/network
- /etc/sysconfig/network-scripts/ directory, Network Interfaces, Directories in the /etc/sysconfig/ Directory
- (see also network)
- /etc/sysconfig/networking/ directory, Directories in the /etc/sysconfig/ Directory
- /etc/sysconfig/ntpd , /etc/sysconfig/ntpd
- /etc/sysconfig/quagga , /etc/sysconfig/quagga
- /etc/sysconfig/radvd , /etc/sysconfig/radvd
- /etc/sysconfig/rhn/ directory, Directories in the /etc/sysconfig/ Directory
- /etc/sysconfig/samba , /etc/sysconfig/samba
- /etc/sysconfig/selinux , /etc/sysconfig/selinux
- /etc/sysconfig/sendmail , /etc/sysconfig/sendmail
- /etc/sysconfig/spamassassin , /etc/sysconfig/spamassassin
- /etc/sysconfig/squid , /etc/sysconfig/squid
- /etc/sysconfig/system-config-users , /etc/sysconfig/system-config-users
- /etc/sysconfig/vncservers , /etc/sysconfig/vncservers
- /etc/sysconfig/xinetd , /etc/sysconfig/xinetd
- additional information about, The sysconfig Directory
- additional resources, Additional Resources
- installed documentation, Installed Documentation
- directories in, Directories in the /etc/sysconfig/ Directory
- files found in, Files in the /etc/sysconfig/ Directory
- sysctl
- configuring with /etc/sysctl.conf , Using the sysctl Command
- controlling /proc/sys/ , Using the sysctl Command
- SysRq (see system request key)
- system information
- file systems, File Systems
- /dev/shm , File Systems
- gathering, Gathering System Information
- hardware, Hardware
- memory usage, Memory Usage
- processes, System Processes
- currently running, System Processes
- system request key
- enabling, /proc/sys/
- System Request Key
- definition of, /proc/sys/
- setting timing for, /proc/sys/kernel/
- system-config-authentication (see Authentication Configuration Tool )
- system-config-date (see time configuration, date configuration)
- system-config-kdump (see kdump)
- system-config-services (see services configuration)
- system-config-users (see user configuration and group configuration)
T
- time configuration
- date , Date and Time Setup
- synchronize with NTP server, Network Time Protocol Properties, Network Time Protocol Setup
- system-config-date , Date and Time Properties
- time zone configuration, Time Zone Properties
- TLB cache (see hugepages)
- TLS, Setting Up an SSL Server
- (see also Apache HTTP Server)
- tool
- Authentication Configuration Tool , The Authentication Configuration Tool
- top , System Processes
U
- updating currently installed packages
- available updates, Updating Packages with Software Update
- updating packages with PackageKit
- PolicyKit, Updating Packages with Software Update
- user configuration
- adding users, Adding a New User
- changing full name, Adding a New User
- changing home directory, Adding a New User
- changing login shell, Adding a New User
- changing password, Adding a New User
- command line configuration, Command Line Configuration
- passwd , Command Line Configuration
- useradd , Command Line Configuration
- filtering list of users, User and Group Configuration
- modify groups for a user, Adding a New User
- modifying users, Adding a New User
- password
- forcing expiration of, Command Line Configuration
- viewing list of users, User and Group Configuration
- User Manager (see user configuration)
- user private groups (see groups)
- and shared directories, Group Directories
- useradd command
- user account creation using, Command Line Configuration
- users (see user configuration)
- /etc/passwd , Standard Users
- additional resources, Additional Resources
- installed documentation, Installed Documentation
- introducing, Users and Groups
- standard, Standard Users
- tools for management of
- User Manager , User and Group Management Tools
- useradd , User and Group Management Tools
- UID, Users and Groups
V
- virtual file system (see proc file system)
- virtual files (see proc file system)
- virtual host (see Apache HTTP Server)
W
- web server (see Apache HTTP Server)
Y
- Yum
- Additional Resources, Additional Resources
- configuring plugins, Enabling, Configuring and Disabling Yum Plugins
- configuring Yum and Yum repositories, Configuring Yum and Yum Repositories
- disabling plugins, Enabling, Configuring and Disabling Yum Plugins
- displaying packages
- displaying packages with Yum, Searching, Listing and Displaying Package Information
- enabling plugins, Enabling, Configuring and Disabling Yum Plugins
- installing a package group with Yum, Installing
- installing with Yum, Installing
- listing packages with Yum, Searching, Listing and Displaying Package Information
- Glob expressions, Searching, Listing and Displaying Package Information
- yum grouplist, Searching, Listing and Displaying Package Information
- yum list, Searching, Listing and Displaying Package Information
- yum list all, Searching, Listing and Displaying Package Information
- yum list available, Searching, Listing and Displaying Package Information
- yum list installed, Searching, Listing and Displaying Package Information
- yum repolist, Searching, Listing and Displaying Package Information
- packages and package groups, Packages and Package Groups
- plugins
- PackageKit-yum-plugin, Plugin Descriptions
- rhnplugin, Plugin Descriptions
- yum-plugin-protect-packages, Plugin Descriptions
- yum-plugin-security, Plugin Descriptions
- yum-presto, Plugin Descriptions
- yum-rhn-plugin, Plugin Descriptions
- repository, Creating a Yum Repository
- searching for packages with Yum
- searching packages with Yum, Searching, Listing and Displaying Package Information
- setting [main] options, Setting [main] Options
- setting [repository] options, Setting [repository] Options
- uninstalling package groups with Yum, Removing
- uninstalling packages with Yum, Removing
- yum remove package_name, Removing
- variables, Using Yum Variables
- Yum plugins, Yum Plugins
- Yum repositories
- configuring Yum and Yum repositories, Configuring Yum and Yum Repositories
- Yum repositories
- viewing Yum repositories with PackageKit, Refreshing Software Sources (Yum Repositories)
- Yum Updates
- checking for updates, Checking For Updates
- updating a single package, Updating Packages
- updating all packages and dependencies, Updating Packages
- updating packages, Updating Packages
- updating security-related packages, Updating Security-Related Packages
aa - ab - af - ak - als - am - an - ang - ar - arc - as - ast - av - ay - az - ba - bar - bat_smg - bcl - be - be_x_old - bg - bh - bi - bm - bn - bo - bpy - br - bs - bug - bxr - ca - cbk_zam - cdo - ce - ceb - ch - cho - chr - chy - co - cr - crh - cs - csb - cu - cv - cy - da - de - diq - dsb - dv - dz - ee - el - eml - en - eo - es - et - eu - ext - fa - ff - fi - fiu_vro - fj - fo - fr - frp - fur - fy - ga - gan - gd - gl - glk - gn - got - gu - gv - ha - hak - haw - he - hi - hif - ho - hr - hsb - ht - hu - hy - hz - ia - id - ie - ig - ii - ik - ilo - io - is - it - iu - ja - jbo - jv - ka - kaa - kab - kg - ki - kj - kk - kl - km - kn - ko - kr - ks - ksh - ku - kv - kw - ky - la - lad - lb - lbe - lg - li - lij - lmo - ln - lo - lt - lv - map_bms - mdf - mg - mh - mi - mk - ml - mn - mo - mr - mt - mus - my - myv - mzn - na - nah - nap - nds - nds_nl - ne - new - ng - nl - nn - no - nov - nrm - nv - ny - oc - om - or - os - pa - pag - pam - pap - pdc - pi - pih - pl - pms - ps - pt - qu - quality - rm - rmy - rn - ro - roa_rup - roa_tara - ru - rw - sa - sah - sc - scn - sco - sd - se - sg - sh - si - simple - sk - sl - sm - sn - so - sr - srn - ss - st - stq - su - sv - sw - szl - ta - te - tet - tg - th - ti - tk - tl - tlh - tn - to - tpi - tr - ts - tt - tum - tw - ty - udm - ug - uk - ur - uz - ve - vec - vi - vls - vo - wa - war - wo - wuu - xal - xh - yi - yo - za - zea - zh - zh_classical - zh_min_nan - zh_yue - zu -
Static Wikipedia 2007 (no images)
aa - ab - af - ak - als - am - an - ang - ar - arc - as - ast - av - ay - az - ba - bar - bat_smg - bcl - be - be_x_old - bg - bh - bi - bm - bn - bo - bpy - br - bs - bug - bxr - ca - cbk_zam - cdo - ce - ceb - ch - cho - chr - chy - co - cr - crh - cs - csb - cu - cv - cy - da - de - diq - dsb - dv - dz - ee - el - eml - en - eo - es - et - eu - ext - fa - ff - fi - fiu_vro - fj - fo - fr - frp - fur - fy - ga - gan - gd - gl - glk - gn - got - gu - gv - ha - hak - haw - he - hi - hif - ho - hr - hsb - ht - hu - hy - hz - ia - id - ie - ig - ii - ik - ilo - io - is - it - iu - ja - jbo - jv - ka - kaa - kab - kg - ki - kj - kk - kl - km - kn - ko - kr - ks - ksh - ku - kv - kw - ky - la - lad - lb - lbe - lg - li - lij - lmo - ln - lo - lt - lv - map_bms - mdf - mg - mh - mi - mk - ml - mn - mo - mr - mt - mus - my - myv - mzn - na - nah - nap - nds - nds_nl - ne - new - ng - nl - nn - no - nov - nrm - nv - ny - oc - om - or - os - pa - pag - pam - pap - pdc - pi - pih - pl - pms - ps - pt - qu - quality - rm - rmy - rn - ro - roa_rup - roa_tara - ru - rw - sa - sah - sc - scn - sco - sd - se - sg - sh - si - simple - sk - sl - sm - sn - so - sr - srn - ss - st - stq - su - sv - sw - szl - ta - te - tet - tg - th - ti - tk - tl - tlh - tn - to - tpi - tr - ts - tt - tum - tw - ty - udm - ug - uk - ur - uz - ve - vec - vi - vls - vo - wa - war - wo - wuu - xal - xh - yi - yo - za - zea - zh - zh_classical - zh_min_nan - zh_yue - zu -
Static Wikipedia 2006 (no images)
aa - ab - af - ak - als - am - an - ang - ar - arc - as - ast - av - ay - az - ba - bar - bat_smg - bcl - be - be_x_old - bg - bh - bi - bm - bn - bo - bpy - br - bs - bug - bxr - ca - cbk_zam - cdo - ce - ceb - ch - cho - chr - chy - co - cr - crh - cs - csb - cu - cv - cy - da - de - diq - dsb - dv - dz - ee - el - eml - eo - es - et - eu - ext - fa - ff - fi - fiu_vro - fj - fo - fr - frp - fur - fy - ga - gan - gd - gl - glk - gn - got - gu - gv - ha - hak - haw - he - hi - hif - ho - hr - hsb - ht - hu - hy - hz - ia - id - ie - ig - ii - ik - ilo - io - is - it - iu - ja - jbo - jv - ka - kaa - kab - kg - ki - kj - kk - kl - km - kn - ko - kr - ks - ksh - ku - kv - kw - ky - la - lad - lb - lbe - lg - li - lij - lmo - ln - lo - lt - lv - map_bms - mdf - mg - mh - mi - mk - ml - mn - mo - mr - mt - mus - my - myv - mzn - na - nah - nap - nds - nds_nl - ne - new - ng - nl - nn - no - nov - nrm - nv - ny - oc - om - or - os - pa - pag - pam - pap - pdc - pi - pih - pl - pms - ps - pt - qu - quality - rm - rmy - rn - ro - roa_rup - roa_tara - ru - rw - sa - sah - sc - scn - sco - sd - se - sg - sh - si - simple - sk - sl - sm - sn - so - sr - srn - ss - st - stq - su - sv - sw - szl - ta - te - tet - tg - th - ti - tk - tl - tlh - tn - to - tpi - tr - ts - tt - tum - tw - ty - udm - ug - uk - ur - uz - ve - vec - vi - vls - vo - wa - war - wo - wuu - xal - xh - yi - yo - za - zea - zh - zh_classical - zh_min_nan - zh_yue - zu -
Sub-domains
CDRoms - Magnatune - Librivox - Liber Liber - Encyclopaedia Britannica - Project Gutenberg - Wikipedia 2008 - Wikipedia 2007 - Wikipedia 2006 -
Other Domains
https://www.classicistranieri.it - https://www.ebooksgratis.com - https://www.gutenbergaustralia.com - https://www.englishwikipedia.com - https://www.wikipediazim.com - https://www.wikisourcezim.com - https://www.projectgutenberg.net - https://www.projectgutenberg.es - https://www.radioascolto.com - https://www.debitoformtivo.it - https://www.wikipediaforschools.org - https://www.projectgutenbergzim.com
aa - ab - als - am - an - ang - ar - arc - as - bar - bat_smg - bi - bug - bxr - cho - co - cr - csb - cv - cy - eo - es - et - eu - fa - ff - fi - fiu_vro - fj - fo - frp - fur - fy - ga - gd - gl - glk - gn - got - gu - gv - ha - hak - haw - he - ho - hr - hsb - ht - hu - hy - hz - ia - id - ie - ig - ii - ik - ilo - io - is - it - iu - jbo - jv - ka - kab - kg - ki - kj - kk - kl - km - kn - ko - kr - ks - ksh - ku - kv - kw - ky - la - lad - lb - lbe - lg - li - lij - lmo - ln - lo - lt - lv - map_bms - mg - mh - mi - mk - ml - mn - mo - mr - ms - mt - mus - my - mzn - na - nah - nap - nds - nds_nl - ne - new - ng - nn -
Liber Liber 2023 -
Authors
abati
- abba
- abbate
- accademia_degli_intronati
- accati
- accetto
- acerbi
- adami
- agabiti
- agamennone
- aganoor
- agaraff
- agostini
- agraives
- agresti
- agrippa
- alamanni
- albergati_capacelli
- albert
- albertazzi
- albertelli
- alberti
- alberti_leandro
- alberti_tommaso
- albini
- albinoni
- albori_della_vita_italiana
- alcott
- aleardi
- alfa
- alfieri
- algarotti
- ali
- alighieri
- alighieri_jacopo
- allen
- aloysius
- amabile
- amalteo
- amari
- amati
- ambrogini
- amidei
- amodeo
- andersen
- anderson
- andrea_da_barberino
- andreis
- angiolieri
- angiolini
- anile
- anonimo
- antiquarie_prospettiche_romane
- antoccia
- antona_traversi
- antonelli
- appelius
- apuleius
- aragona
- arbib
- archinti
- arenskij
- aretino
- ariosto
- aristoteles
- armaroli
- aroldi
- arouet
- arrhenius
- arrieta
- arrighi
- arrigoni
- arsinov
- artom
- artusi
- atlante
- auber
- audran
- auto_da_fe_in_bologna
- avancini
- azeglio
- bacci
- baccini
- bacci_peleo
- bach
- bachi
- bachi_riccardo
- bachofen
- bach_carl_philipp_emanuel
- bach_johann_bernhard
- bach_johann_ludwig
- bach_wilhelm_friedemann
- bacigalupo
- badia_y_leblich
- baffo
- bakunin
- balakirev
- balbo
- balbo_italo
- baldacci
- balsamo
- balzac
- balzani
- banchieri
- bandello
- bandi
- baratono
- baratono_adelchi
- barbagallo
- barbaranelli
- barbarani
- barbarich
- barberini
- barbiera
- barbieri
- barbieri_francisco
- barbusse
- barella
- bargiacchi
- baricelli
- barla
- barni
- barrie
- barrili
- bartok
- bartoli
- bartoli_daniello
- barzini
- basile
- bassano
- bassano_anthony
- bastianelli
- baudelaire
- baunard
- bazzero
- bazzoni
- becattini
- beccari
- beccaria
- beccaria_antonella
- beckford
- beethoven
- belgioioso
- belgiojoso
- bellacchi
- bellani
- belli
- bellini
- belloc_lowndes
- bellone
- belo
- beltrame
- beltramelli
- bembo
- benaglio
- benamozegh
- benco
- benco_delia
- benedetti
- benelli
- beolco
- berchet
- berchet_guglielmo
- berg
- berlioz
- bernard
- bernardino_da_siena
- berneri
- berneri_camillo
- berneri_maria_luisa
- berni
- bersezio
- bertacchi
- bertacchi_cosimo
- bertelli
- berti
- bertinetti
- bertini
- bertola
- bertoni
- bertoni_brenno
- bertoni_luigi
- berwald
- besana
- bestiario_moralizzato
- betteloni
- betti
- bettinelli
- bettoni
- bevilacqua
- beyle
- bhagavad_gita
- biagi
- bianchi
- bianchi_giovini
- bianco
- bianconi
- bianconi_giovanni_lodovico
- bibbia
- bibbiena
- biber
- biffoli
- binazzi
- bini
- biografie_e_ritratti_d_illustri_siciliani
- bisciola
- bisi
- bizet
- bizzarri
- bizzozero
- blackwood
- blake
- blanch
- blanchard
- blaserna
- boccaccio
- boccalini
- boccardi
- boccardo
- boccherini
- bocchi
- bodrero
- boerio
- boghen_conegliani
- boiardo
- boieldieu
- boine
- boito
- boito_a
- bolza
- bon
- bonacini
- bonaparte
- bonarelli
- bonatelli
- bonaventura
- bonaventura_enzo
- bond
- bonfadini
- bonghi
- bonizzi
- bonola
- bonomo
- bonvesin_de_la_riva
- bordenave
- borgese
- borgese_giuseppe
- borghi
- borghi_armando
- borodin
- borri
- bortolotti
- boschetti_alberti
- boscovich
- bosio
- bossi
- botta
- bottazzi
- bottero
- bouchardy
- bourcet
- bourdet
- bouvier
- bovio
- bovio_libero
- bozzano
- bozzini
- bracco
- brahms
- brancaccio
- brera
- bresadola
- breton
- brocchi
- brofferio
- broglio
- bronte
- bronzino
- bruch
- bruckner
- bruna
- brunelli
- brunetti
- bruni
- bruni_giuseppe
- bruno
- brusoni
- bufardeci
- buia
- buonaiuti
- buonarroti
- buonarroti_il_giovane
- buoninsegni
- buozzi
- burchiello
- burckhardt
- burke
- burnaby
- burroughs
- burzio
- buschi
- busetto
- busoni
- butti
- buxtehude
- buzzanca
- byrne
- byron
- caccianiga
- cacciatore
- caccini
- cafiero
- cagna
- cagni
- cajkovskij
- calandra
- calcagno
- caldarella
- calestani
- calvo
- calza
- camillo
- camis
- cammarano
- camoes
- campana
- campanella
- campolonghi
- campra
- canestrini
- canestrini_alessandro
- canina
- cannabich
- cannizzaro
- cantalupo
- cantoni
- cantoni_giovanni
- canto_gregoriano
- cantu
- capasso
- capefigue
- capella
- capocci
- capparoni
- capponi
- capranica
- caprile
- capuana
- carabellese
- caracciolo
- caracciolo_enrichetta
- carafa_capecelatro
- carcano
- cardano
- cardile
- carducci
- carlyle
- carmina_burana
- carnevali
- carocci
- carpenter
- carrera
- carroll
- carubia
- casadei
- casanova
- casas
- cassini
- castelli
- castelli_david
- castelnuovo
- castelvetro
- casti
- castiglione
- castiglioni
- catalani
- caterina_da_siena
- cather
- cattaneo
- cava
- cavalcanti
- cavallotti
- cavara
- caversazzi
- caviglia
- cefali
- celesia
- cellini
- celoria
- cena
- cenni
- cennini
- cerlone
- cernysevskij
- cerro
- cervantes
- cervesato
- cesarotti
- cesi
- chabrier
- chanson_de_roland
- chapi
- charpentier
- chaucer
- chausson
- chelli
- cherubini
- cherubini_eugenio
- chesterton
- cheyney
- chiabrera
- chiara
- chiarelli
- chiaretti
- chiarini
- chiesa
- chigi
- chiocchetti
- chiosso
- chiurlo
- chopin
- christiansen
- chueca
- ciaceri
- ciamician
- ciampoli
- cian
- ciano
- cicero
- cicogna
- cielo
- cifra
- cimarosa
- cinelli
- cipriani
- cittadella
- claps
- clarke
- clementi
- club_alpino_italiano
- cocchi
- codemo
- coffa_caruso
- coglitore
- colagrossi
- colajanni
- coleridge
- collenuccio
- colletta
- collins
- collodi
- colombe
- colombo_fernando
- colombo_michele
- colonna
- colonna_vittoria
- colorni
- columba
- cominelli
- compagni
- compagnia_del_mantellaccio
- comparetti
- confucius
- contessa_lara
- conti
- coperario
- coppi
- corano
- corbino
- cordelia
- corelli
- coresio
- corio
- cornaro
- cornelius
- cornoldi
- corradini
- cortesi
- cosmi
- cossa
- costa
- costa_andrea
- coster
- couperin
- crawford
- crawford_morris
- cremonese
- crispi
- croce
- crocella
- croce_benedetto
- croce_enrico
- cronica_vita_di_cola_di_rienzo
- cucca
- cummins
- cuneo
- cuoco
- cuomo
- curiel
- curti
- curti_pier_ambrogio
- cusani
- cyrano_de_bergerac
- dadone
- dall_ongaro
- dalmasso
- dandrieu
- danti
- darwin
- darwin_erasmus
- daudet
- dauli
- da_ponte
- da_porto
- da_verona
- debay
- debenedetti
- debussy
- deledda
- delibes
- delius
- della_casa
- della_chiesa
- della_porta
- della_seta
- della_valle
- della_valle_pietro
- delpino
- del_lungo
- del_lungo_carlo
- dering
- desanctis
- descalzo
- descartes
- descuret
- despres
- devienne
- dewey
- de_amicis
- de_angelis
- de_astis
- de_blasio
- de_boni
- de_bosis
- de_cesare
- de_cleyre
- de_filippi
- de_foe
- de_franchi
- de_gamerra
- de_giovanni
- de_gubernatis
- de_marchi
- de_maria
- de_orestis
- de_paoli
- de_pellegrini
- de_pretto
- de_quincey
- de_roberto
- de_rubris
- de_ruggiero
- de_sanctis
- de_vries
- diabelli
- diamante
- dickens
- diderot
- difensore_degli_ebrei
- dini
- dito
- dittersdorf
- di_blasi
- di_genio
- di_giacomo
- di_giovanni
- di_giovanni_alessio
- di_grazia
- di_monaco
- di_san_giusto
- dolce
- domenichi
- donati
- donaver
- doni
- donizetti
- dorso
- dossi
- dostoevskij
- douhet
- doyle
- draeseke
- driesch
- drigo
- drosso
- ducati
- dukas
- dumas
- dunant
- duparc
- durante
- du_mage
- dvorak
- d_albert
- d_ambra
- d_ancona
- d_andrea
- d_annunzio
- d_arzo
- d_emilio
- d_india
- eco
- economisti_del_cinque_e_seicento
- eisner
- electronic_frontier_foundation
- elgar
- elia
- emanuelli
- emerson
- emiliani_giudici
- emma
- emmanuel
- engels
- enriques
- epictetus
- epicurus
- erasmus_roterodamus
- eredia
- ermacora
- errante
- errera
- euclides
- fabbri
- fabiani
- fabula_de_etc
- faldella
- fanciullacci
- fanciulli
- fanfani
- fantazzini
- fantoni
- farga
- fargion
- farina
- farinelli
- farnaby
- faure
- favaro
- fazello
- federici
- fernandez_caballero
- fernandez_guardia
- ferrabosco_il_giovane
- ferrari
- ferrari_carlotta
- ferrari_giuseppe
- ferrari_giuseppe_1720
- ferrari_paolo
- ferrari_pietro
- ferrari_pio_vittorio
- ferrari_severino
- ferrer
- ferrero
- ferretti
- ferri
- ferrieri
- ferri_dina
- ferri_giustino
- ferroni
- ferruggia
- feuerbach
- fiacchi
- fibich
- figner
- figuier
- filicaia
- filippi
- fillak
- filopanti
- finella
- fioravanti
- fioretti_di_san_francesco
- fiore_di_leggende_cantari_antichi_etc
- fiorini
- firenzuola
- flammarion
- flaubert
- fletcher
- flies
- florenzi
- florio
- flotow
- fogazzaro
- folengo
- folgore
- fontana
- fontanarosa
- fontane
- fontefrancesco
- fontenelle
- formichi
- fornaciari
- forteguerri
- fortis
- foscolo
- fraccacreta
- fracchia
- france
- francesco_d_assisi
- franchetti
- franck
- franco
- frari
- freud
- frezzi
- frugoni
- fucini
- fugassa
- funck_brentano
- gabetti
- gabrieli
- gabrieli_giovanni
- galassi
- galiani
- galilei
- gallaccini
- galleani
- galleria_palatina
- gallina
- gallo
- galuppi
- gamberi
- gandhi
- ganot
- gargiulo
- garibaldi
- garrone
- gatti
- gautier
- geminiani
- gentile
- gentile_iginio
- gerard
- geremicca
- gerli
- german
- gershwin
- gervasoni
- gherardi
- ghersi
- ghislanzoni
- ghisleri
- giaccani
- giacometti
- giacosa
- giamboni
- gianelli
- giannone
- gibbon
- gibellini
- gide
- gigli
- giglioli
- gille
- gilles
- ginzburg
- gioberti
- giolitti
- giordana
- giordano
- giornale_per_i_bambini
- giostra_delle_virtu_e_dei_vizi
- giovannetti
- giovannitti
- giovio
- giraud
- giraudoux
- giretti
- giribaldi
- giuseppe_da_forio
- giusta_idea
- giusti
- glazunov
- glinka
- gluck
- gobetti
- goethe
- gogol
- goldoni
- goldsmith
- golgi
- goll
- gomes
- gonin
- gori
- gori_pietro_1854_1930
- gorkij
- gossec
- gothein
- gounod
- gozzano
- gozzi
- gozzi_gasparo
- graf
- gramsci
- granados
- grande
- grandi
- grassi
- grasso
- grave
- gray
- graziani
- gregorovius
- gretry
- grieg
- grimaldi
- grimm_jakob
- grippa
- grossi
- grossi_vincenzo
- groto
- guadagnoli
- gualandris
- gualdo
- guardione
- guareschi
- guarini
- guelfi
- guerrazzi
- guerrini
- guglielminetti
- guglielmotti
- guicciardini
- guidetti
- guidi
- guidiccioni
- guidi_michelangelo
- guiducci
- gulli
- guy
- haeckel
- haendel
- hamsun
- harding
- hasse
- hauptmann
- hawthorne
- haydn
- heron
- herschel
- hewlett
- heywood
- hichens
- historia_di_papa
- holborne
- holst
- homerus
- hubay
- huch
- hugo
- hummel
- humperdinck
- huxley
- iacopone_da_todi
- iacopo_da_sanseverino
- iberti
- ibn_gubayr
- ibn_miskawayh
- ibsen
- imbriani
- indy
- ingrassia
- innocentius_papa_12
- intorcetta
- invernizio
- ippolita_comunita_di_scriventi
- ippolitov_ivanov
- issel
- istoria_critica
- italia
- jacobsen
- james
- janacek
- jarro
- jatta
- jeans
- jefferson
- jenna
- jennings
- jerome
- johansson
- johnson
- joinville
- jolanda
- joplin
- jovine
- joyce
- juvalta
- kaffka
- kahn
- kalevala
- kalidasa
- kant
- karr
- keynes
- kipling
- kleist
- kollo
- komzak
- kovalevskaja
- kropotkin
- labriola
- ladenarda
- lady_gregory
- lafargue
- lagerlof
- lalande
- lalli
- lalo
- lancillotti
- lando
- landriani
- lanzalone
- lao_tzu
- lasca
- laser
- lasso
- latini
- lattes
- lattes_dante
- lavater
- lawrence
- lazzarelli
- lazzaretti
- lazzeri
- la_boetie
- la_fontaine
- la_lumia
- leetherland
- leggenda_di_tristano
- legouve
- lehar
- leibniz
- leitgeb
- lemery
- lemonnier
- lenti_boero
- leonardo
- leoncavallo
- leoni
- leopardi
- leroux
- lesca
- lessig
- lessona
- lettera_a_diogneto
- levati
- levi
- levi_adolfo
- levi_giulio_augusto
- lewis
- libri_piu_letti
- libro_della_cucina
- liebig
- liesegang
- liguria
- linati
- lipparini
- lippi
- liszt
- littre
- lizio_bruno
- ljadov
- lleo
- locatelli
- lockyer
- lodi
- lomazzo
- lombardini
- lombroso
- lombroso_gina
- london
- longo
- longus_sophista
- lopez
- lorentz
- lorenzo
- lorenzoni
- lori
- loria
- lortzing
- lo_valvo
- lucatelli
- lucchesini
- lucianus
- lucini
- lucretius
- luigini_federico
- luini
- lully
- luna
- lupo
- lusitania
- luther_blissett
- luzio
- macaulay
- maccrie
- machiavelli
- mackay
- maes
- maeterlinck
- maffei
- magalotti
- maggi
- mahler
- maineri
- maistre
- malamani
- malatesta
- malinverni
- malon
- malpassuti
- mameli
- mamiani
- mannarino
- manni
- manno
- mannu
- mantegazza
- manucci
- manzoni
- marais
- marcelli
- marcello
- marchand
- marchesani
- marchesa_colombi
- marchetti
- marchi
- marconi
- maresca
- mariani
- marinelli
- marinetti
- marino
- mario
- marrama
- marselli
- marsili
- martello
- martineau
- martinelli
- martinelli_vincenzo
- martinetti
- martini
- martini_ferdinando
- martoglio
- martucci
- marugi
- marx
- mascagni
- masci
- masi
- massarani
- massenet
- massimi
- mastriani
- mastro_titta
- mattei
- matteucci
- mattirolo
- maupassant
- mazzarino
- mazzini
- medici
- medici_ferdinando_i
- medici_lorenzino
- mehul
- meli
- melville
- mendelssohn
- menghini
- mengozzi
- merlini
- merlino
- messa_di_requiem
- messina
- metastasio
- meyer
- meyerbeer
- meyrink
- micanzio
- michaelis
- michel
- michelstaedter
- mieli
- milani
- mill
- mille_e_una_notte
- milton
- mioni
- mirbeau
- misasi
- misefari
- moderata_fonte
- modigliani
- molinari
- molnar
- mommsen
- monchablon
- mondaini
- moneta
- mongai
- mongitore
- monicelli
- monnier
- montanelli
- montesquieu
- montessori
- monteverde
- monteverdi
- monti
- monti_achille
- montpensier
- moore
- morandi
- morandi_carlo
- morando
- morasso
- more
- moresco
- moretti
- morra
- morris
- morselli
- morselli_ercole
- mosca
- moscardelli
- mosso
- mozart
- mozzoni
- mudge
- mulazzi
- mule
- mule_bertolo
- munthe
- mura
- muratori
- muratori_lodovico
- murger
- murri
- musorgskij
- mussolini
- musumeci
- muzzi
- nagy
- nardini
- narrazione_critico_storica_etc
- natale
- navigazione_di_san_brandano
- nazioni_unite
- neera
- negri
- negri_ada
- negri_francesco
- negri_gaetano
- nencioni
- nerucci
- nettlau
- nibby
- nibelunghi
- niccolini
- nicolai
- nicolaus_cusanus
- nielsen
- nieri
- nietzsche
- nievo
- nivers
- nobili
- nordau
- nordhoff
- norsa
- nota
- notari
- notturno_napoletano
- novacek
- novaro
- novaro_mario
- novatore
- novella_del_grasso_legnajuolo
- novelle_cinesi
- novelle_indo_americane
- novelle_italiane_dalle_origini_al_cinquecento
- novellino
- nucera_abenavoli
- nuovi_misteri_del_chiostro_napoletano_etc
- offenbach
- ojetti
- olper_monis
- omodeo
- onesto
- oppenheim
- orestano
- oriani
- orsi
- orsini
- ortolani
- pachelbel
- pacini
- pacioli
- padoa
- padula
- pagani
- paganini
- pagliaro
- pailleron
- paisiello
- palazzi
- paleologue
- palladio
- pallavicini
- pallavicino
- palli_bartolommei
- palma
- palmeri
- palomba
- pananti
- pani
- pannocchieschi
- panzacchi
- panzini
- paolieri
- pareto
- parini
- paris
- parlatore
- parmeggiani
- pascal
- pascal_carlo
- pascarella
- pascoli
- pasinetti
- pasolini
- paterno
- pausanias
- pavese
- peano
- pellico
- pellizzari
- penzig
- pepoli
- percoto
- pergolesi
- perlman
- perodi
- perrault
- petrarca
- petrocchi
- petruccelli_della_gattina
- piave
- piazza
- piazza_antonio
- piazzi
- pico_della_mirandola
- pierantoni_mancini
- pieri
- pierne
- pigafetta
- pignata
- pinamonti
- pinchetti
- pindemonte
- pino
- pintor
- pinza
- pioda
- piola
- pirandello
- pisacane
- piscel
- pissilenko
- pitre
- piva
- pizzagalli
- pizzigoni
- pizzigoni_giuseppina
- pizzirani
- planche
- plato
- plinius_caecilius_saecundus
- podesta
- podrecca
- poe
- poli
- polidori
- polidori_francesco
- polimanti
- poliziano
- polo
- polybius
- pompilj
- ponchielli
- popper
- porati
- porta
- pov_ray_team
- pozzi
- pozzi_antonia
- praetorius
- praga
- praga_marco
- prati
- previati
- prevost
- prose_e_poesie_giapponesi
- proudhon
- proust
- prunas
- puccini
- puini
- pulci
- purcell
- purgotti
- puskin
- puviani
- quadrio
- quel_libro_nel_cammino_della_mia_vita
- quevedo
- rabelais
- rabizzani
- raccolta_di_lettere_ecc
- racconti_popolari_dell_ottocento_ligure
- rachmaninov
- racquet
- radcliffe
- raffaello_sanzio
- raga
- ragazzoni
- rajberti
- rajna
- ramazzini
- rameau
- ramusio
- randi
- ranieri
- rapisardi
- rastrelli
- ravagli
- ravel
- razzaguta
- reclus
- redi
- regaldi
- regalia
- reger
- reghini
- regina_di_luanto
- regnani
- regno_d_italia_1805_1814
- reinecke
- relazione_dell_atto_della_fede_etc
- renan
- renier_michiel
- rensi
- repubblica_romana_1849
- respighi
- retif_de_la_bretonne
- reuze
- reyer
- rezzonico
- ricchi
- ricchieri
- ricci
- ricci_paterno_castello
- ricci_umberto
- riccoboni
- righetti
- righi
- rignano
- rilke
- rimatori_siculo_toscani_del_dugento
- rime_dei_memoriali_bolognesi
- rimini
- rimskij_korsakov
- rinaldini
- ringhieri
- ripa
- ripamonti
- rizzatti
- roberti
- robida
- rocca
- roccatagliata_ceccardi
- rocca_enrico
- rocco
- roggero
- rohlfs
- rolando
- romagnoli
- romagnoli_augusto
- romani
- roma_e_la_opinione_etc
- romberg
- romussi
- roncaglia_gino
- rosa
- rosadi
- rosa_daniele
- rose
- rosetti
- rosi
- rosmini
- rosselli_carlo
- rosselli_nello
- rossi
- rossini
- rossi_emanuele
- rossi_giovanni
- rostand
- rousseau
- roussel
- rovani
- rovetta
- rubinstejn
- ruffini
- ruffini_francesco
- russo
- russolo
- ruzzante
- ryner
- sabatini
- sabatini_rafael
- sabbadini
- sacchetti
- sacchetti_roberto
- sacchi
- sacheli
- sacher_masoch
- saffi
- saffi_antonio
- saint_evremond
- saint_saens
- salanitro
- salfi
- salgari
- salimbene_da_parma
- sallustius
- salucci
- saluzzo_roero
- sangiorgio
- sannazaro
- santucci
- sanudo
- sanvittore
- sarasate
- sardegna_regno
- saredo
- sarno
- sarpi
- satta
- savarese
- savasta
- savinio
- savio
- savioli
- savi_lopez
- savonarola
- scarfoglio
- scarlatti
- scarpetta
- scarpetta_maria
- scartabellati
- schein
- schiaparelli
- schiavini
- schicchi
- schiller
- schioppa
- schmid
- schmidt
- schopenhauer
- schubert
- schumann
- schutz
- schwarz
- scilla
- scina
- scott
- scrofani
- scuto
- sebastian
- secchi
- sella
- seneca
- serafini
- serafino_aquilano
- serao
- sercambi
- serena
- serge
- sergi
- serra
- servi
- settembrini
- sfinge
- sforza
- shakespeare
- shaw
- shelley
- sicilia
- siciliani
- sidrac
- sienkiewicz
- sigonio
- siliprandi
- silva
- simpson
- sinding
- sismondi
- skrjabin
- slataper
- smetana
- sobrero
- sobrero_mario
- socci
- soler
- solera
- solmi
- solovev
- sommerfeld
- sonzogno
- sophocles
- sorbelli
- spampanato
- spaventa
- spaventa_filippi
- sperani
- speroni
- spinazzola
- spinelli
- spinoso
- spinoza
- spohr
- spontini
- stacpoole
- stael
- stampa
- statius
- stefanoni
- stein
- steiner
- stendhal
- stenhammar
- steno
- stephens
- sterne
- stevenson
- stewart
- stirner
- stoker
- storia_dei_paladini_di_francia
- storia_di_fra_michele_minorita
- stowe
- straparola
- strauss
- strauss_josef
- strauss_jr
- strauss_richard
- strenna_di_ascolti_per_il_natale
- stromboli
- suk
- sullivan
- supino
- suppe
- supplica_degli_stampatori_e_etc
- suzzara_verdi
- svendsen
- svevo
- swift
- sylos_labini
- synge
- szanto
- szymanowski
- tagore
- tanini
- tanini_alighiero
- tarabotti
- tarchetti
- targioni_tozzetti
- tartaglia
- tartini
- tartufari
- tassini
- tasso
- tassoni
- telemann
- teloni
- tempio
- tenca
- terentius
- tesoro_di_scienze_etc
- tessa
- testoni
- tettoni
- theuriet
- tholozan
- thomas
- thoreau
- thorpe
- thouar
- thovez
- thucydides
- tigri
- tilgher
- timmermans
- timpanaro
- tiraboschi
- titelouze
- tocco
- tolstoj
- tomei
- tommaseo
- torelli
- torelli_luigi
- torricelli
- tosco
- tosti
- tozzi
- traina
- trebbi
- treitschke
- trentin
- tresca
- trilussa
- trimmer
- troya
- tucci
- tumiati
- turco
- turgenev
- ubaldini
- uccellini
- uda
- ughetti
- ultimi_fatti_di_milano
- unesco
- unione_europea
- untersteiner
- urgnani
- vailati
- valera
- valery
- vallardi
- valles
- valletta
- valli
- valvason
- vannicola
- vanzetti
- varthema
- varvaro
- vasari
- vassallo
- vaticano
- venerandi
- venexiana
- veneziani
- venier
- veniero
- venosta
- venturi
- venturini
- venturi_adolfo
- verdi
- verdinois
- verdi_de_suzzara
- veresaev
- verga
- vergilius
- verne
- veronese
- verri_alessandro
- verri_pietro
- vertua
- vettori
- viaggi_di_gio_da_mandavilla
- viani
- vico
- vieuxtemps
- vigoni
- villa
- villabianca
- villani
- villani_matteo
- villari
- villiers_de_l_isle_adam
- vinci
- violante
- viotti
- viriglio
- viscnu_sarma
- vismara
- vitali
- vita_delitti
- vita_italiana_nel_cinquecento
- vita_italiana_nel_rinascimento
- vita_italiana_nel_risorgimento
- vita_italiana_nel_seicento
- vita_italiana_nel_settecento
- vita_italiana_nel_trecento
- vitruvius
- vivaldi
- vivante
- vivanti
- vives
- viviani
- viviani_raffaele
- vogue_melchior_de
- volin
- volpi
- volta
- voltaire
- volterra
- wagenaar
- wagner
- waldteufel
- wallace
- wallace_edgar
- wallace_lewis
- walpole
- wassermann
- weber
- wells
- wessely
- white_mario
- widmann
- wieniawski
- wilde
- wolf
- wolf_ferrari
- woolf
- world_wide_web_consortium
- wundt
- wu_ming
- wu_ming_1
- wu_ming_2
- wu_ming_5
- yambo
- yeats
- yriarte
- zagarrio
- zanazzo
- zandonai
- zanella
- zanghi
- zanotelli
- zavattero
- zena
- zhuang_zi
- zola
- zuccoli
-